9.3.1.3. AMI - Distributed MetaDefender Deployment
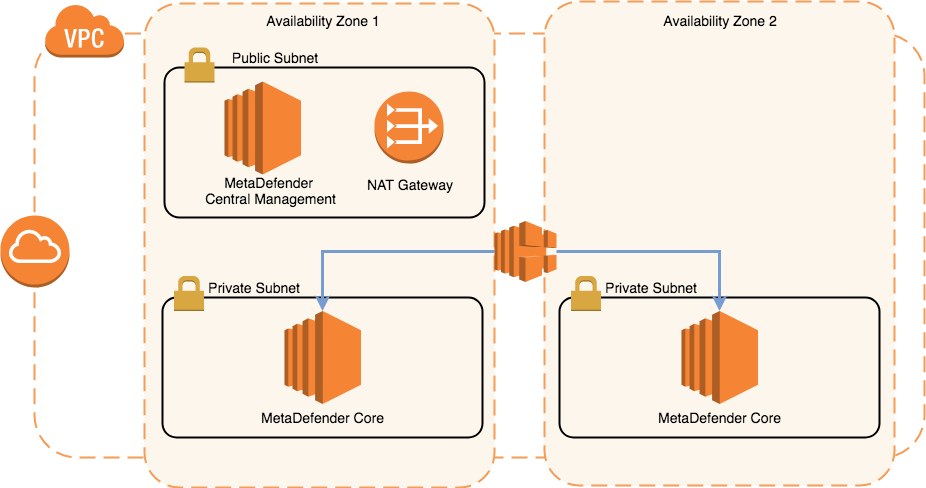
For a distributed environment, we would recommend to use MetaDefender Central Management deployed in a public subnet and MetaDefender Core instances deployed in private subnets, in separate Availability Zones.
Disclaimer: Please note that Central Management is not available on the AWS Marketplace, you will need to download the product from portal.opswat.com, install it and create an AMI.
Even though is a free of charge, will require a license key. Please contact us for details.
OPSWAT provides a CloudFormation template as an example of the deployment seen in the diagram below.
Deployment Diagram:
Deployment flow:
Select the desired MetaDefender, based on the OS support:
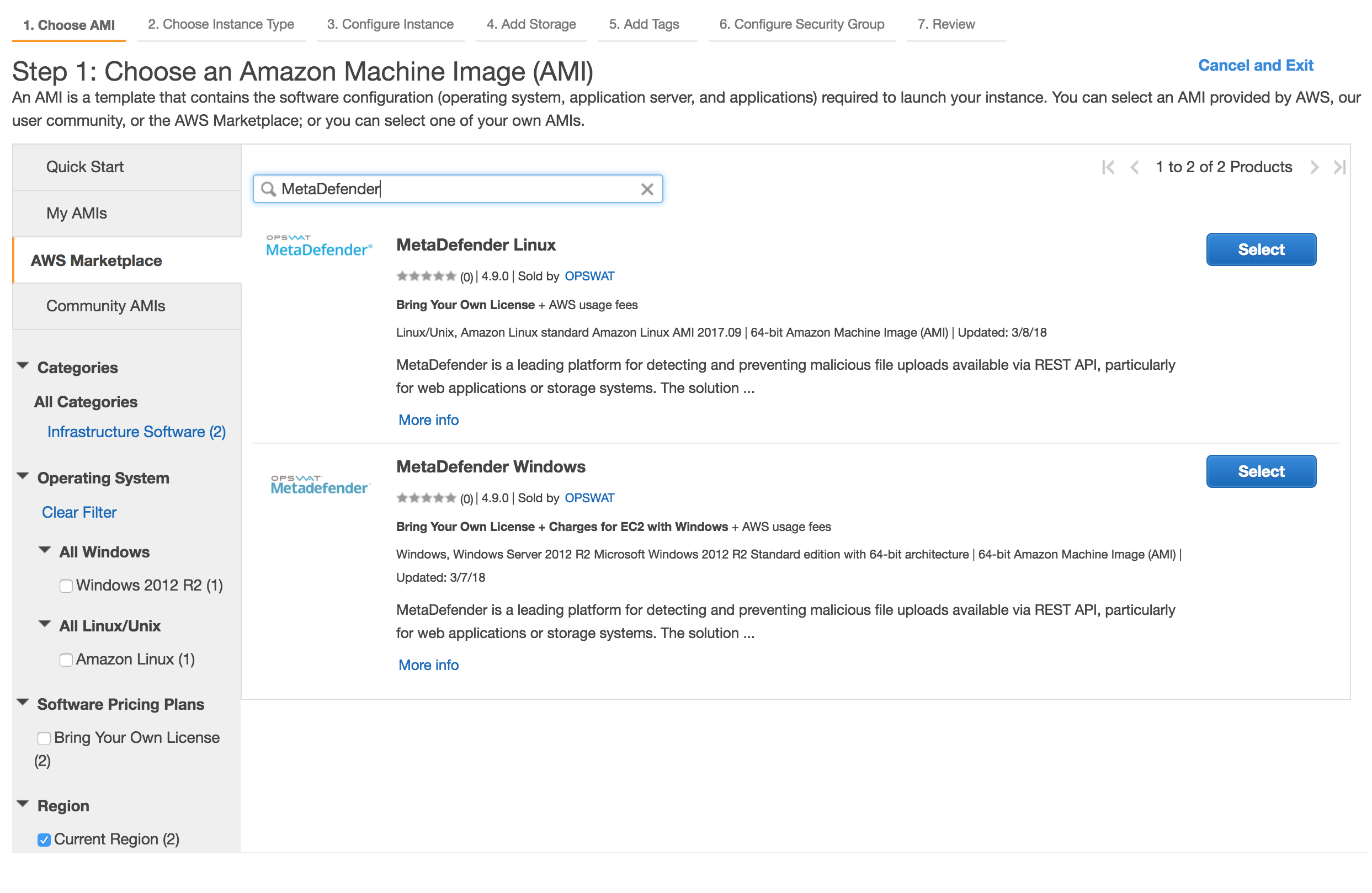
Go through the steps to launch an instance (steps defined here: 8.4.1.1. Install MetaDefender in AWS EC2)
Or, in order to use the CloudFormation template provided, please see OPSWAT's Github account. Our recommendation would be to use this template as an example and modify it accordingly to your business requirements.
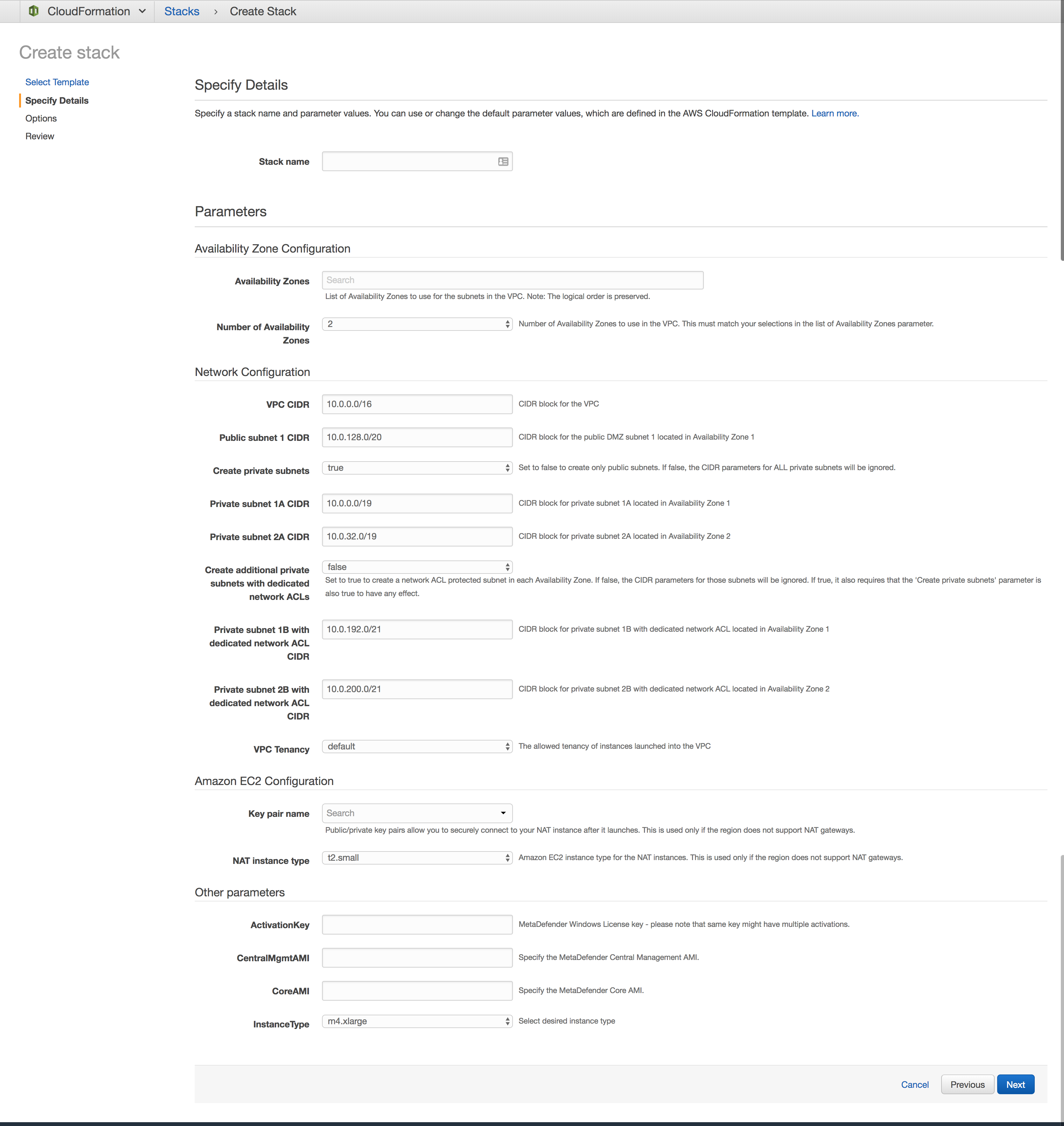
To launch the CloudFormation script, follow these steps:
-
Go to CloudFormation > Create Stack and select the template (or import it):
-
Fill the needed details:
-
Stack name : Identifier for this entire MetaDefender stack
-
Availability Zones
-
Select at least 2 availability zones in the selected region
-
-
Network Configuration
