5.6.1 Stand-alone PoC environment
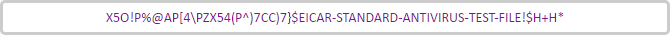
Design
Components
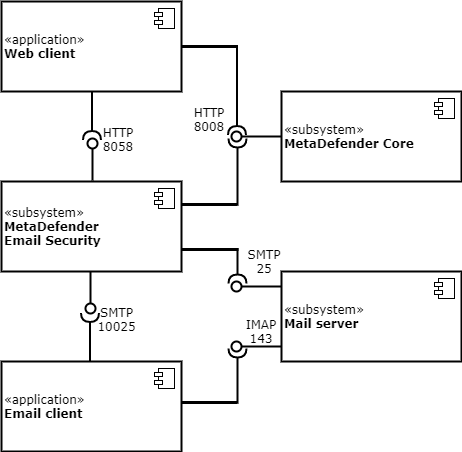
Traffic flow
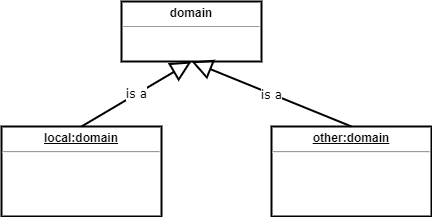
Domains
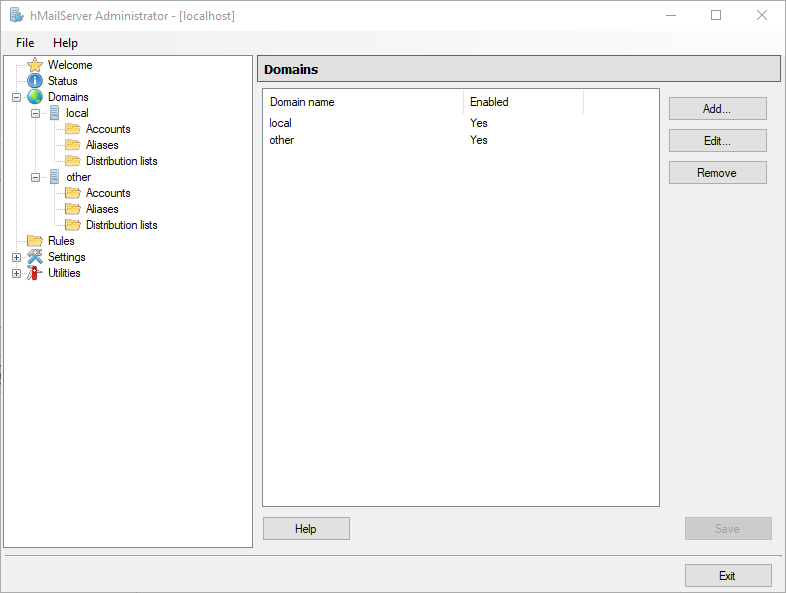
We will have two domains in the examples below:
-
the domain local as the organization internal domain, for inbound email traffic and
-
the domain other as the external domain, for outbound email traffic.
