4.1. Registry configuration
-
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security
-
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security\global
-
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security\logger
-
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security\database
Some configuration options of the server are available in Windows Registry.
After modifying the server configuration entries in the Windows Registry, you must restart the Metadefender Email Gateway Security service in order for the changes to take effect.
Default logging target is Windows Event Log with default level of info (see below).
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security
|
Parameter |
Default value |
Type |
Required |
Description |
|
ExchangeMode |
N/A |
N/A |
N/A |
Do not change this value manually! This value is set when Email Gateway Security is installed in Exchange plugin mode. For details see 4.9. Onsite Microsoft Exchange deployment. |
|
InstallationFolder |
C:\Program Files\OPSWAT\MetaDefender Email Security\ |
string |
N/A |
Do not change this value manually! This value is by the Email Gateway Security installation. |
|
external_quarantine_block |
|
dword |
optional |
Enable quarantining the original copy of blocked emails on an other mail server. For details see 4.10. Quarantine configuration. If the parameter does not exist or if it is 0, then the internal quarantine will be used in case of blocked emails. |
|
external_quarantine_sanitize |
|
dword |
optional |
Enable quarantining the original copy of sanitized emails on an other mail server. For details see 4.10. Quarantine configuration. If the parameter does not exist or if it is 0, then the internal quarantine will be used in case of sanitized emails. |
|
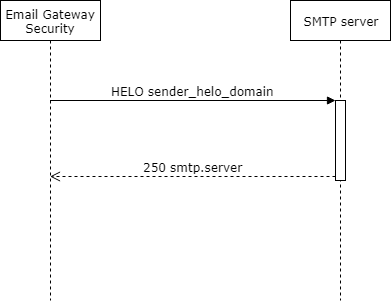
sender_helo_domain |
|
string |
optional |
The fully qualified domain name (FQDN) that Email Gateway Security will send in HELO/EHLO commands to relay SMTP servers. Besides this FQDN the external IP address of Email Security will also be sent. For details see section Opening and closing in RFC 821. If the parameter does not exist or if it is empty then the computer name of Email Gateway Security is sent in HELO/EHLO.
|
|
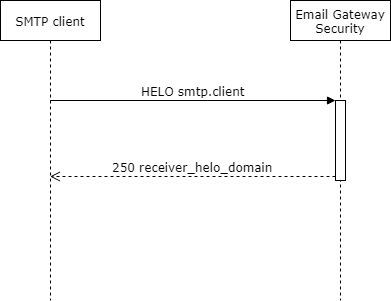
receiver_helo_domain |
|
string |
optional |
The fully qualified domain name (FQDN) that Email Gateway Security will send in HELO/EHLO commands to SMTP clients. For details see section Opening and closing in RFC 821. If the parameter does not exist or if it is empty then the
computer name of Email Gateway Security is sent in the response to a HELO/EHLO.
|
|
exchange_exclude_probe_emails |
|
dword |
optional |
Microsoft Exchange Server sends probe email messages to monitor the health status of the email processing components. This probe messages can, however, fill Audit > Email History. Setting this parameter to 0 will enable listing Exchange probe messages in Audit > Email History. If the parameter does not exist or if it is 1, then Exchange probe messages are not listed in Audit > Email History. No service restart is needed There is no need to restart any services for this setting to take effect, because the transport agent reads and applies this registry setting for each email. |
|
processing_threshold |
75 |
dword |
optional |
This parameter limits the number of emails with "Processing" status at the same time. If this parameter is not present then this number is 75 by default. Setting this value lower can reduce the processing load on both Email Gateway Security and Core. If the parameter is 0 then the throttling is disabled. |
|
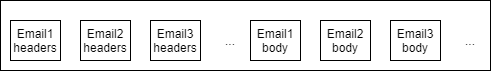
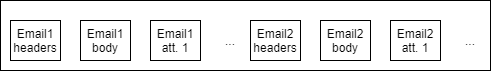
concurrency_threshold |
N/A |
dword |
optional |
This parameter limits the number of concurrent threads submitting emails to MetaDefender Core for scanning. Example By default Email Gateway Security submits emails to Core on several threads. This causes the components of different emails to mix in the Core queue. If this parameter is set to 1, then contents are sent to Core email by email with no overlapping.
If the parameter is 0 then no direct limitation is applied. |
|
scheduled_db_optimization_time |
03:00 |
string |
optional |
If this parameter is set, then Email Gateway Security performs a database optimization at the time configured. 24 hours scheme The DB optimization time must be set in 24 hours scheme. For example 3 AM is 03:00, while 3 PM is 15:00.
Set by default This value is set to 03:00 (3:00AM each day) by the installation. The value syntax is: Value syntax
<hh>:<mm>Configured to the following value, Email Gateway Security performs the optimization at 3:00AM each day: Value example
03:00If not set (or can not be interpreted as a time value) then no optimization is performed. |
|
in_folder_timer_interval |
1000 |
dword |
optional |
Interval –in milliseconds– between polling of new emails. |
|
max_email_insert_count |
100 |
dword |
optional |
Maximum number of emails to insert into the database in a single batch. |
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security\global
|
Parameter |
Default value |
Type |
Required |
Description |
|
restaddress |
* |
string |
required |
One or all of the IP addresses of the computer that runs the product to serve the web user interface (* means all interfaces) Supported values * : all IPv4 and IPv6 interfaces One specific IPv4 or IPv6 address : the specific IPv4 or IPv6 address |
|
restport |
8058 |
string |
required |
Designated port number for the web management console (REST) interface |
|
public_rescan_port |
N/A |
string |
optional |
Designated port number for the rescan functionality web and REST interface. Rescan functionality is always -even if this value is defined- available on the restport. For details about rescan see 5.6. Password protected attachments. |
|
smtpaddress |
* |
string |
optional |
One or all of the IP addresses of the computer that runs the product to serve the SMTP interface (* means all interfaces) Supported values Missing or * : all IPv4 and IPv6 interfaces One specific IPv4 or IPv6 address : the specific IPv4 or IPv6 address |
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security\logger
|
Parameter |
Default value |
Type |
Required |
Description |
|
logfile |
|
string |
optional |
Location of a log file to write log messages to. If the parameter does not exist, then no logs are written to any logfile. Empty string is not allowed as a value. |
|
loglevel |
|
string |
optional |
Level of logging. Supported values are: debug, info, warning, error. |
|
wineventlog_level |
info |
string |
optional |
Level of logging. Supported values are: debug, info, warning, error. If the parameter does not exist, then no logs are written to the Windows Logs. |
|
syslog |
|
string |
optional |
Value can only be in form of udp://<hostname>:<port>. If the parameter does not exist, then no logs are written to syslog. (Multiple server can be specified separated with comma) |
|
syslog_level |
|
string |
optional |
Level of logging. Supported values are: debug, info, warning, error. |
|
override |
|
string |
optional |
Override specific log ids to display them on another level e.g.: "1723:error,663:info". Note: when displaying these log ids their original level will remain the same. Empty string is allowed as a value. |
|
cef |
false |
string |
optional |
If true, the log format is Common Event Format. |
|
local_timezone |
false |
string |
optional |
If true, the times sent in syslog messages will be in the server's local timezone. This does not effect entries in the log file/Windows event log. When syslog is used with cef and local_timezone enabled the timezone name can vary based on the underlying system and it's settings. Examples
|
|
nginx_logfile |
[installdir]\nginx\nginx.log |
string |
optional |
File name and path to store the Nginx logs. (Rotation of this log has not yet been solved on Windows systems) |
|
log_rotation |
false |
string |
optional |
If true, the log file specified by the logfile entry is rotated after 24 hours from creation. The last 30 log files are stored, the oldest log file will be deleted if number of files reaches the limit. Logfile entry required The logfile entry must be set for this option to work. Naming convention The rotated log files are named according to the following convention: <file name from logfile entry>-<yyyyMMdd>-<nnn>.gz The trailing three digits (<nnn>) ensure that the file name is unique. Example mdemailsecurity-20200525.gz Support package All stored log files are included in MetaDefender Email Gateway Security's support package. |
|
nginx_log_rotation |
false |
string |
optional |
If true, the log file specified by the nginx_logfile entry is rotated after 24 hours from creation. The last 30 log files are stored, the oldest log file will be deleted if number of files reaches the limit. Naming convention The rotated log files are named according to the following convention: <file name from nginx_logfile entry>-<yyyyMMdd>-<nnn>.gz The trailing three digits (<nnn>) ensure that the file name is unique. Example nginx-20200730.gz Support package All stored Nginx log files are included in MetaDefender Email Gateway Security's support package. |
You must set both of syslog and syslog_level or none of them, and you must set both of logfile and loglevel or none of them.
HKEY_LOCAL_MACHINE\SOFTWARE\OPSWAT\Metadefender Email Security\database
|
Parameter |
Defalut value |
Type |
Required |
Description |
|
instance |
computer name |
string |
required |
This parameter is the name of the Email Gateway Security instance in scalable mode. This parameter is relevant when upgrading a standalone instance to scalable. For details see 5.15. Scalable deployment operation. |
|
mode |
local |
string |
required |
This parameter tells Email Gateway Security in what scalability mode it is. This parameter must be local for bundle and standalone edition deployments. For details see 5.15. Scalable deployment operation. |