-
Distribution of the CIDR blocks
-
Configure the needed IP allocation per subnets
-
If needed, create additional private subnets with dedicated ACL, not default ones.
-
-
-
EC2 Configuration
-
KeyName: the keypair you would like to use in order to manage this instance
-
Note that it's very important to provide a valid key, especially if you plan to connect to this machine for different investigations
-
-
NAT instance type
-
This is important for regions where NAT Gateway are not yet available (e.g. GovCloud)
-
-
-
MetaDefender Configuration
-
Activation Key: MetaDefender license key
-
AMI:
-
Both for Central Management and Core
-
Grab the AMI id from the AWS Marketplace or from your own built MetaDefender AMI
-
-
-
-
Finish the wizard, acknowledge that IAM roles are being generated and hit Create
The CloudFormation script will generate the needed resources to provide the following flow:
-
Instance initialize phase
-
Central Management
-
User Data script (Powershell for Windows and shell for Linux) will be called which will:
-
change the credentials from the default admin/admin to admin/instance-id
-
updates the CloudWatch Event Rule to be dispatched only for the instances running MetaDefender (adds the new instance-id to the existing list)
-
updates the Deactivate Lambda function by mapping the instance-id to the MetaDefender's unique deploymentId
-
activate the product based on the provided activation key
-
attach the running MetaDefender instances
-