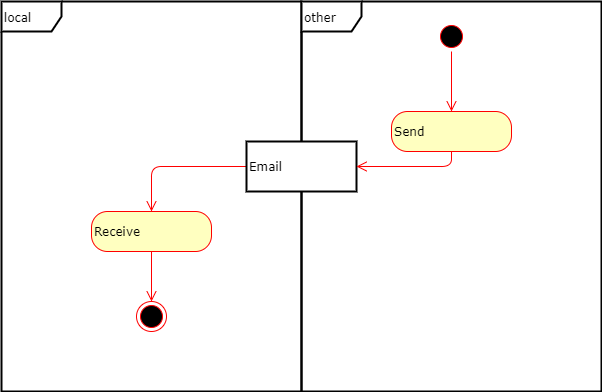
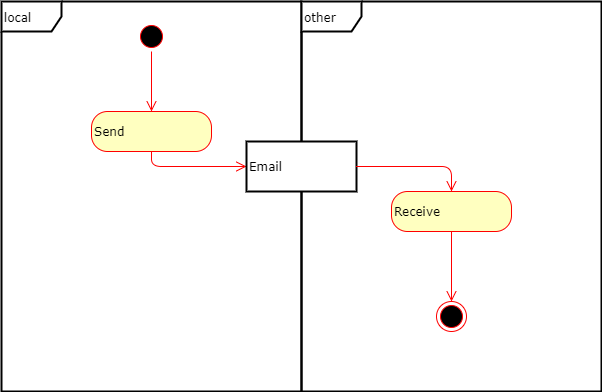
Direction
Inbound
Outbound
Prerequisites
Host
Any of the components above may be deployed to different, or to the same host.
In the examples of this page all components will be deployed to the same host, thus localhost or 127.0.0.1 will be used as host address.
Web client
Any web client that is supported by MetaDefender Core and MetaDefender Email Gateway Security can be used.
We assume that the web client is pre-installed on the host.
Email client
In the examples of this page Microsoft Mail will be used
We assume that the email client is pre-instaled on the host.
Mail server
In the examples of this page hMailServer will be used (https://www.hmailserver.com/).
