3.2.2. LDAP attributes
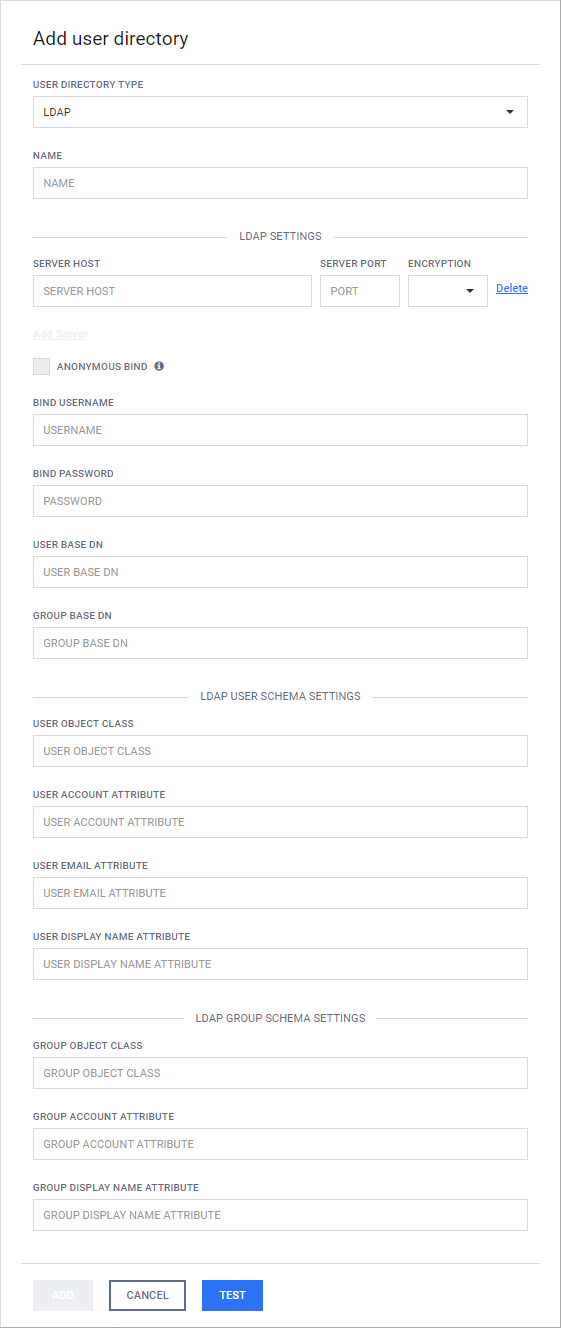
This page contains tips on how to obtain the BIND USERNAME, the USER BASE DN and GROUP BASE DN attributes, the LDAP USER SCHEMA SETTINGS and the LDAP GROUP SCHEMA SETTINGS when creating an LDAP type user directory.
Normally a domain administrator should provide these values.
The BIND USERNAME, the USER BASE DN and GROUP BASE DN attributes must be expressed using a valid LDAP syntax.
Bind username
Normally an LDAP administrator should provide these values, however there is a way to get the BIND USERNAME as an LDAP DN, that is needed for the product to do searches in the directory information tree. To get this information, there is, however, some information about the LDAP tree, that must be known in advance:
|
LDAP property |
Notes |
Example |
|
DN of the LDAP tree node that has the bind user as a child. |
This will be the base for the search. If selected improperly then the search may be very slow or won't find the appropriate user. |
ou=users,dc=test |
|
Attributes and their values that uniquely identify the bind user account. |
These will be used as filter conditions to find the proper user. |
uid=bind |
To find the bind user, perform the following steps:
-
Log on to a Windows machine that has connectivity to the LDAP server
-
Choose a user that is intended for this purpose (ie: has rights to do searches in the tree)
-
Open the LDP.exe tool with elevated rights (Run as Administrator)
-
Assuming the example properties above are correct, do the following search:
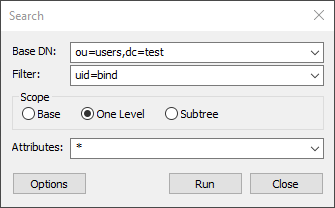
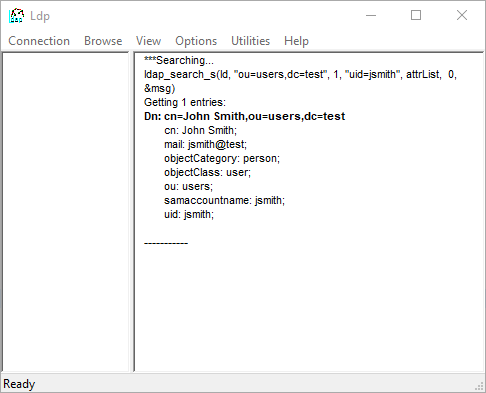
The search above will return the attributes for the user in question:
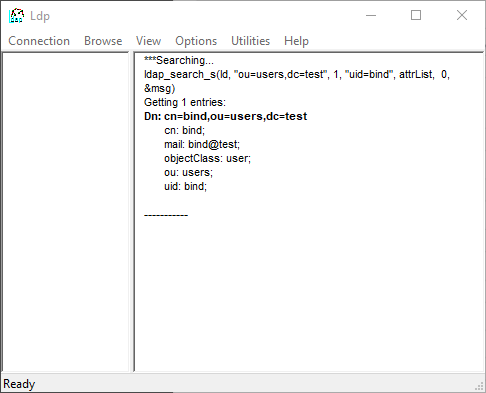
The DN should look something like this:
cn=bind,ou=users,dc=testPlease note, the actual user DN will most probably look completely different than the above example, as it depends on the structure of the underlying directory information tree in the LDAP server.
On non-server Windows machines the LDP.exe tool can be obtained with installing the Remote Server Administration Tools (RSAT).
User base and group base DN
Once the bind user DN is obtained, an easy way to get the DNs for the user and group searches is by taking all the DC parts of the user DN and leaving the rest out. Using the examples above the result DN will be the following:
dc=testPlease note that using only DC components for the user/group DNs may result in searches to be executed from the top of the directory information tree and potentially slow down the LDAP server responses a lot and thus have an impact on the MetaDefender product's password validation. The rule of thumb here is that the more specific the user/group DN, the faster the server response is.
Please also note that users and groups may reside in different parts of the directory information tree, as a consequence applying the same, more specific DN both as USER BASE DN and GROUP BASE DN may cause the MetaDefender product to not find group accounts in the directory information tree. So these DNs should be chosen carefully.
LDAP user schema settings
Similarly to the search in Bind username, we can search for users and determine the appropriate values.
Example
-
Let's assume the following search is executed:
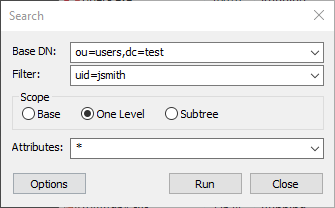
-
That gives the following result:
-
The LDAP USER SCHEMA SETTINGS may be the following:
User schema setting
LDAP attribute
USER OBJECT CLASS
user
USER ACCOUNT ATTRIBUTE
uid or samaccountname
USER EMAIL ATTRIBUTE
mail
USER DISPLAY NAME ATTRIBUTE
cn
LDAP group schema settings
Similarly to the search in LDAP user schema settings, we can search for users and determine the appropriate values.