activate MetaDefender instances and push the activation file to MetaDefender instances
-
-
-
MetaDefender Core
-
User Data script (Powershell for Windows and shell for Linux) will be called which will:
-
change the credentials from the default admin/admin to admin/instance-id
-
-
-
-
Instance shutting-down / terminate
-
Deactivate Lambda function will call the OPSWAT Activation Server to deregister the existing MetaDefender deployment
-
Results are logged in CloudWatch
-
-
-
Instance rebooted
-
Respects same flow as Initialize phase
-
Resources:
-
MetaDefender Windows MDWindowsEC2AZ1
-
The VM running the MetaDefender instance in Availability Zone 1
-
-
MetaDefender Windows MDWindowsEC2AZ2
-
The VM running the MetaDefender instance in Availability Zone 2
-
-
MetaDefenderSecurityGroup
-
Only the TCP port 8008 is opened, being the only port needed to communicate with MetaDefender
-
-
CentralManagementSecurityGroup
-
Only the TCP port 8018 is opened, being the only port needed to communicate with MetaDefender Central Management
-
-
LambdaAccessRole
-
IAM Role created for to the EC2 instance, to allow it to update the DeactivateLambda function and the DeactivateEventRule
-
-
LambdaRolePolicies
-
The IAM Policy which grants access to update the defined lambda function and CloudWatch event rule
-
-
LambdaInstanceProfile
-
IAM InstanceProfile that is attached to the EC2 instance
-
-
DeactivateLambda
-
Calls the OPSWAT's Activation Server to deregister the MetaDefender instance on termination.