MetaDefender Core and MetaDefender Email Gateway Security
The latest available version will be used.
Setup
MetaDefender Core
Install MetaDefender Core following the instructions in 1. Quick Start with MetaDefender Core.
hMailServer
Installation
|
Step |
Description |
Screenshot |
|
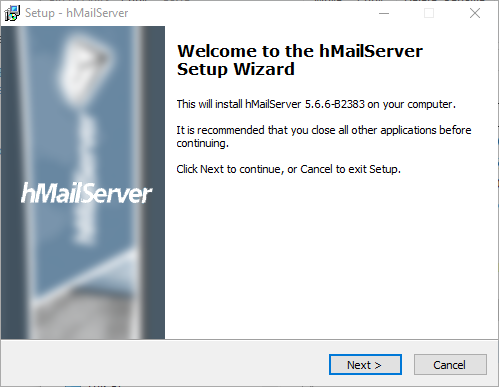
1 |
|
|
|
2 |
Launch the installer |
|
|
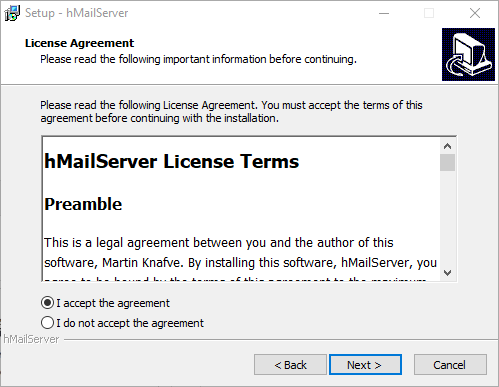
3 |
Accept the License Agreement |
|
|
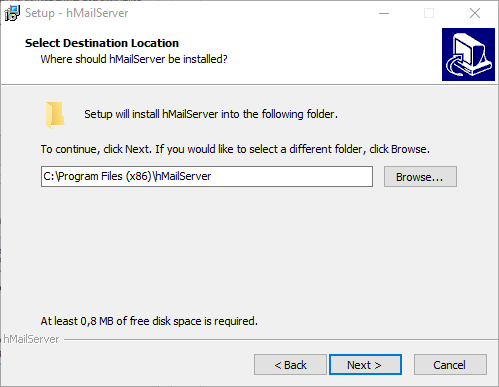
4 |
Select destination directory |
|
|
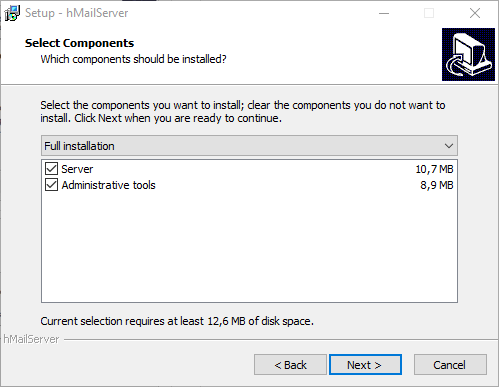
5 |
Select components. Do select both Server and Administrative tools |
|
|
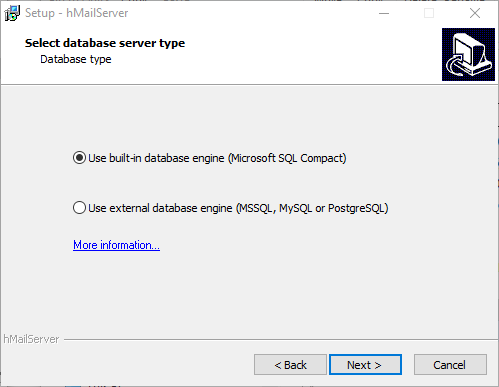
6 |
Select database type (default) |
|
|
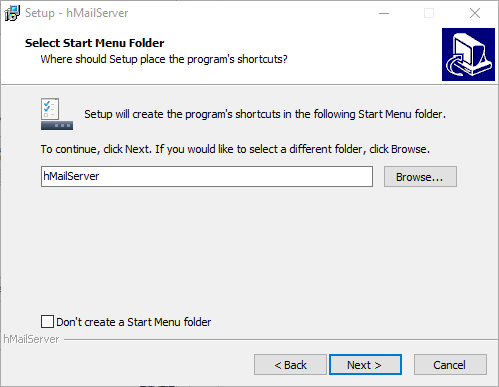
7 |
Specify Start Menu folder |
