6.2.7 Version 4.6.1
4.6.1 MetaDefender Email Security releaseRelease Date: April 15, 2019 |
MetaDefender Email Security 4.6.1 is a maintenance release focused on fixing issues and providing minor improvements. |
||||
New & improved |
|||||
Support for Data Loss Prevention results |
Email Security now utilizes MetaDefender Core's Data Loss Prevention results in its statistics, dashboard, etc. |
||||
|
Support for password protected documents |
Email Security now supports rescanning password protected Portable Document Format (.pdf) and Microsoft Office (.docx, etc,) document attachments, when Email Security is paired with MetaDefender Core version 4.14.3 or newer. Core 4.14.3 required Rescanning Portable Document Format and Microsoft Office documents is only supported when MetaDefender Core version 4.14.3 (or newer) is in use. For further details please read 4.7 Support for password protected attachments. |
||||
|
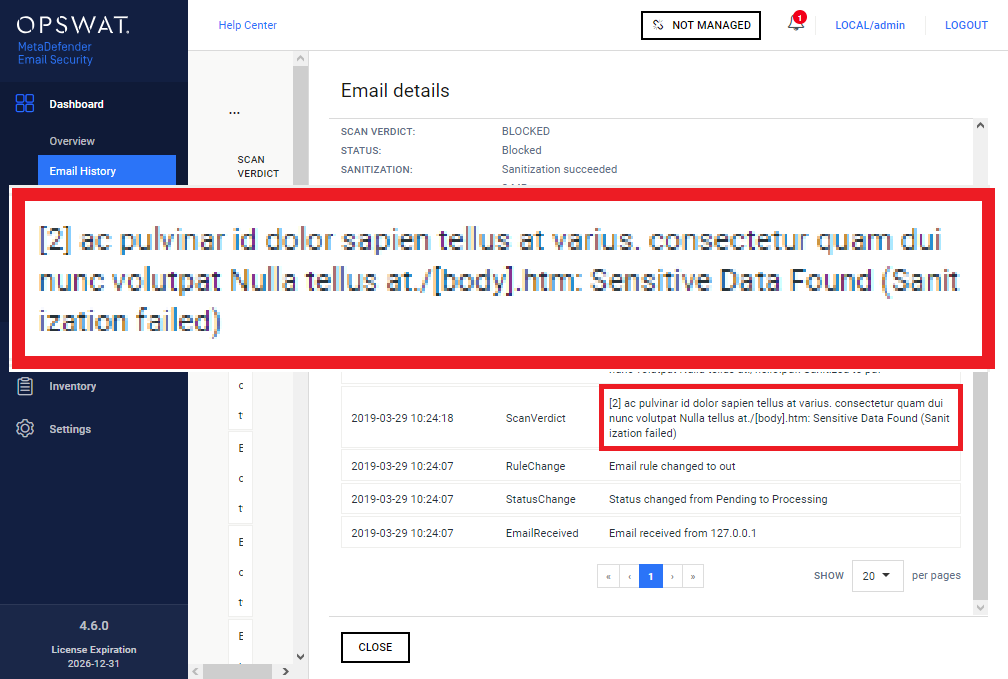
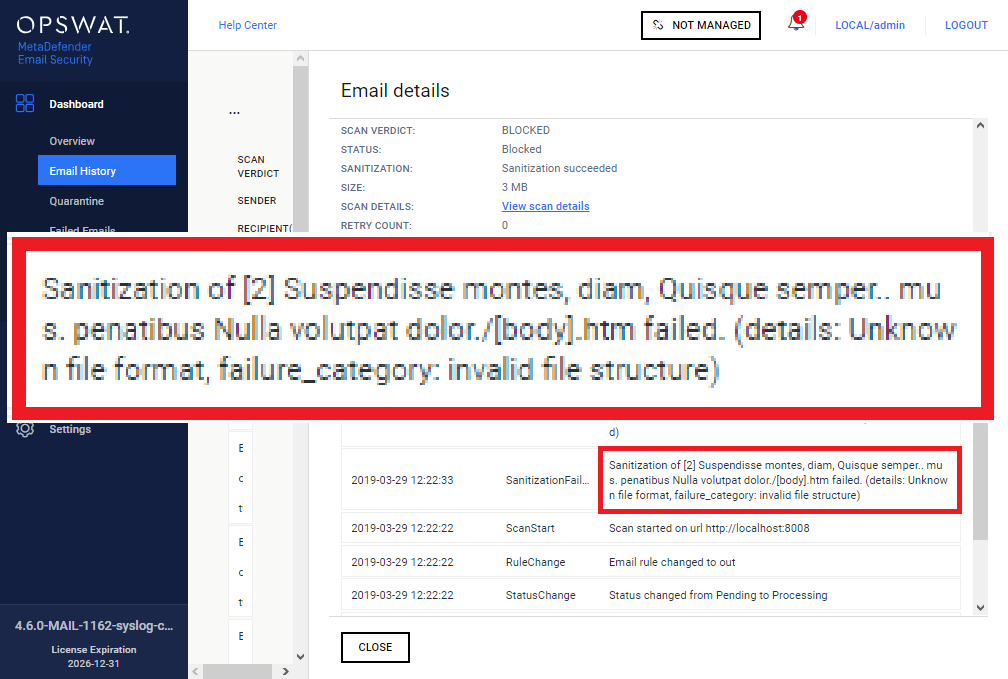
Provide details about sanitization failures |
Processing history and email alerts provide now more details about the reasons of sanitization failures.
|
||||
|
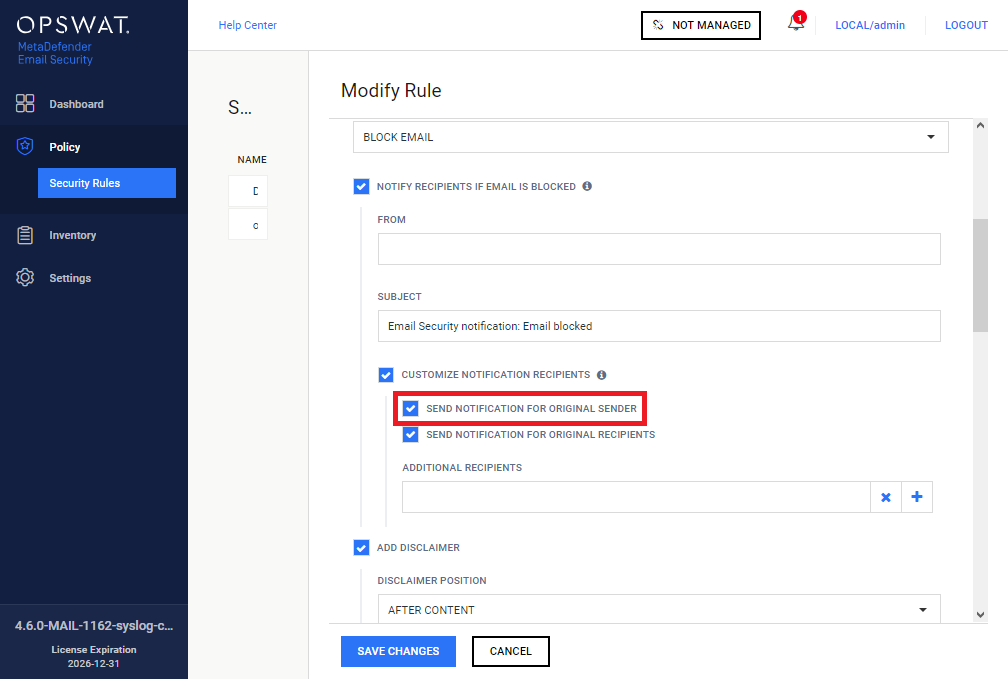
Notify sender on blocked outbound emails |
The sender is notified when the outbound email is blocked. This will allow the sender to provide the password (for a password protected document or archive) and have the email scanned before it is sent out the organization.
