3.9.2 Google Apps integration
Overview
-
Configure the hosted email server to accept email from MetaDefender Email Gateway Security server.
-
Configure MetaDefender Email Gateway Security to relay out to hosted email server.
-
Update MX record to point to MetaDefender Email Gateway Security server.
Detailed Steps
|
Steps |
Details |
|
|
1 |
Go to https://admin.google.com and login to your Google Apps subscription |
|
|
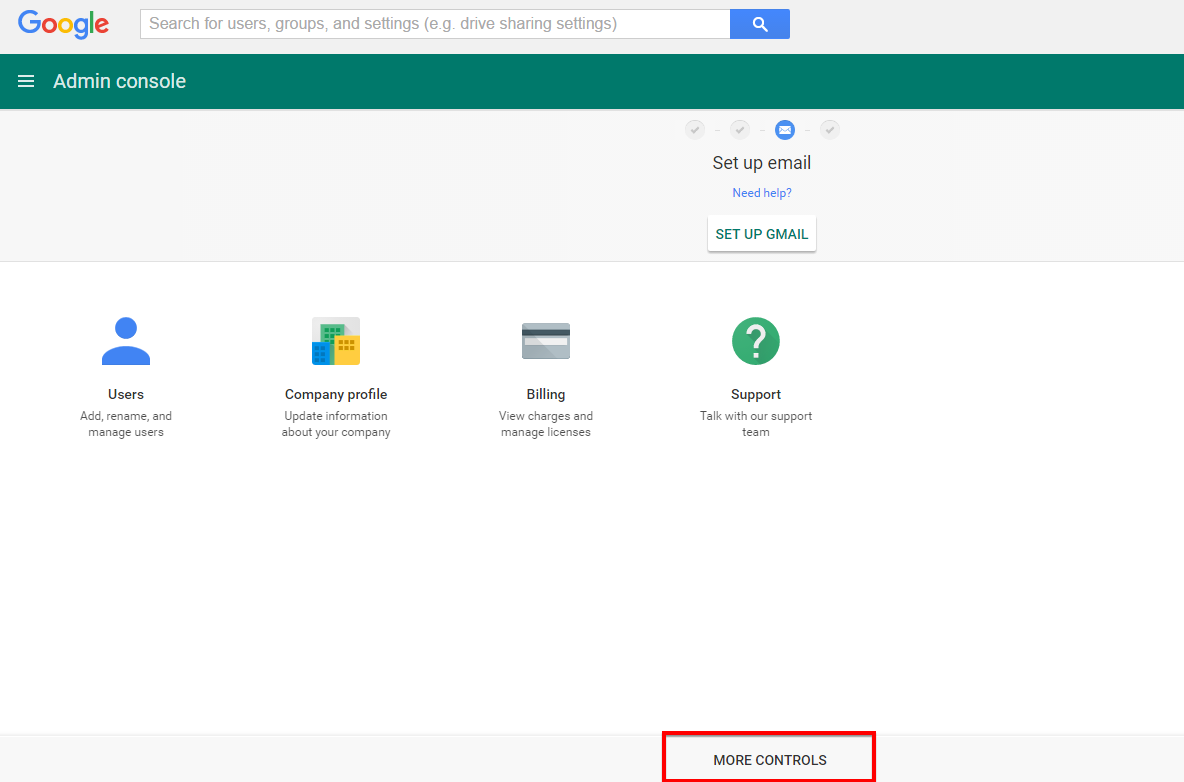
Click 'MORE CONTROLS' |
|
|
|
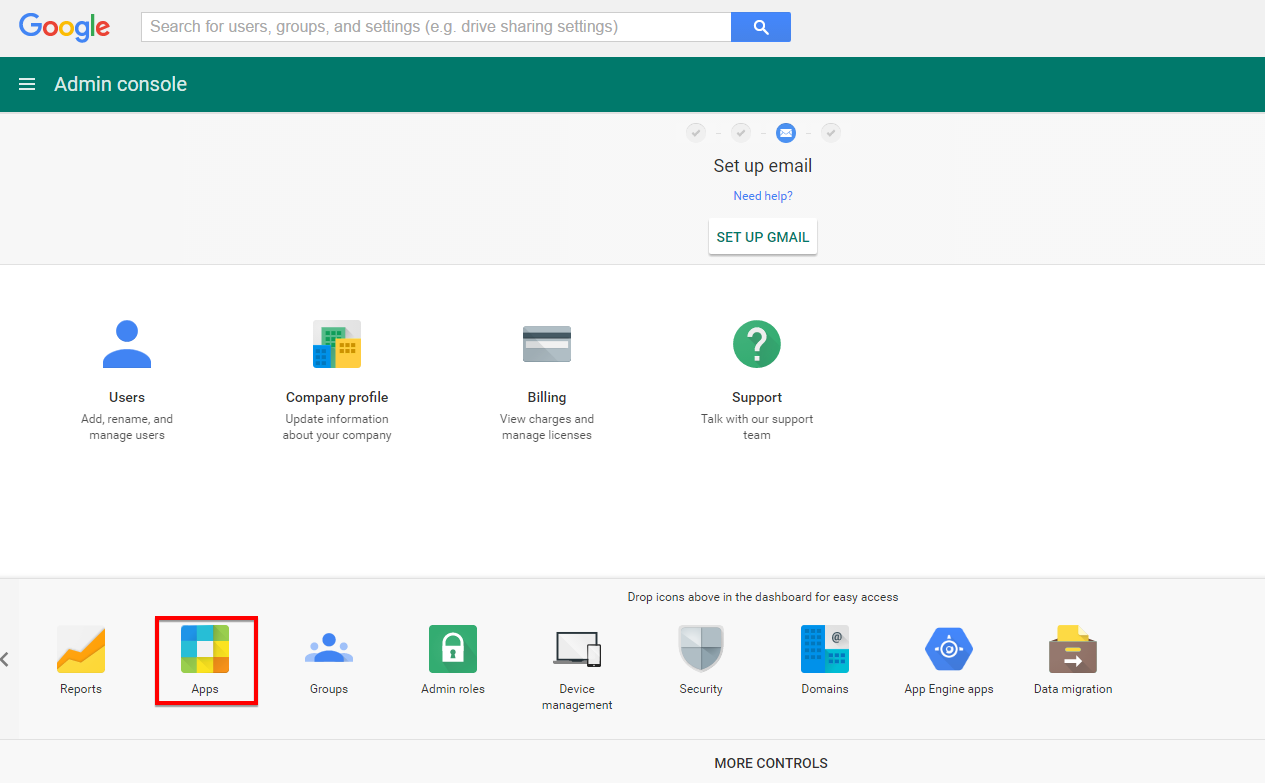
Click 'Apps' |
|
|
|
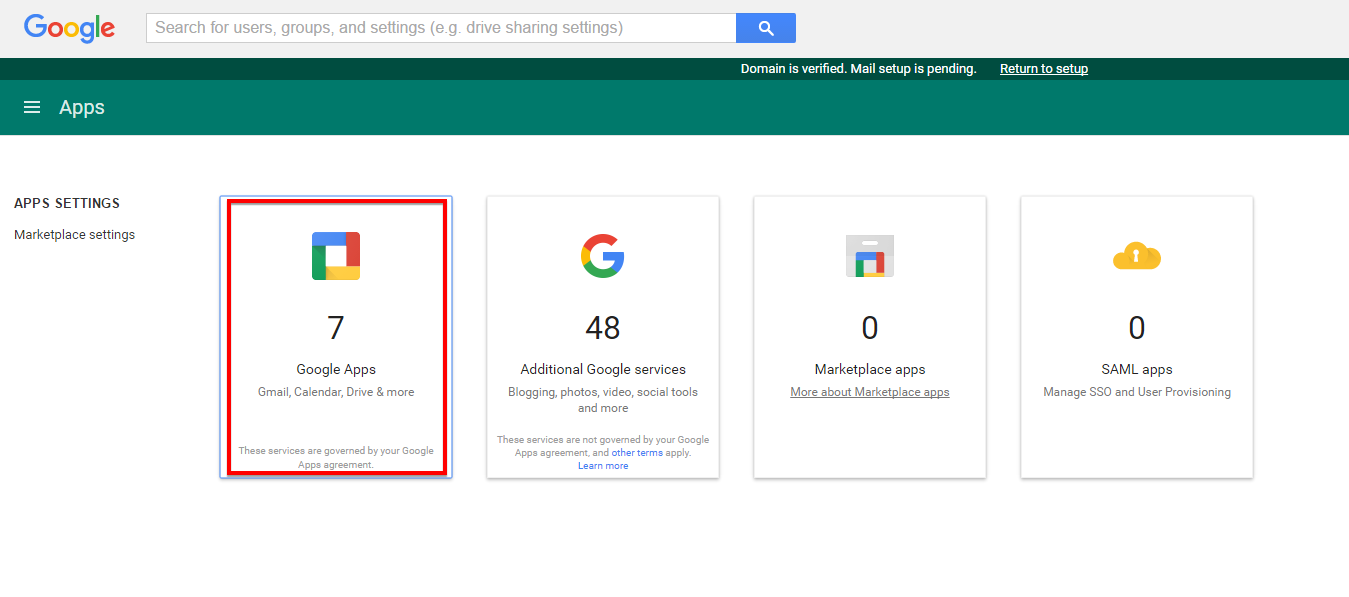
Click 'Google Apps' |
|
|
|
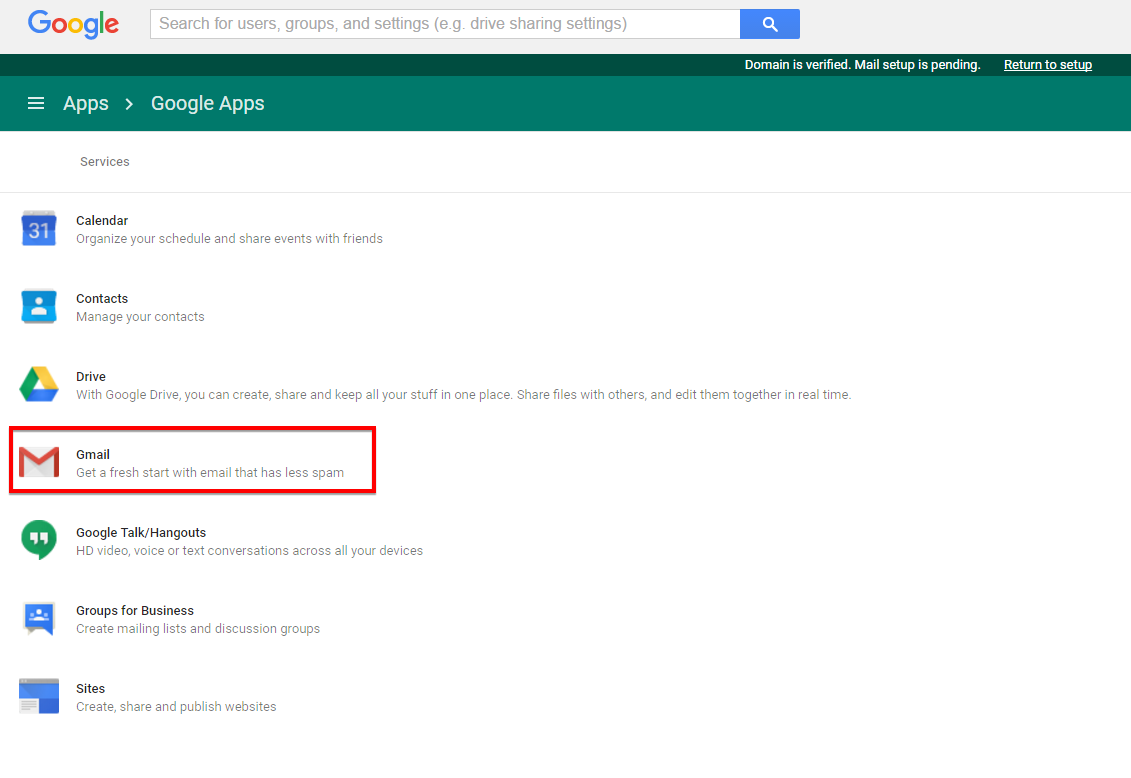
Click 'Gmail' |
|
|
|
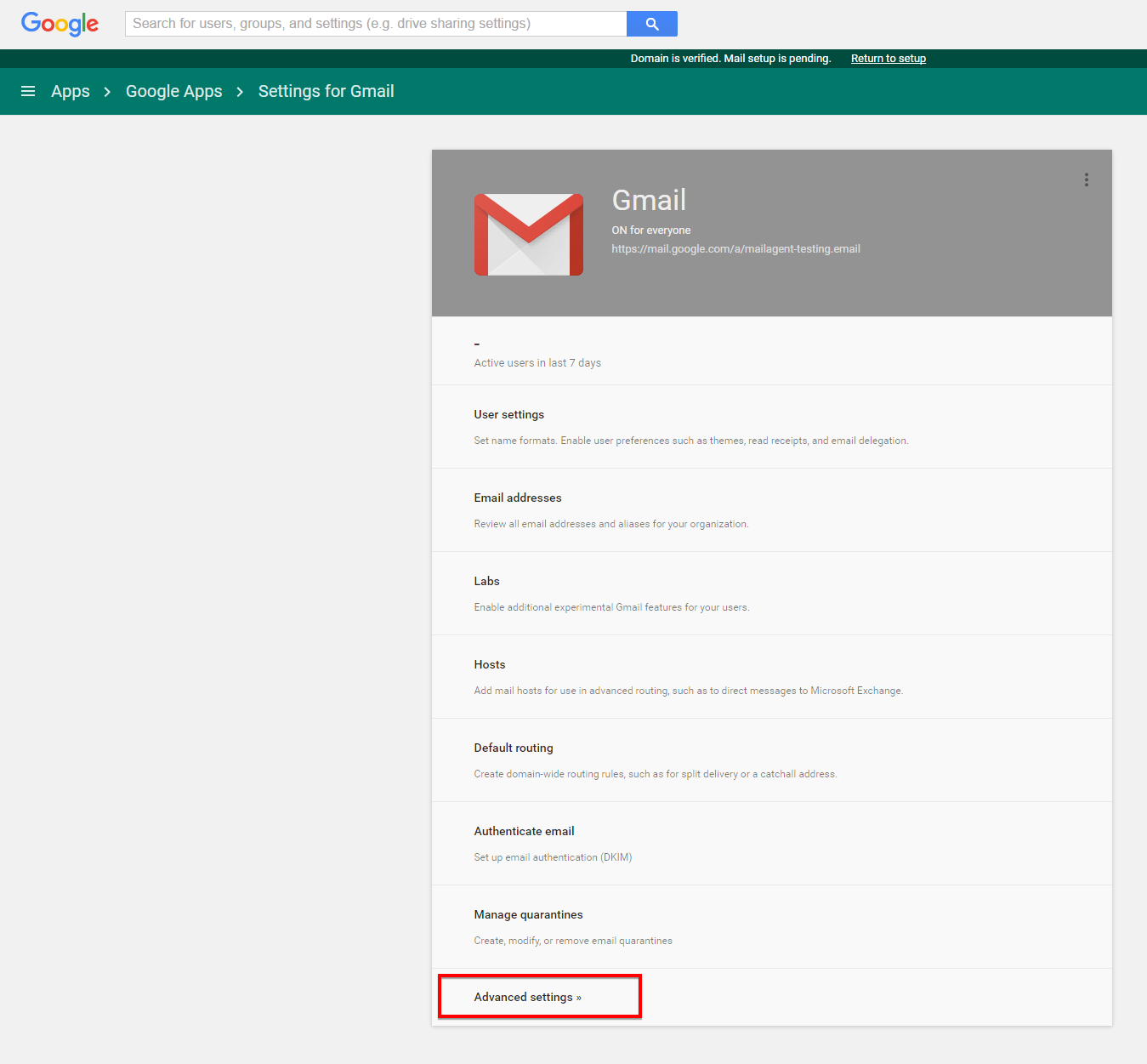
Click 'Advanced settings' |
|
|
|
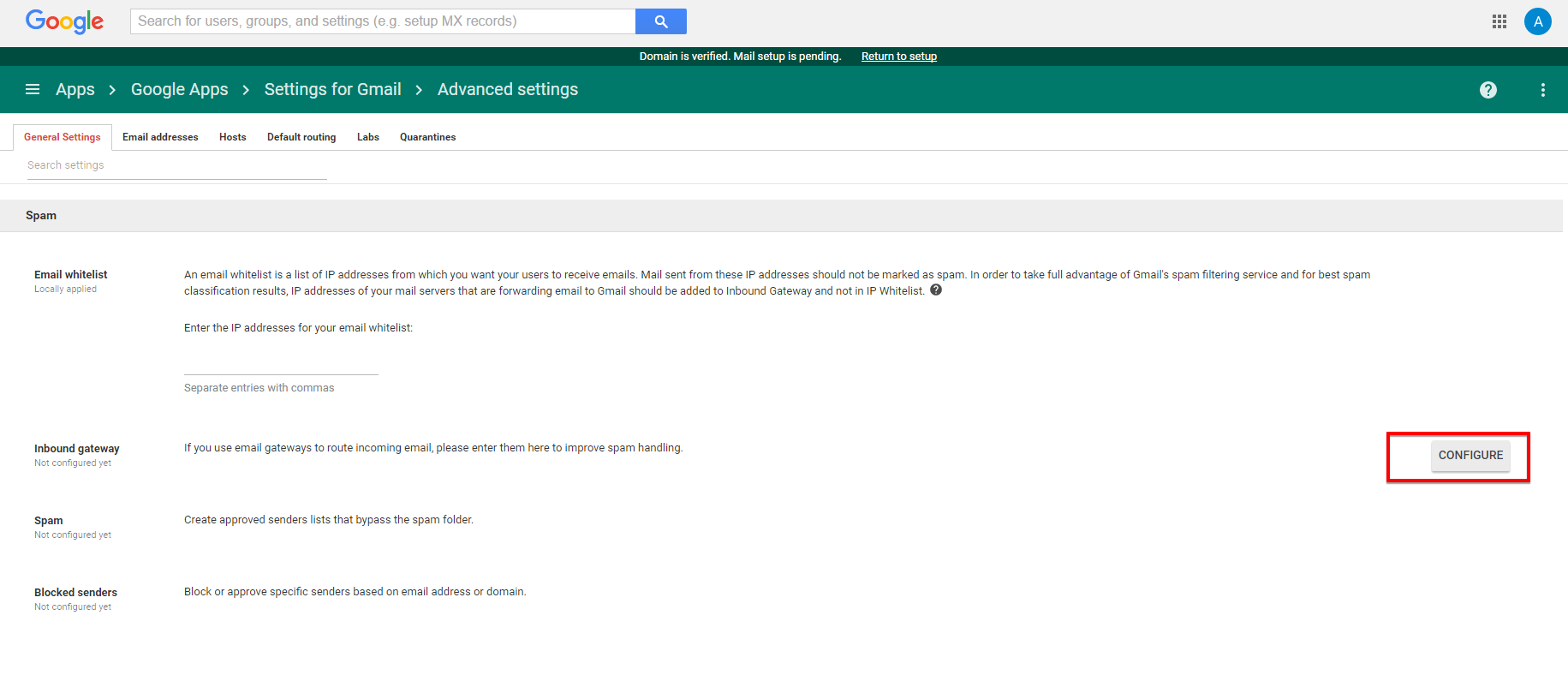
Scroll down to the 'Inbound gateway' section and click 'CONFIGURE' |
|
|
|
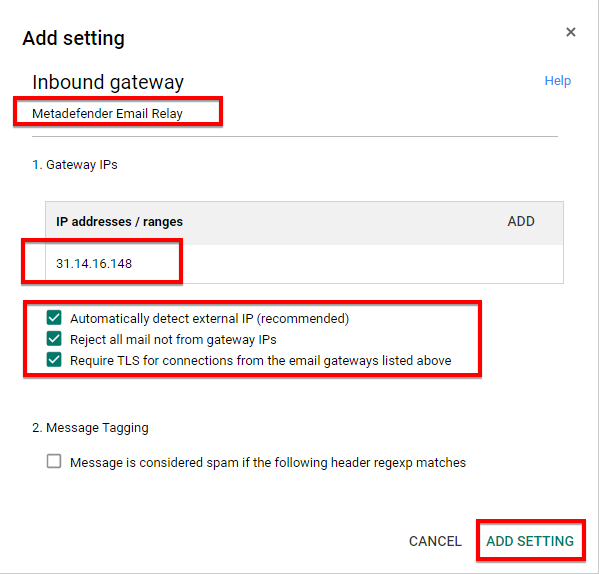
Specify a gateway name (e.g. Metadefender Email Relay) and the IP address of the MetaDefender Email Gateway Security server; check 'Automatically detect external IP (recommended)', 'Reject all mail not from gateway IPs' and 'Require TLS connection from the email gateways listed above' |
|
|
|
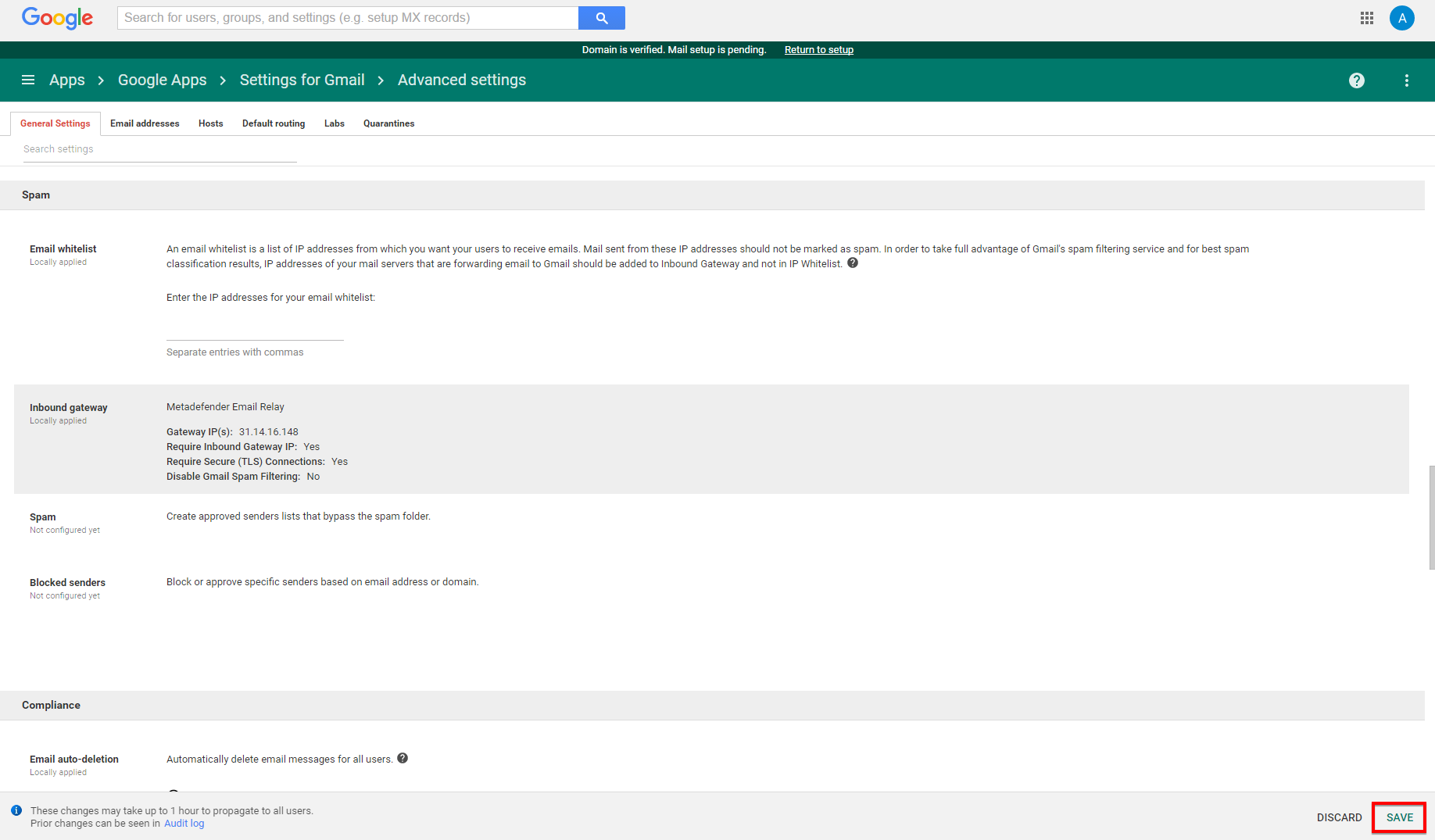
Click 'SAVE' at the bottom right of the screen to save the changes |
|
|
|
2 |
Install MetaDefender Email Gateway Security and configure; for instruction see 1 Quick start with MetaDefender Email Gateway Security |
Remember to configure relays to match your original MX record. For details see 4.2 Security rules . |
|
Configure MetaDefender Email Gateway Security to listen on port 25 |
|
|
|
Verify routing settings by sending an email to a Google Apps recipient directly to the MetaDefender Email Gateway Security server and verify that it arrives correctly in the recipient inbox |
|
|
|
3 |
Refer to your Internet domain registrar for details how to change MX record to point to MetaDefender Email Gateway Security IP address. Verify email routing by sending an email to a Google Apps recipient |
Configure relays to match your original MX record; for details see 4.2 Security rules Make sure that your MX record changes have propagated before verifying email routing. |
Additional notes
-
Quarantine: Google Apps always does a malware check on all incoming emails, so releasing an infected item from quarantine will be rejected by Google Apps. As a workaround for this, configure quarantine to deliver emails to an alternative SMTP server that can accept infected emails.