|
|
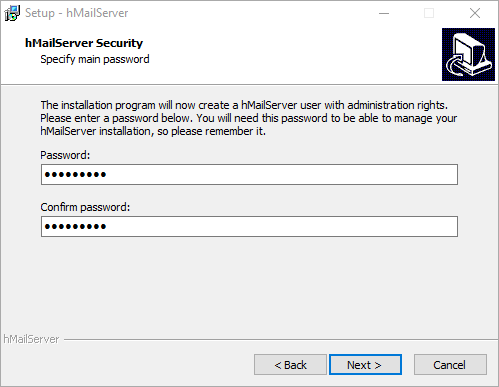
8 |
Create Administrator account |
|
|
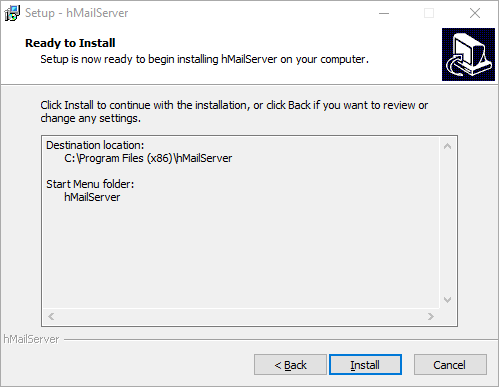
9 |
Finalize installation |
|
Configuration
|
Step |
Description |
Screenshot |
|
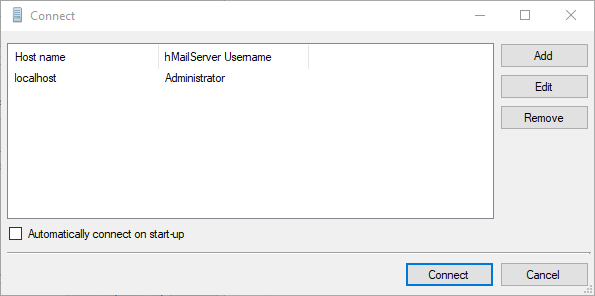
1 |
Start hMailServer Administrator Select the Administrator account and click Connect |
|
|
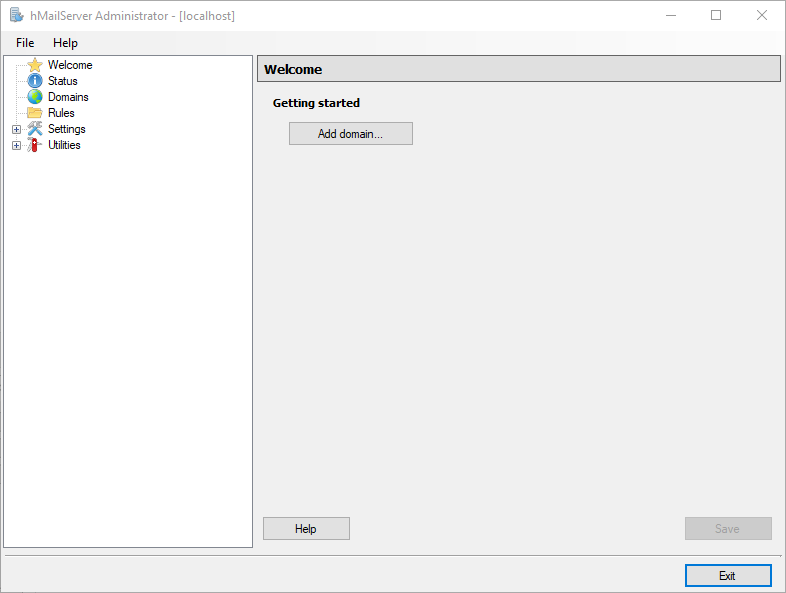
2 |
Click Add domain and start adding our two domains local and other according to the 149495854 |
|
|
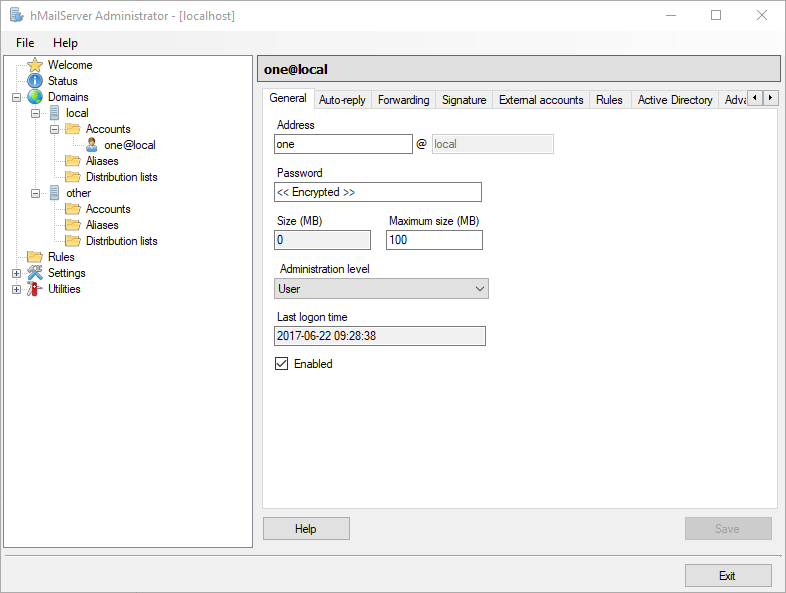
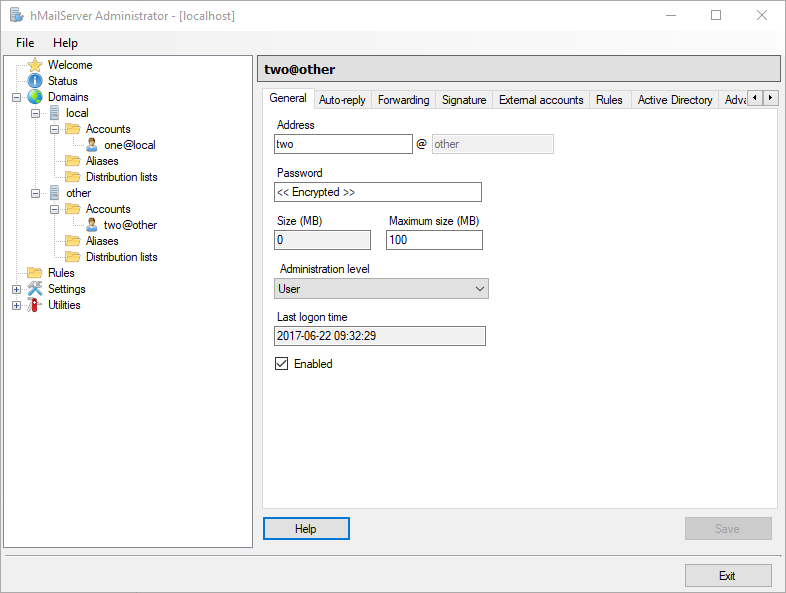
3 |
In each of local and other domains create one-one account for email sending and receiving one and two respectively:
|
|
MetaDefender Email Gateway Security
Installation and configuration
