6.7. Version 5.2.0
5.2.0 MetaDefender Email Gateway Security release |
|
|
December 17, 2020 |
MetaDefender Email Gateway Security 5.2.0 is a feature release focusing on the new reporting capability of the product. |
New & improved |
|
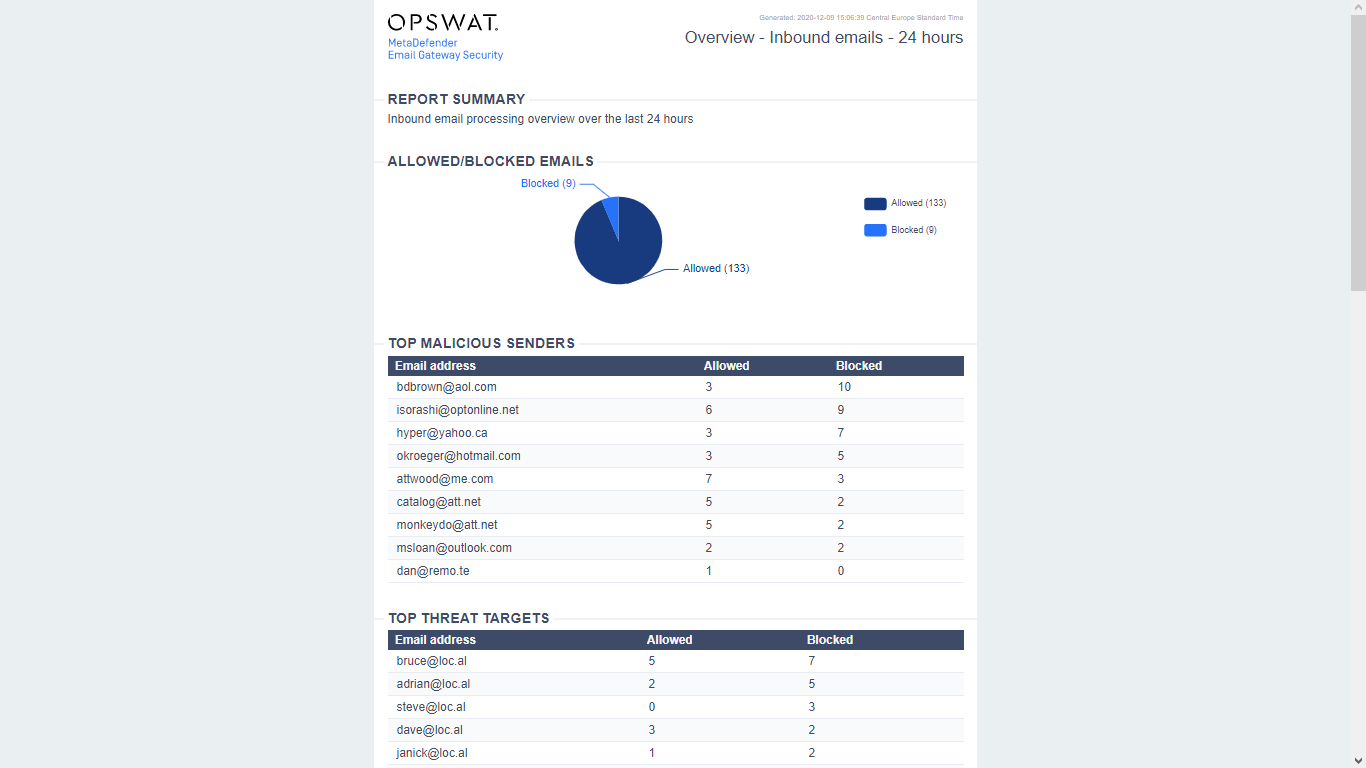
Reporting |
Email Gateway Security now provides a built-in reporting functionality. A report of the most essential processing results can be generated with a single click. The information is presented in a well organized, printing ready format. For details see 5.4. Reporting. |
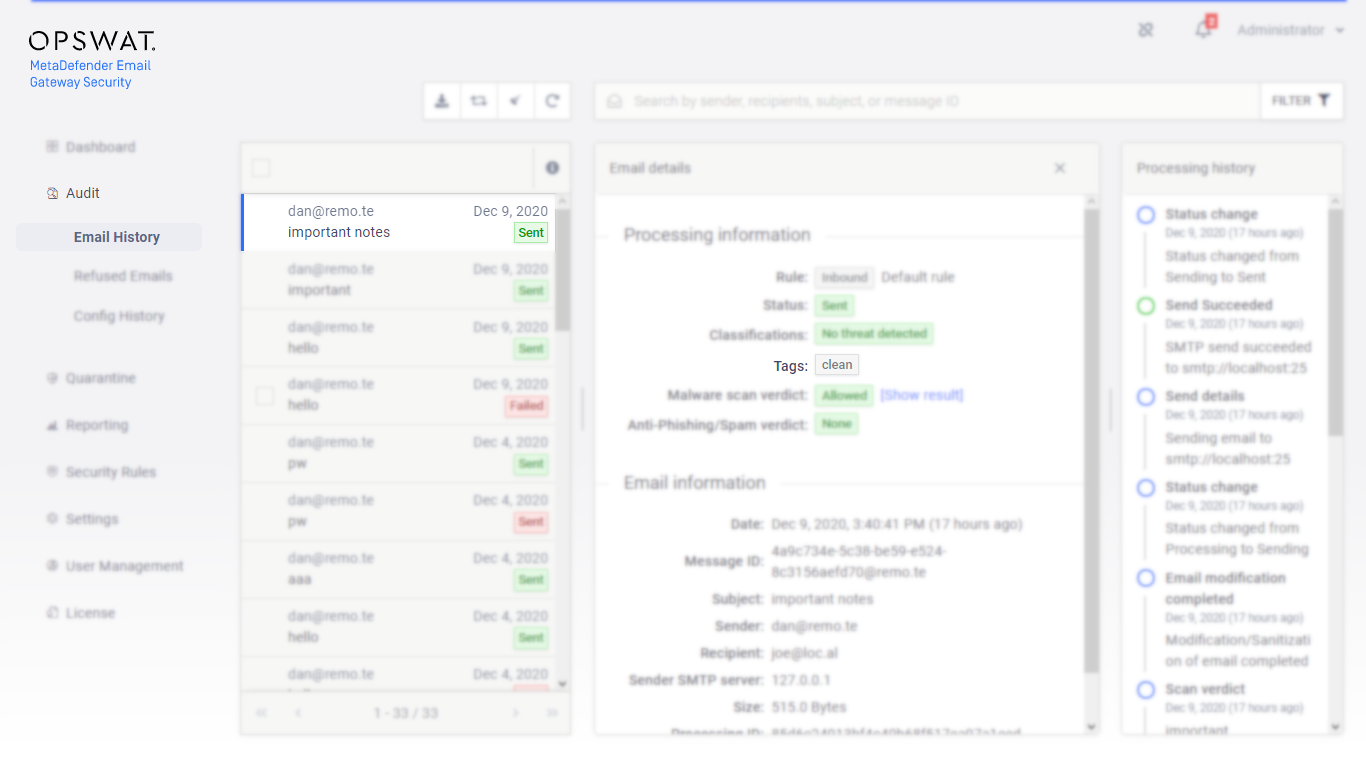
Tags in rules and emails |
Email Gateway Security supports adding markers - called tags - to emails, to provide a user-defined notation for emails based on different processing properties of a specific email. Emails then can be filtered based o these tags, and the tags can even be configured to appear in the subject of the delivered email. For details see 4.4. Policy, 5.2. Email History, 5.3. Quarantine and 5.12. Email tags. |
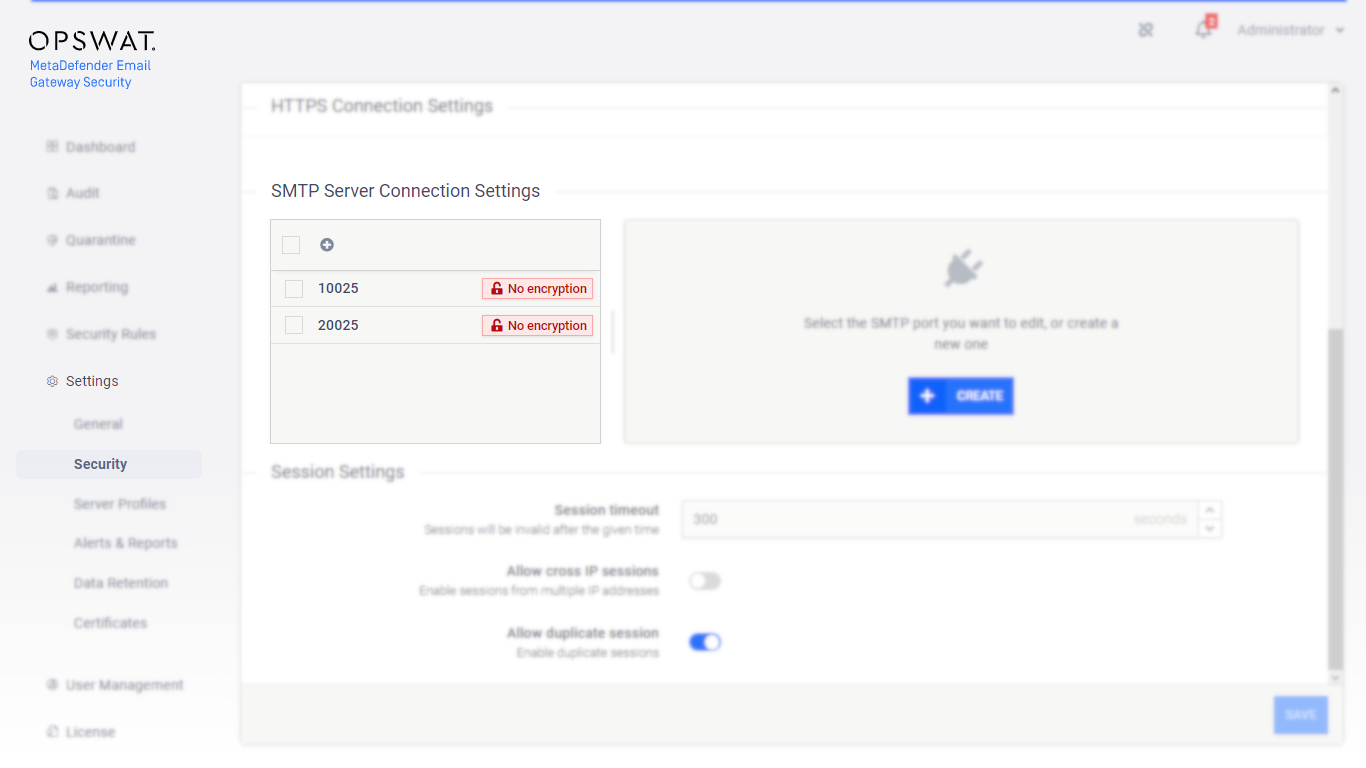
Multiple SMTP ports |
Email Gateway Security can now listen on multiple SMTP ports providing the option to apply different settings for each SMTP port. For details see 4.3. Settings. |
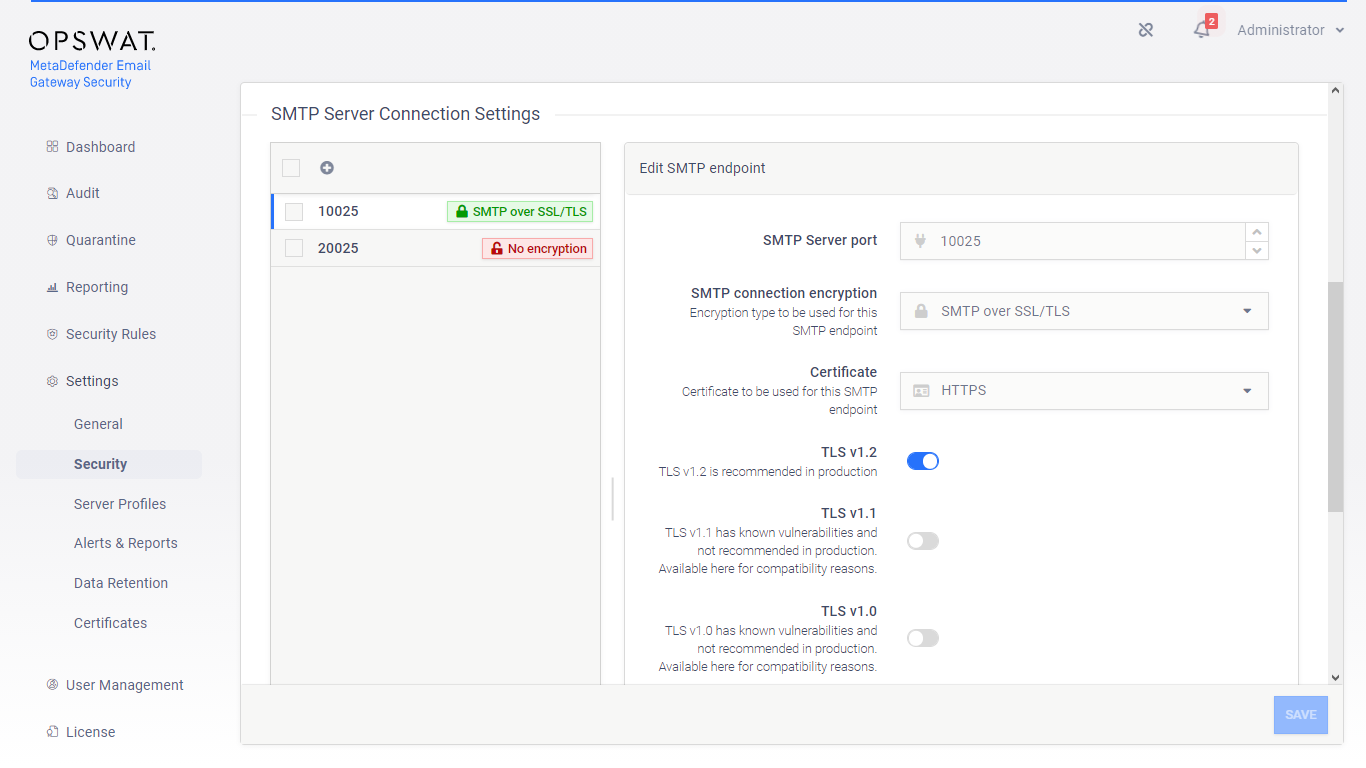
Secure SMTP configuration |
Similarly to HTTPS for the web management console, SMTP over TLS (SMTPS) or other encryption protocols (StartTLS) can now be configured on the user interface. For details see 4.3. Settings and 4.2. Transport Layer Security. |
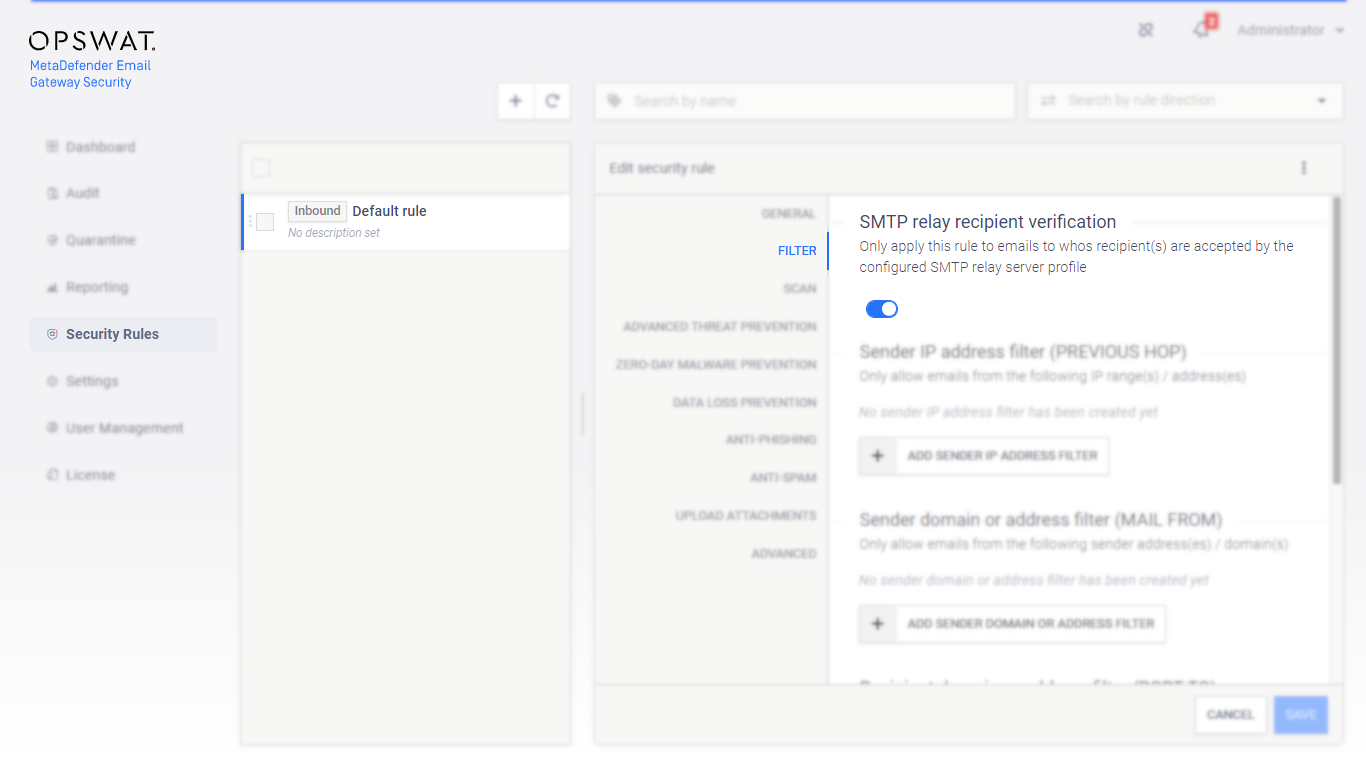
Email recipient verification |
Email Gateway Security can be configured to apply a rule only if the recipient of the email is accepted by any of the SMTP servers of the SMTP server profile configured for the rule. This option can help avoiding situations when Email Gateway Security accepts an email even if it is known to be unable to forward it. In such cases the email ends up in Failed status and pollutes the Audit > Email History with email junk that can not be delivered For details see 4.4.4. Recipient verification. |
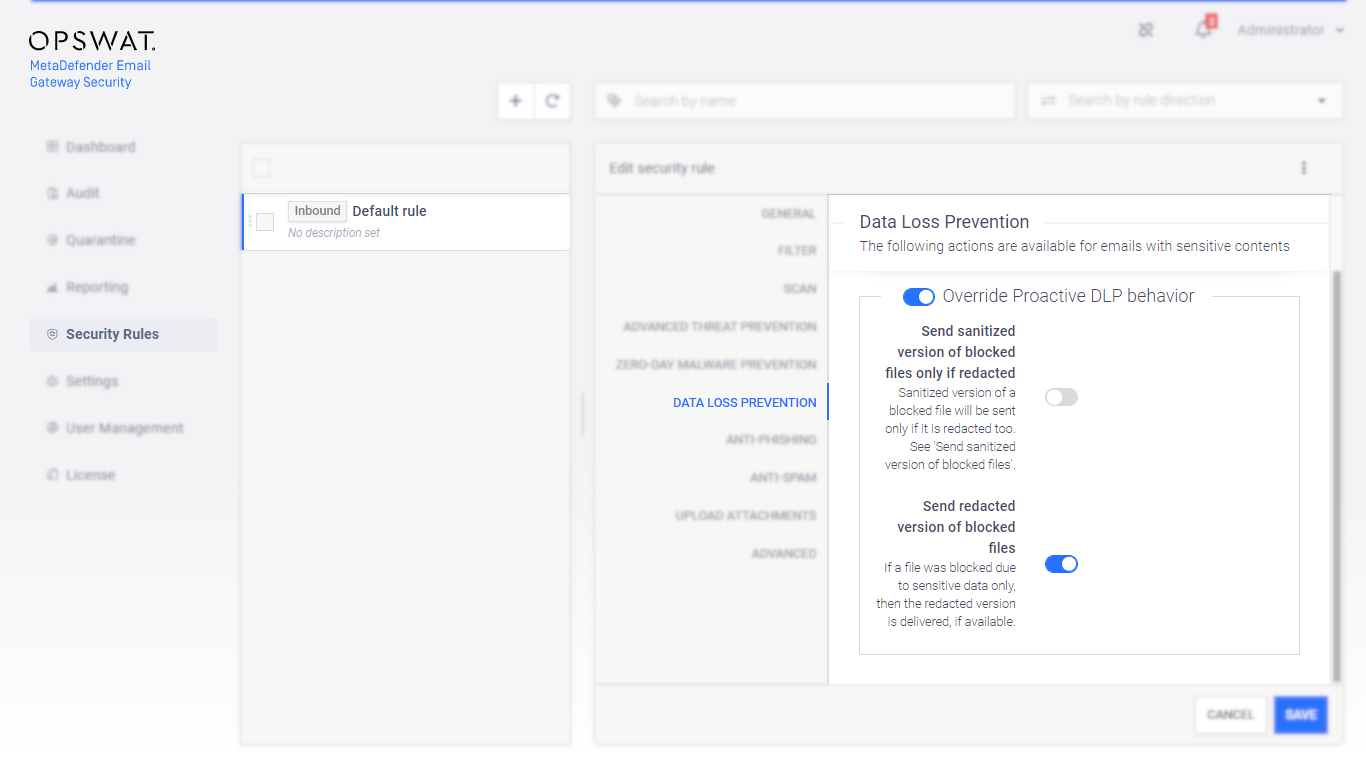
Send redacted attachments |
A new option is available for security rules to send redacted version of blocked files. Enabling this option will deliver redacted email contents - when redaction is available for the file type - if the contents were blocked due to sensitive data only. For details see 4.4. Policy. For details about redaction and file types supported by Proactive DLP see https://onlinehelp.opswat.com/dlp/2._Redact_sensitive_information.html. |
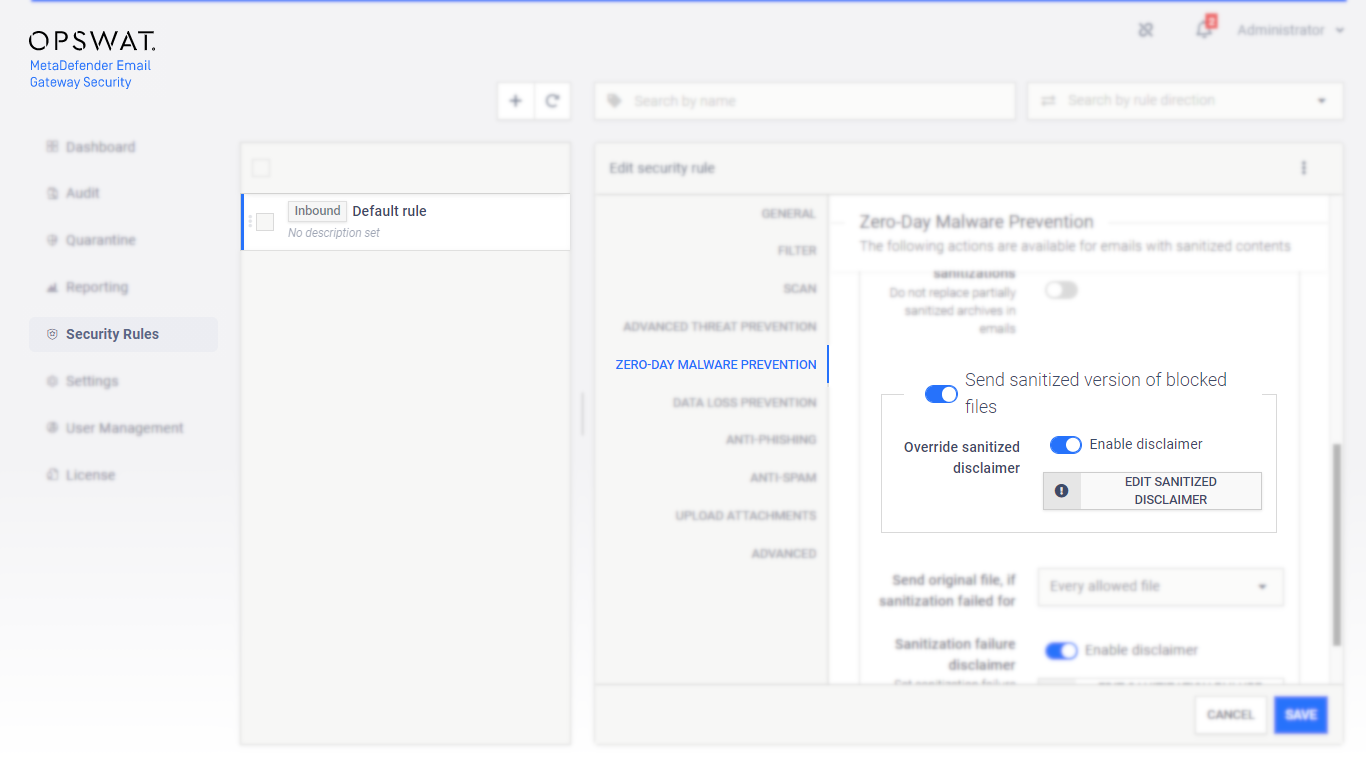
Custom disclaimer for sanitized components |
When Zero-Day Malware Prevention / Override sanitization behavior / Send sanitized version of blocked files is enabled, Email Gateway Security will deliver the sanitized version of blocked components within an email. A custom disclaimer may be set for this cases with a new option. |
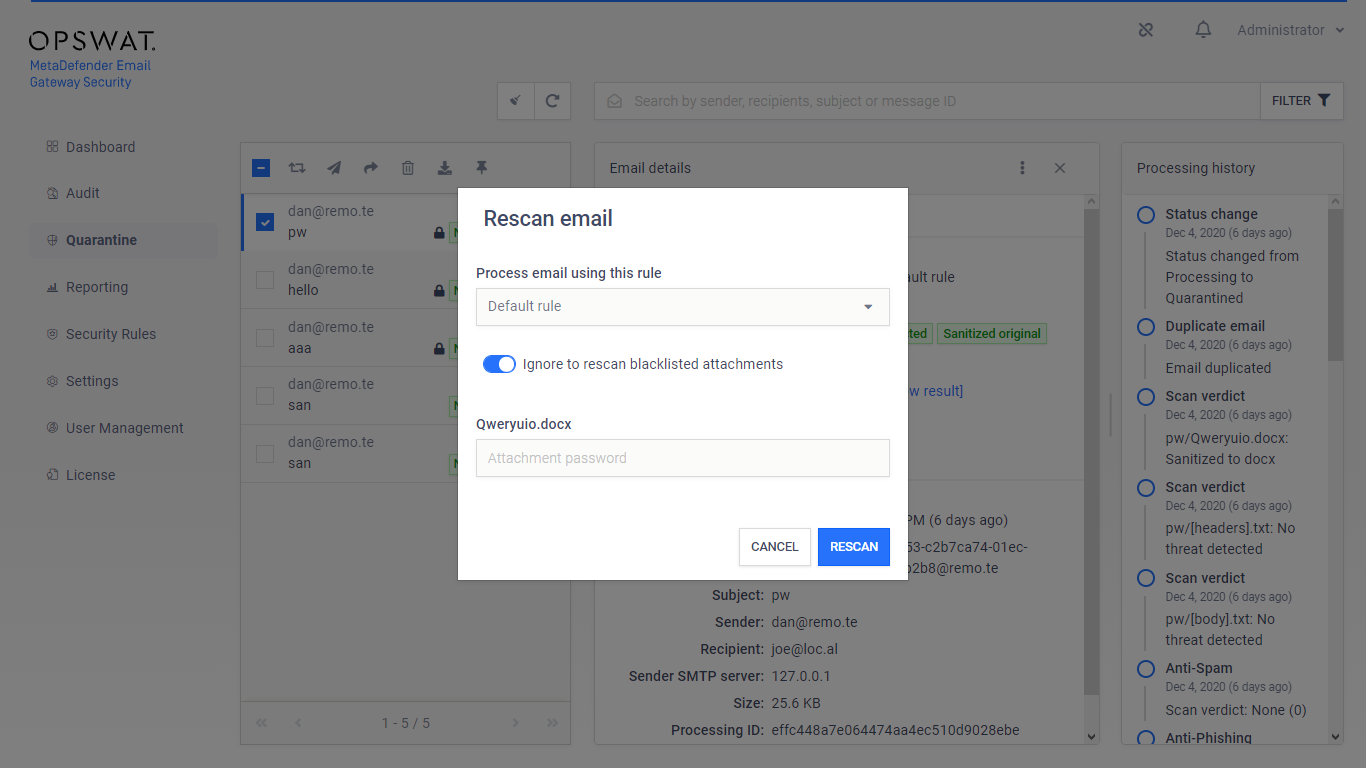
Ignore CDR’s blacklist |
If Deep CDR’s Blacklist unsupported file types option is enabled, it was not possible to rescan emails with password protected attachments as password protected files are blacklisted by Deep CDR. Email Gateway Security now provides an option to Ignore to rescan blacklisted attachments when initiating a rescan in the web management console. Enabling this option the email can be rescanned excluding the blacklisted contents. Public rescan not supported This feature is not available for recipients through the public rescan page, only for administrators via the web management console. For details see 5.3. Quarantine. |
Propagate TLS changes to the Public server address |
When TLS is enabled or disabled for the web management console (HTTP/HTTPS) under Settings > Security, this setting will now be propagated to the Public server address under Settings > General / Configuration. For details see 4.2. Transport Layer Security and 4.3. Settings. |
Notification when in monitoring mode |
A notification message will warn administrators when Email Gateway Security is in a monitoring mode (opposed to the protection mode that is recommended for production). For details see 4.3. Settings. |
Updated processing components |
Advanced Threat Prevention, Zero-Day Malware prevention and Data Loss Prevention components were updated to their latest versions. |
Fixed |
|
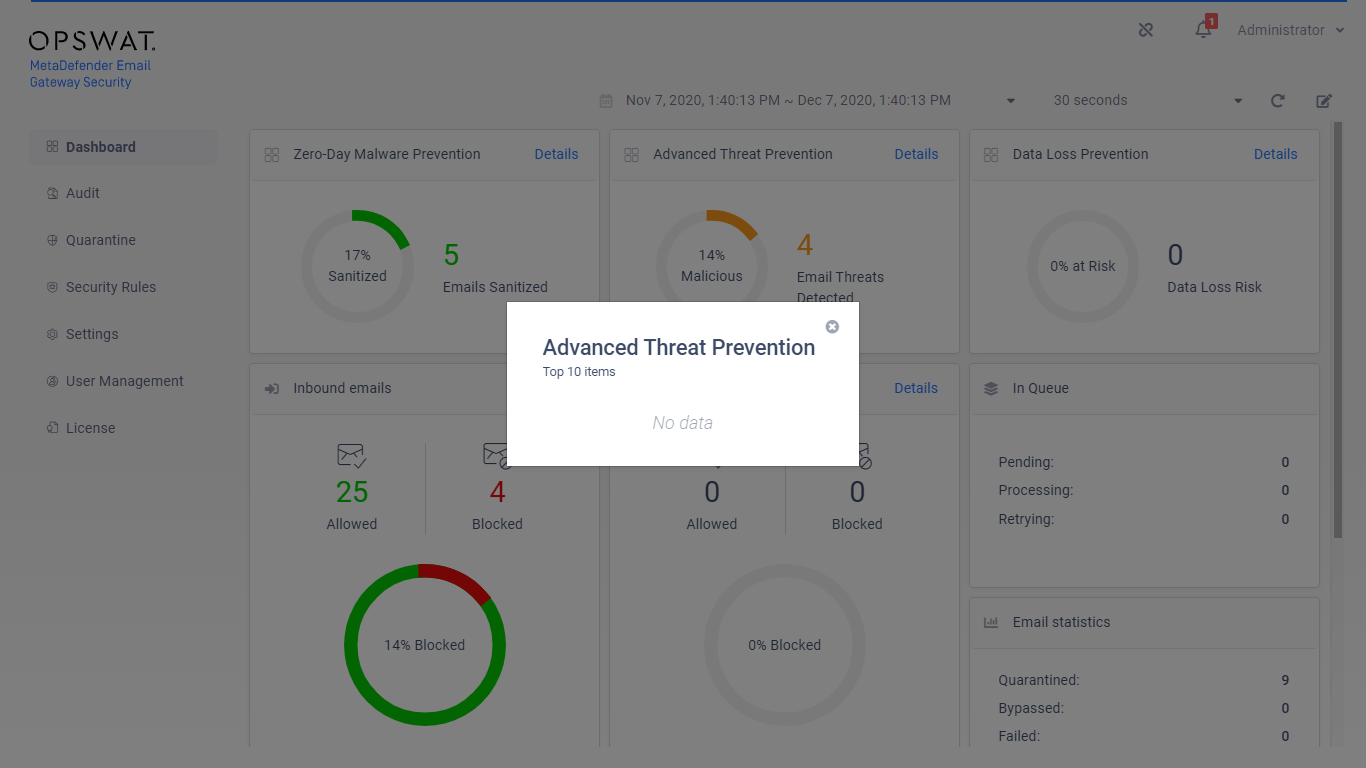
Advanced Threat Prevention's detail is empty |
Advanced Threat Prevention details were empty on the Dashboard even when there were certain advanced threats detected. Waiting for MetaDefender Core side fix Please note that this issue is caused by MetaDefender Core as it won’t report the threat name when it is inside an archive file (e.g. .zip or .docx, etc. files). Until it is fixed, - as a workaround - Email Gateway Security will display the Archive embedded threat text for these cases. |
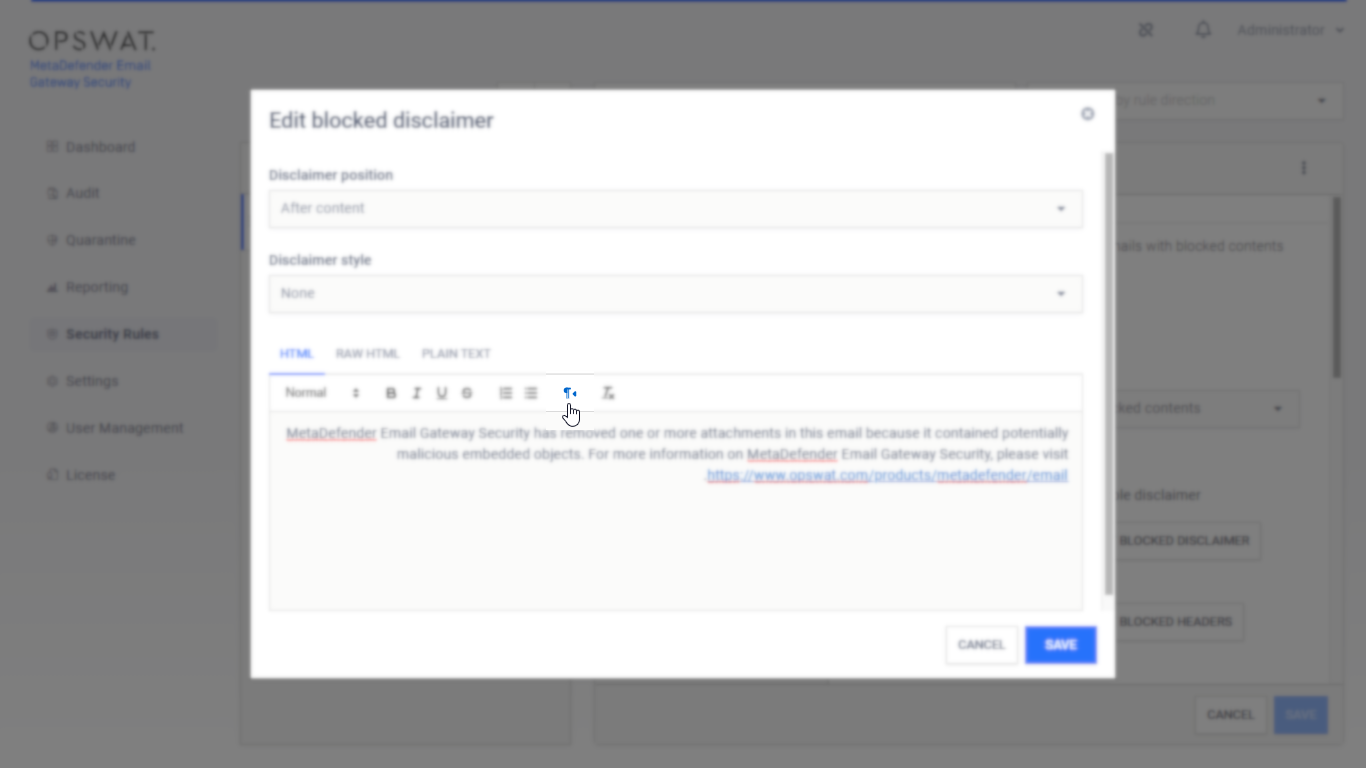
Right-to-left disclaimers |
Even when the browser and the OS were set to a RTL language, disclaimers sometimes were still aligned to left. The disclaimer editor in Email Gateway Security now has a function to enforce the disclaimer to be aligned to right. For details see 4.4.1. Disclaimers. |
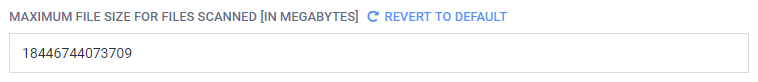
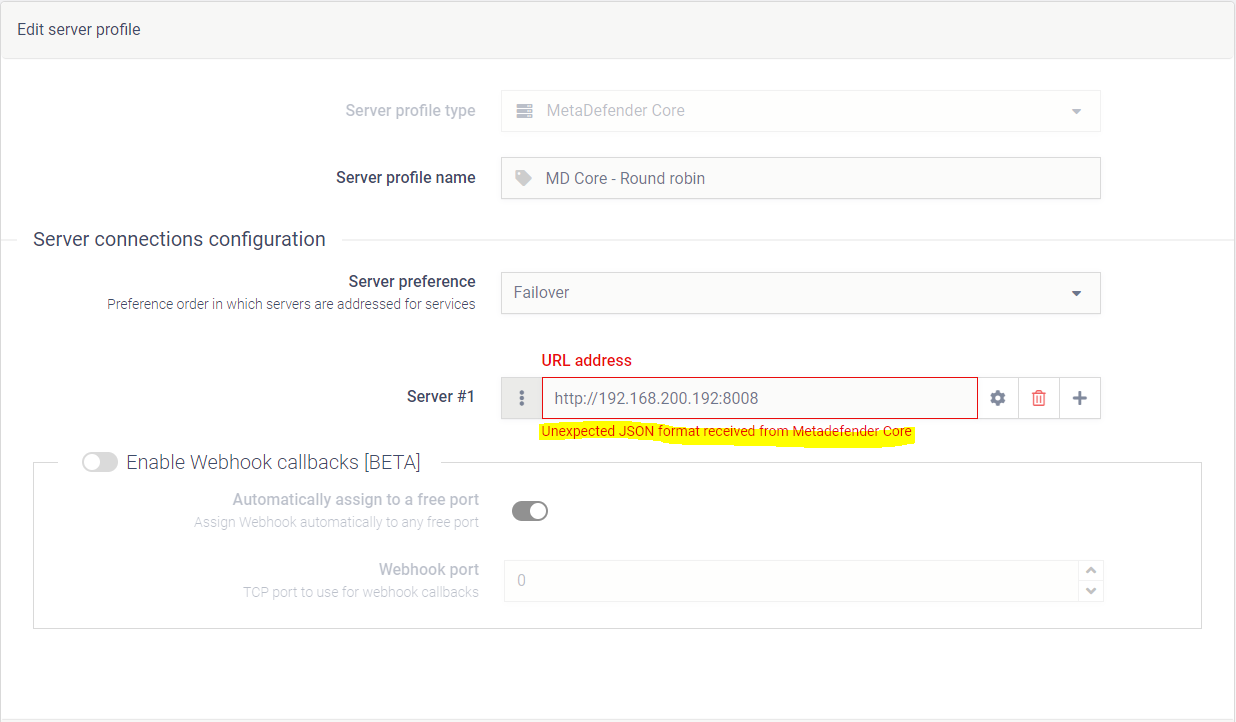
Unexpected JSON format |
When the MAXIMUM FILE SIZE FOR FILES SCANNED value was set over a limit on MetaDefender Core (over 9 223 372 036 854 megabytes) then adding that Core sever to a server profile, or fetching the Core side rules of that Core failed with the Unexpected JSON format received from Metadefender Core error message. |
Rescan page in Internet Explorer |
As a hotfix, Email Gateway Security can support Internet Explorer version 11 for the public rescan page. Internet Explorer is not supported Please note that in general Internet Explorer remains not supported in Email Gateway Security. On request hotfix only This feature is available as a hotfix only on request, and is not available in the product when installed using the public installer. |