-
-
LambdaExecutionRole
-
IAM Role to allow running the lambda function and publishing the results in logs
-
-
DeactivateEventRule
-
CloudWatch EventRule which allows to monitor the EC2 instance and calls DeactivateLambda on shutting-down or stopping.
-
-
PermissionForEventsToInvokeLambda
-
Lambda Permission needed to invoke the DeactivateLambda function
-
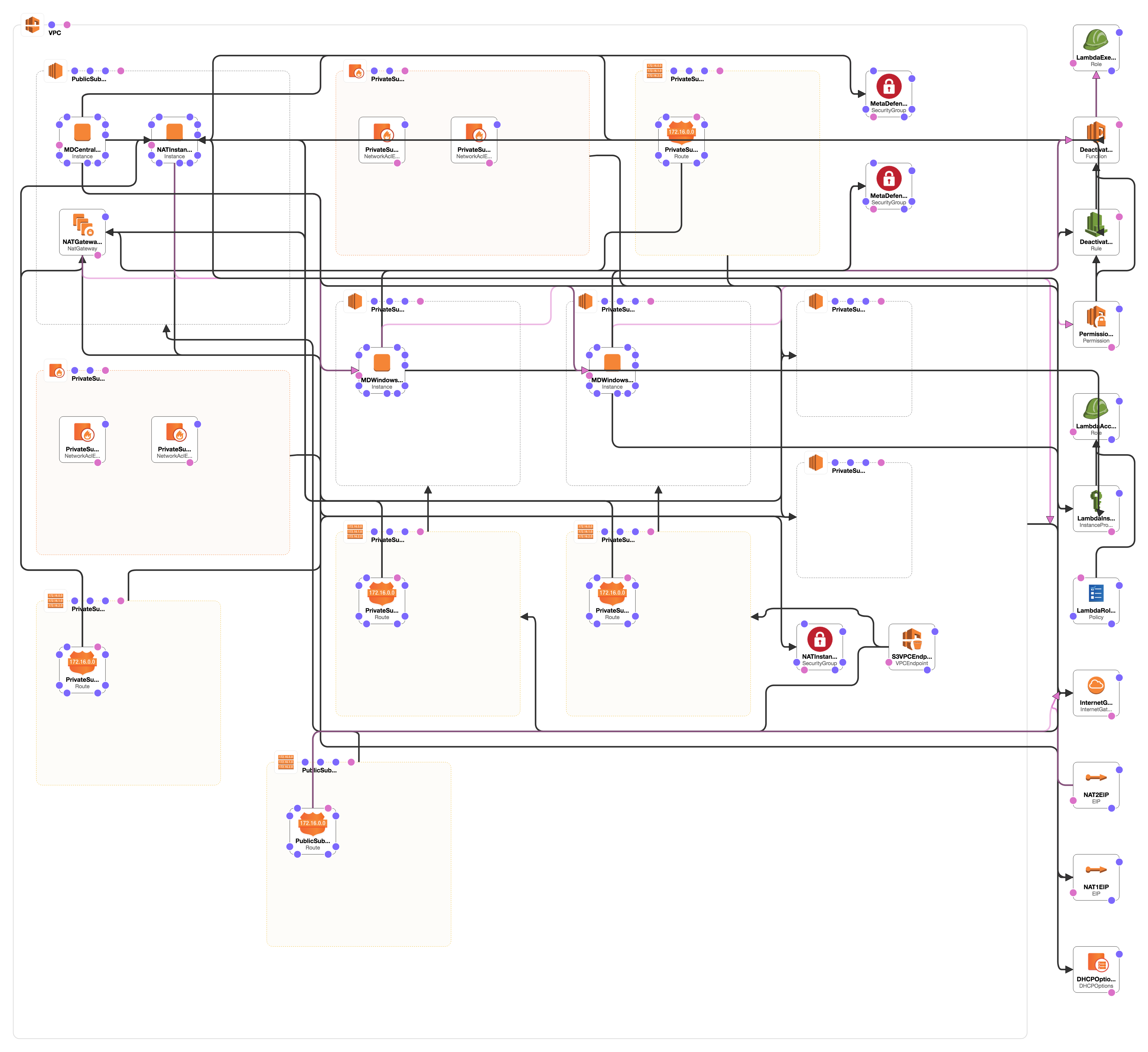
Resources and relationships: