6.8. Version 5.2.1
5.2.1 MetaDefender Email Gateway Security release |
|
|
January 28, 2021 |
MetaDefender Email Gateway Security 5.2.1 is a maintenance release focusing on minor improvements and fixes. |
New & improved |
|
Ignore CDR’s blacklist |
If Deep CDR’s Blacklist unsupported file types option is enabled, it was not possible to rescan emails with password protected attachments as password protected files are blacklisted by Deep CDR. Email Gateway Security can now process emails with password protected attachments as usual even if Deep CDR’s Blacklist unsupported file types option is enabled. For details see 5.3. Quarantine and 5.6. Password protected attachments. |
SMTP IP address configuration |
Email Gateway Security now has a Registry option to configure on which IP addresses it listens for SMTP connections. For details see the smtpaddress option in 4.1. Registry configuration. |
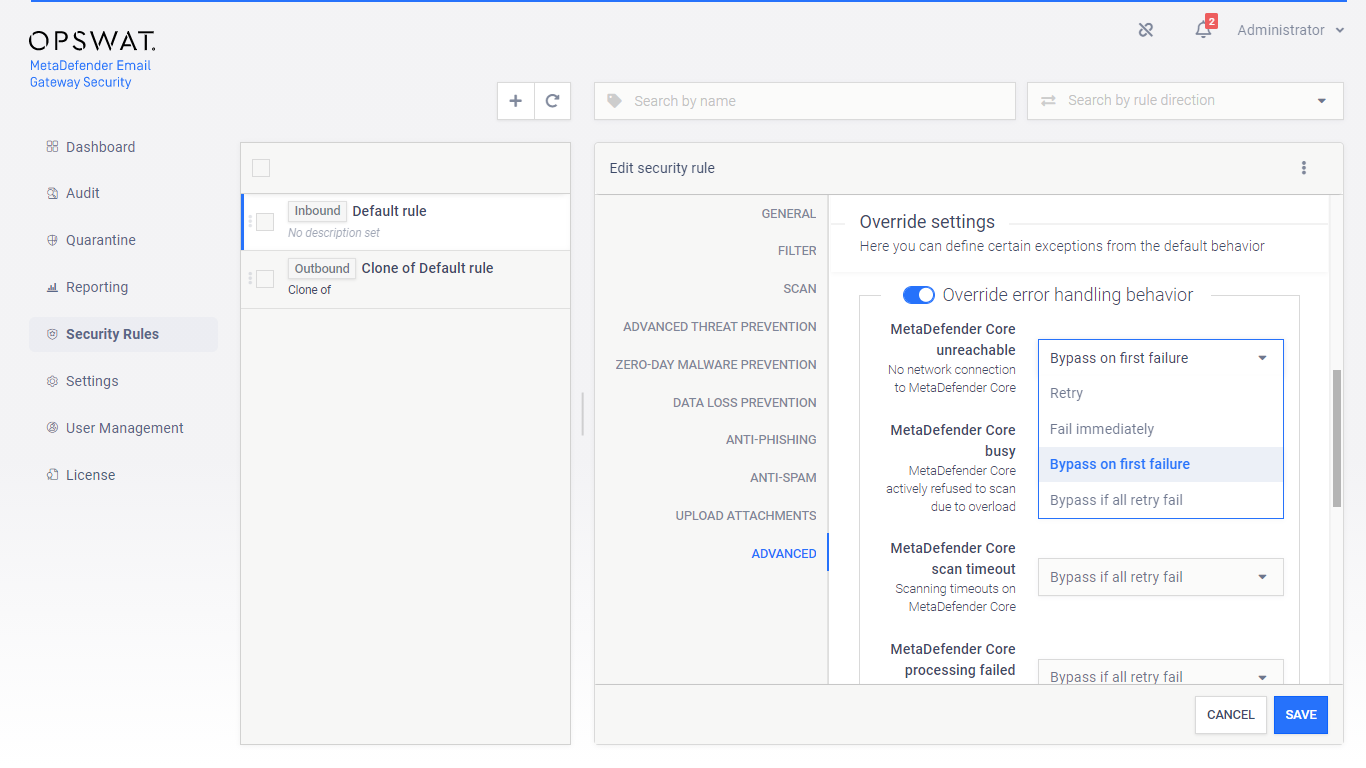