|
||||
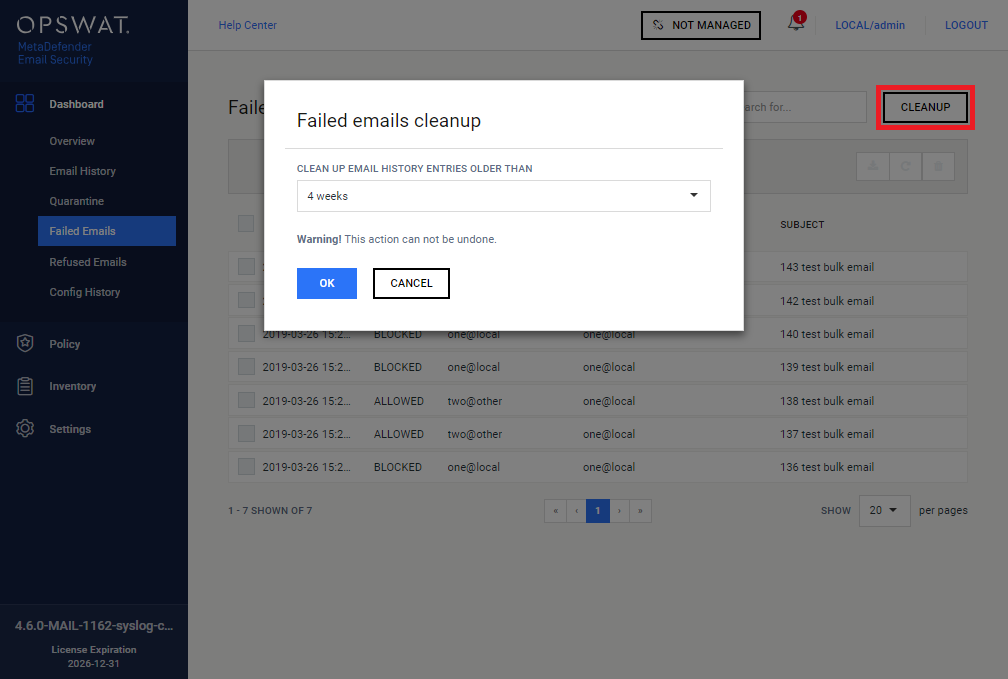
Cleanup functionality for Failed Emails |
Dashboard > Failed Emails now has a CLEANUP function. This function makes possible to delete certain failed emails that are older then the timeframe selected. |
||||
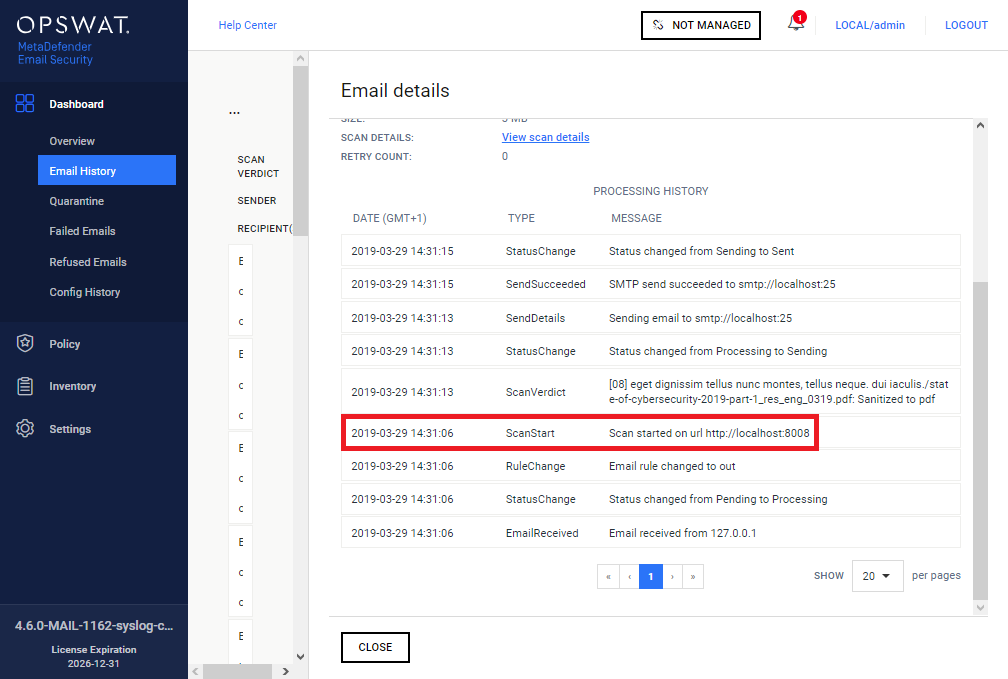
Scan start entry in processing histories |
Email details / PROCESSING HISTORY for Dashboard > Email History, Dashboard > Quarantine and Dashboard > Failed Emails now contains an entry logging when the email was sent for scanning to MetaDefender Core. This entry can help administrators to learn how much time of its processing an email spent in scanning, outside of Email Security. |
||||
|
Fixed |
|||||
Syslog syntax error in case of CEF logs |
When logging was set to Common Event Format (CEF), log messages were not valid according to the syslog syntax. |