Install and configure MetaDefender Email Gateway Security following the instructions in 1 Quick start with MetaDefender Email Gateway Security.
Security rules
Modify the rules created in the previous section according to the following.
Inbound
|
Tab |
|
Filter |
Relay |
||
|
Field |
Direction |
Sender IP |
Recipient domain or address |
Server IP/Domain |
Port |
|
Value |
INBOUND |
blank |
.+@local |
127.0.0.1 |
25 |
Outbound
|
Tab |
|
Filter |
Relay |
||
|
Field |
Direction |
Sender IP |
Recipient domain or address |
Server IP/Domain |
Port |
|
Value |
OUTBOUND |
blank |
.+@.+ (or optionally .+@other) |
127.0.0.1 |
25 |
Email traffic redirection
Skip 1.6 Email traffic redirection as the appropriate settings will be configured with the email client.
Email client
The same email client will be the source and the final destination of emails. As a consequence it will receive emails from hMailServer and send emails towards MetaDefender Email Gateway Security.
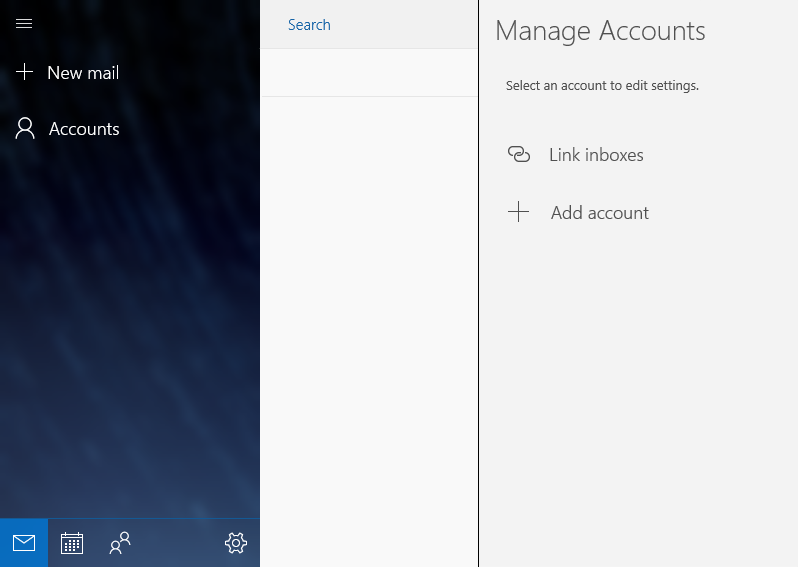
Configure the two accounts one and two in Microsoft mail:
|
Step |
Description |
Screenshot |
|
1 |
Click Accounts / Add account |
|
|
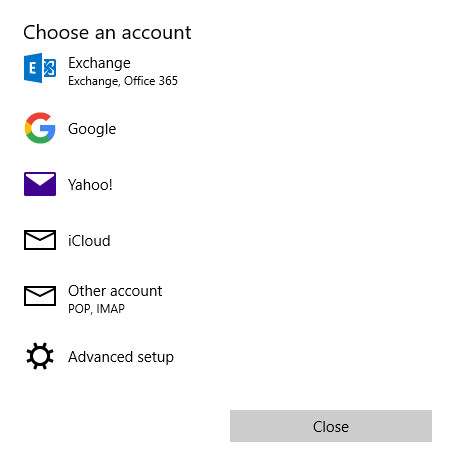
2 |
Select Advanced setup |
|
|
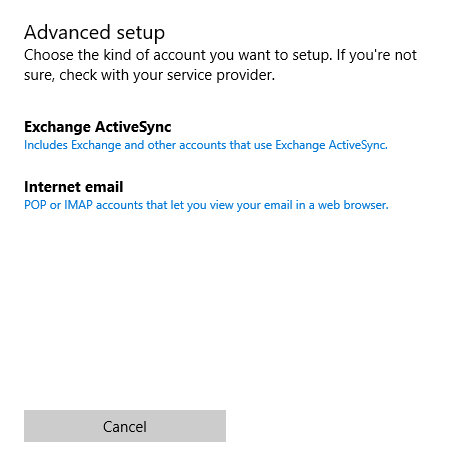
3 |
Select Internet email |
|
|
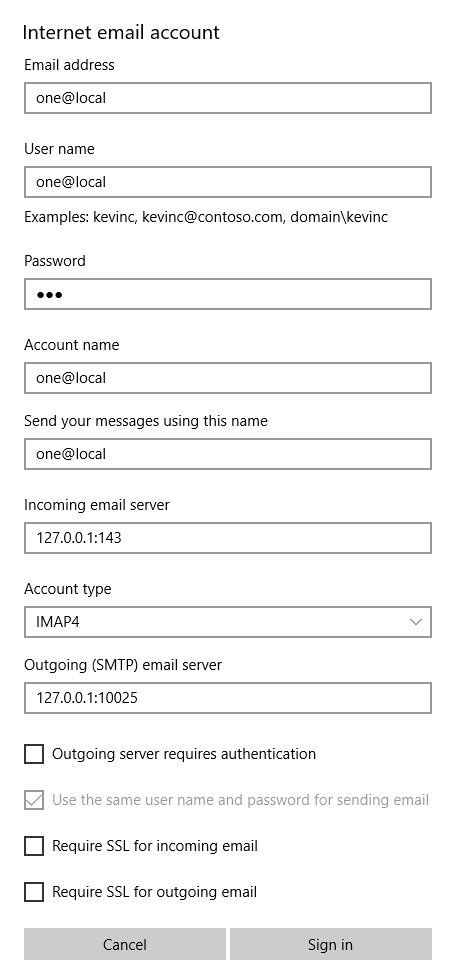
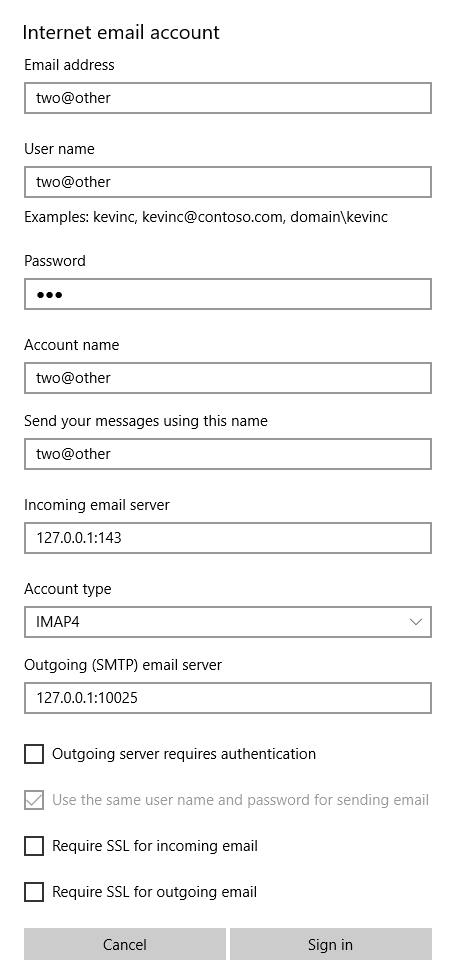
4 |
Configure the account one |
|
|
5 |
Repeat the previous step for the account two |
|
|
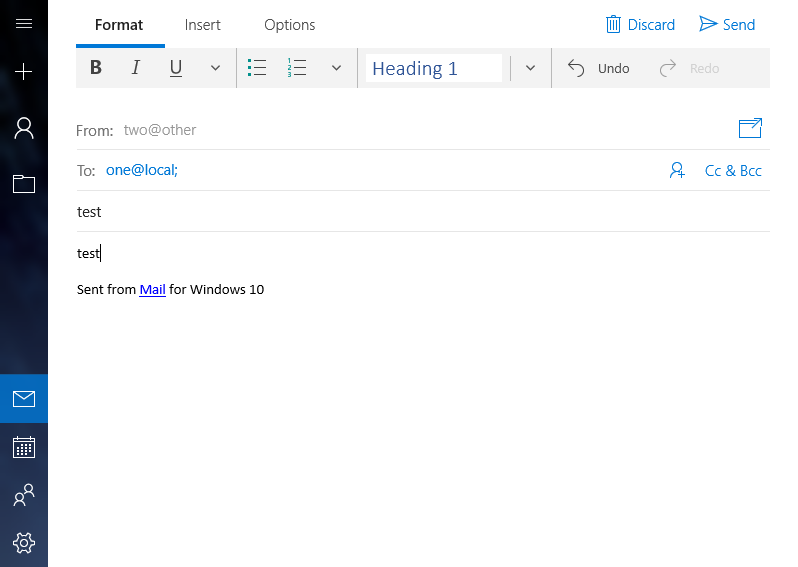
6 |
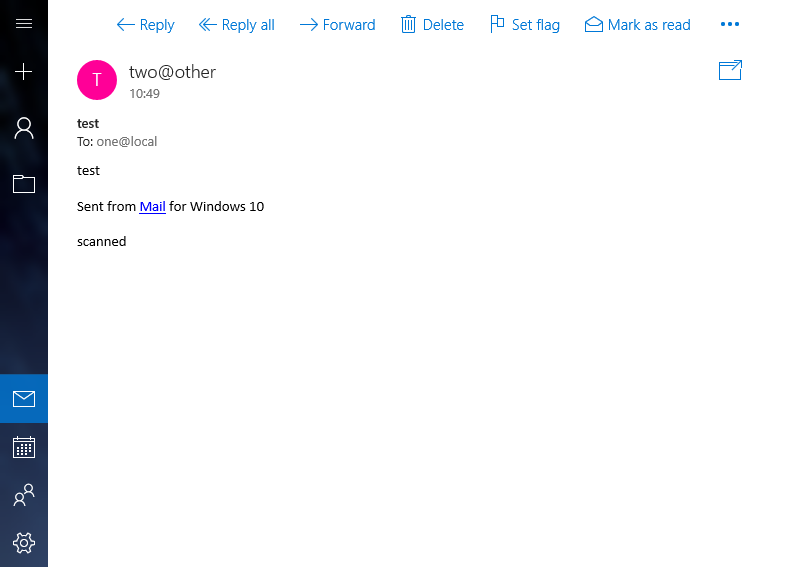