Bypass emails after first failure |
Email Gateway Security can now be configured to bypass immediately if a subcomponent is unreachable or fails. To do so, under Security Rules > rule / ADVANCED / Override error handling behavior set the appropriate entry to Bypass on first failure. For details see 4.4. Policy. |
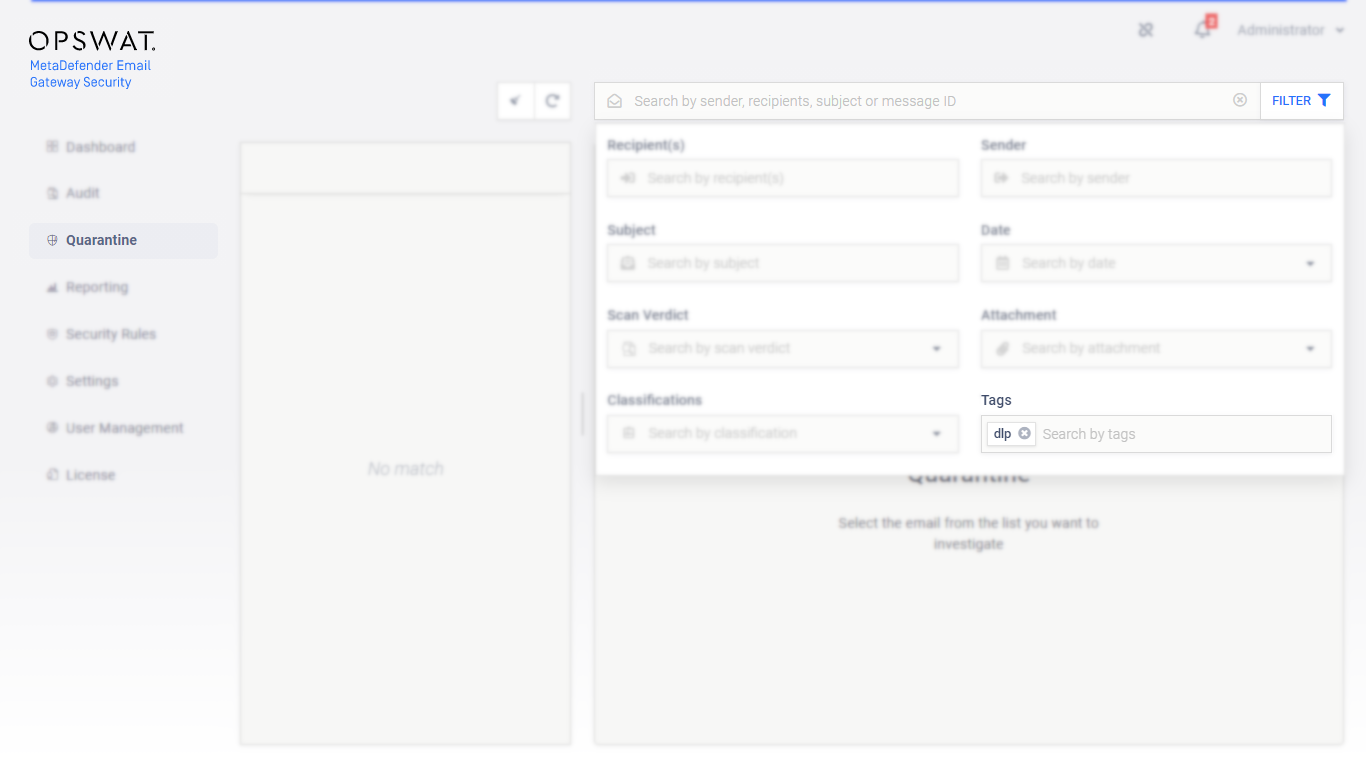
Tag filter field on Quarantine page |
Email Gateway Security now supports filtering the quarantine list by the tags applied to the emails. For details see 5.3. Quarantine. |
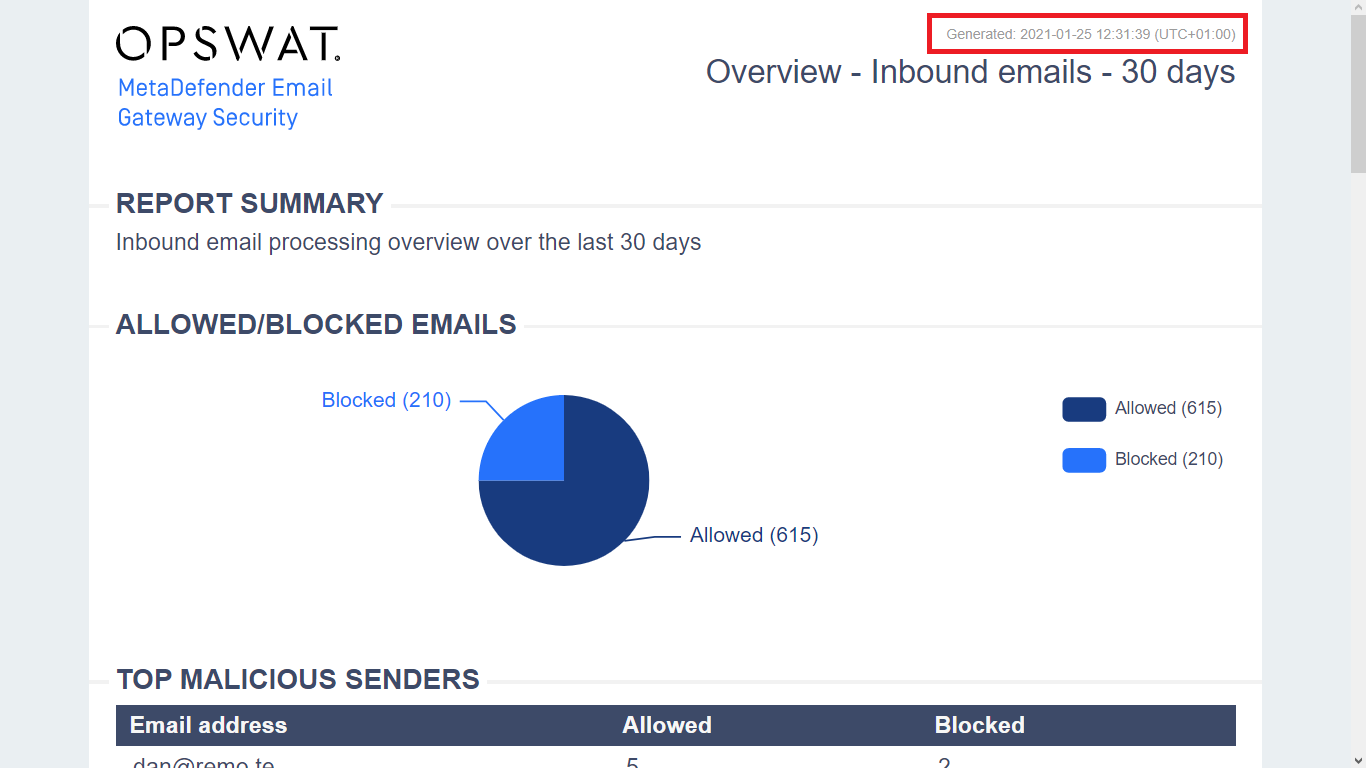
Reports' Generated time in local time |
The Generated date and time info can now be set to be displayed in the server’s local time (previously it was always UTC). The Generated date and time info now follows the setting under Settings > General / Configuration / Use the server's local timezone. For details see 5.4. Reporting. |
Fixed |
|
Misleading Japanese translation |
The message MetaDefender Vault upload failed in Emaill History was translating to the incorrect sentence that means successful upload in Japanese. |
Vault profile with port 443 failed |
Previously it was not possible to create a MetaDefender Vault server profile that used port 443. |
Misleading rescan error message |
The rescan page always gave the error message Rescanning the email failed: The availability limit expired indifferent from the real error case (e.g. the message was the previous even if the rescan failed because the email previously was successfully rescanned). |
Changed |
|
Public address removed from CM |
The option Settings > General / Configuration / Public server address has been removed from under Central Management control. |
Safe URL redirect enabled default |
The option Security Rules > rule / Anti-phishing / Enable Anti-Phishing / Enable Dynamic Anti-Phishing is enabled by default for new rules created. |