||||
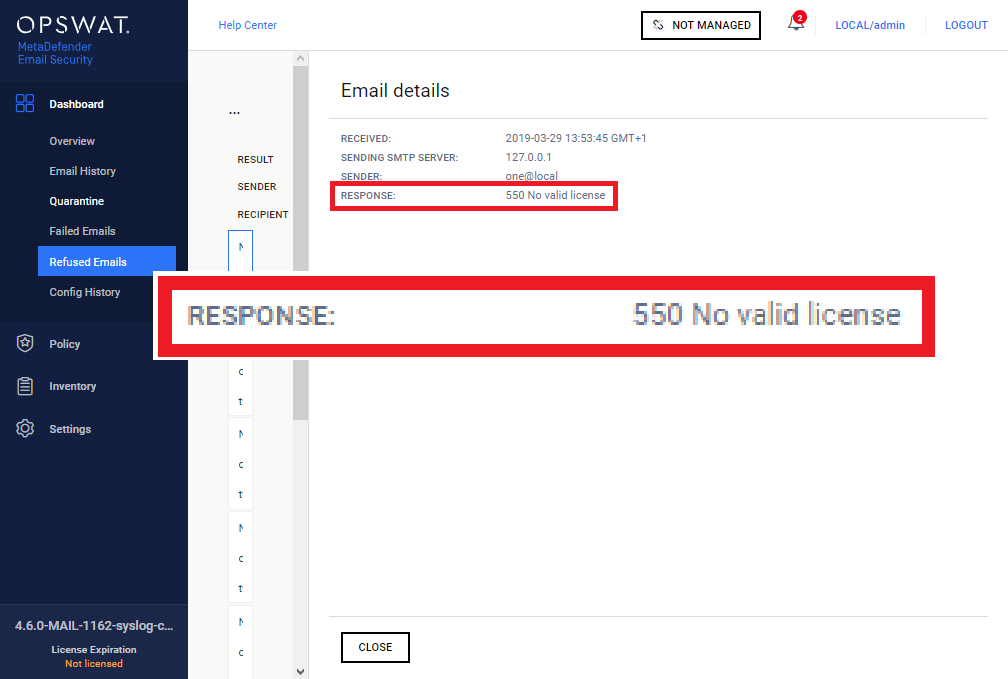
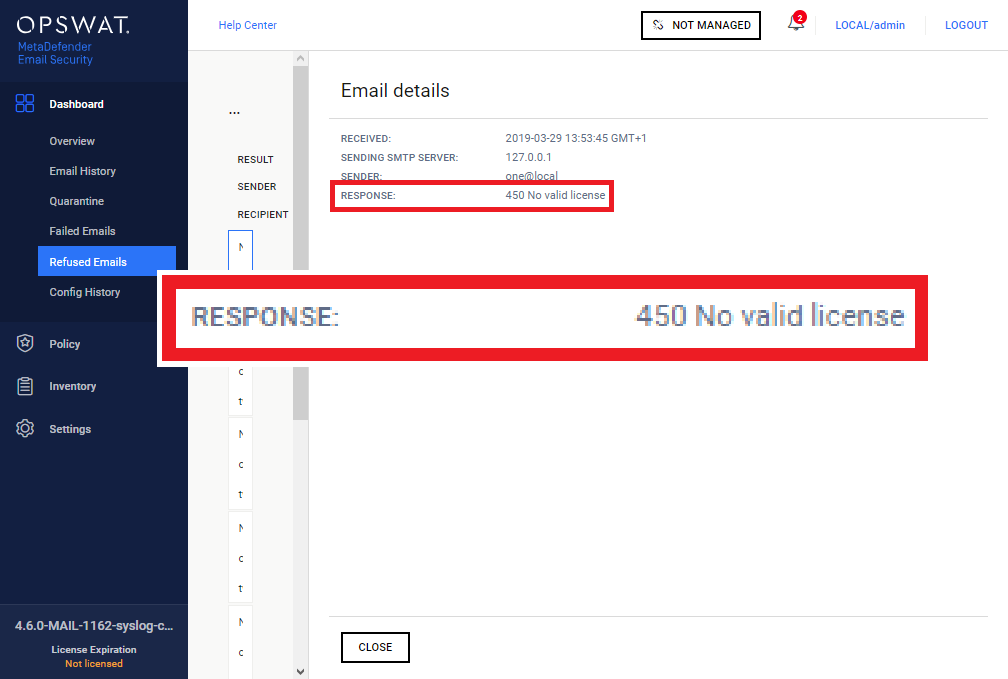
Wrong code reported for refused emails |
When an email was refused -due to unlicensed product, for example- with SMTP code 450, erroneously Email Security reported 550 in Refused Emails > Email details.
|
||||
Contact sharing invitations were corrupted |
Microsoft Exchange Server contact sharing invitations got corrupted in the finally delivered emails when Content Disarm & Reconstruction (CDR; Data Sanitization / DS) was enabled in the MetaDefender Core rule utilized by Email Security. |
||||
Allowed items appeared in quarantine reports |
Allowed (but otherwise quarantined; e.g. emails with sanitized attachments) items were included in quarantine reports even when quarantine reports were configured to contain blocked emails only. |
||||