Send a test email |
|
|
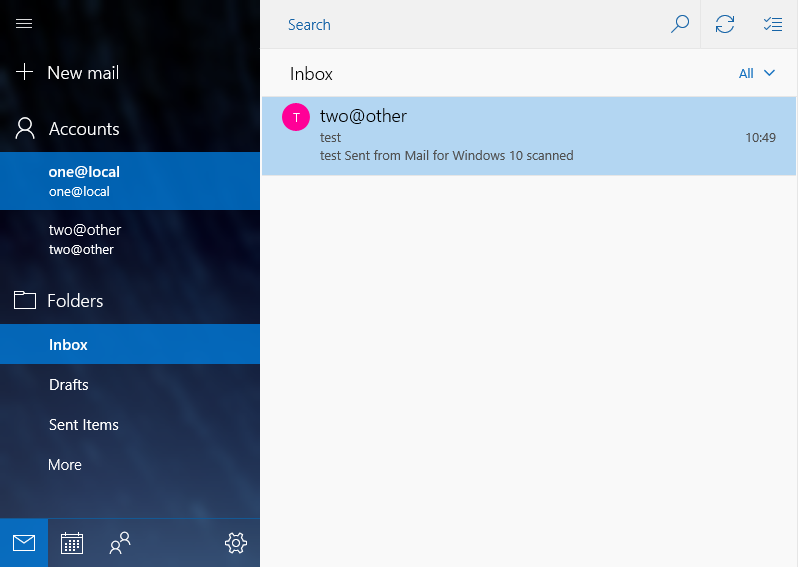
7 |
Check if the email pops up in MetaDefender Email Gateway Security |
|
|
8 |
Check if the email arrives to the recipient |
|
Sending emails programatically
Bulk emails
The following Perl example sends 100 outbound emails using the example settings above.
use strict;use warnings;use Email::Sender::Simple qw(sendmail);use Email::Sender::Transport::SMTP;use Email::Simple;use Email::Simple::Creator;my $smtpserver = '127.0.0.1';my $smtpport = 10025;my $transport = Email::Sender::Transport::SMTP->new( { host => $smtpserver, port => $smtpport, });my $email = Email::Simple->create( header => [ To => 'one@local', From => 'two@other', Subject => "bulk email", ], body => 'This is the message',);for ( my $i = 0 ; $i < 100 ; $i++ ) { sendmail( $email, { transport => $transport } ); sleep(int(rand(60)));}Infected email
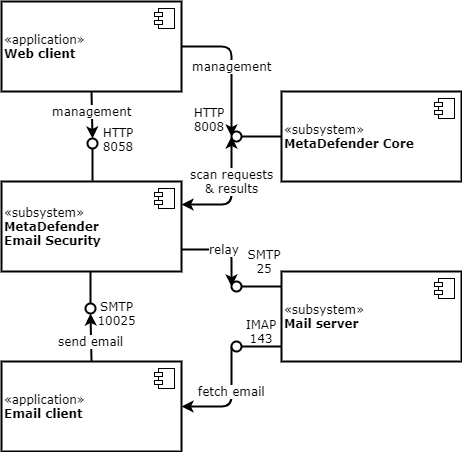
The previous Perl example can be modified to be potentially identified by some of the scan engines as Eicar infected.
The Eicar test string is not copied into this document as text to avoid being identified as threat. Here only images are used instead.
Most probably the resulted Perl program can be saved in the filesystem with no problem.
The email sent by the program will, however, be blocked by some of the engines in MetaDefender Core.
|
Step |
Description |
Screenshot |
|
1 |
|
|
|
2 |
Copy the Eicar test string |
|
|
3 |
Append the Eicar test string to the end of the body text in the previous example |
|