Information regarding certificates
Using a certificate signed by a Certificate Authority
Please follow instructions from CA on how to install your certificate to your server if you have not already done so.
After making sure a valid certificate is installed, the user needs to export the certificate in PKCS12 format and afterwards, convert it to the PEM format, using a tool such as openssl.
Instructions for exporting an existing certificate
-
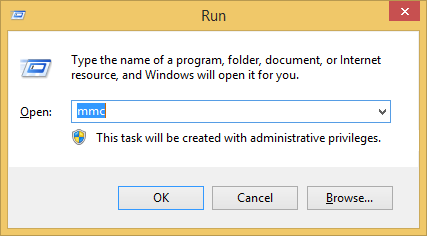
Open "mmc" in windows Run
-
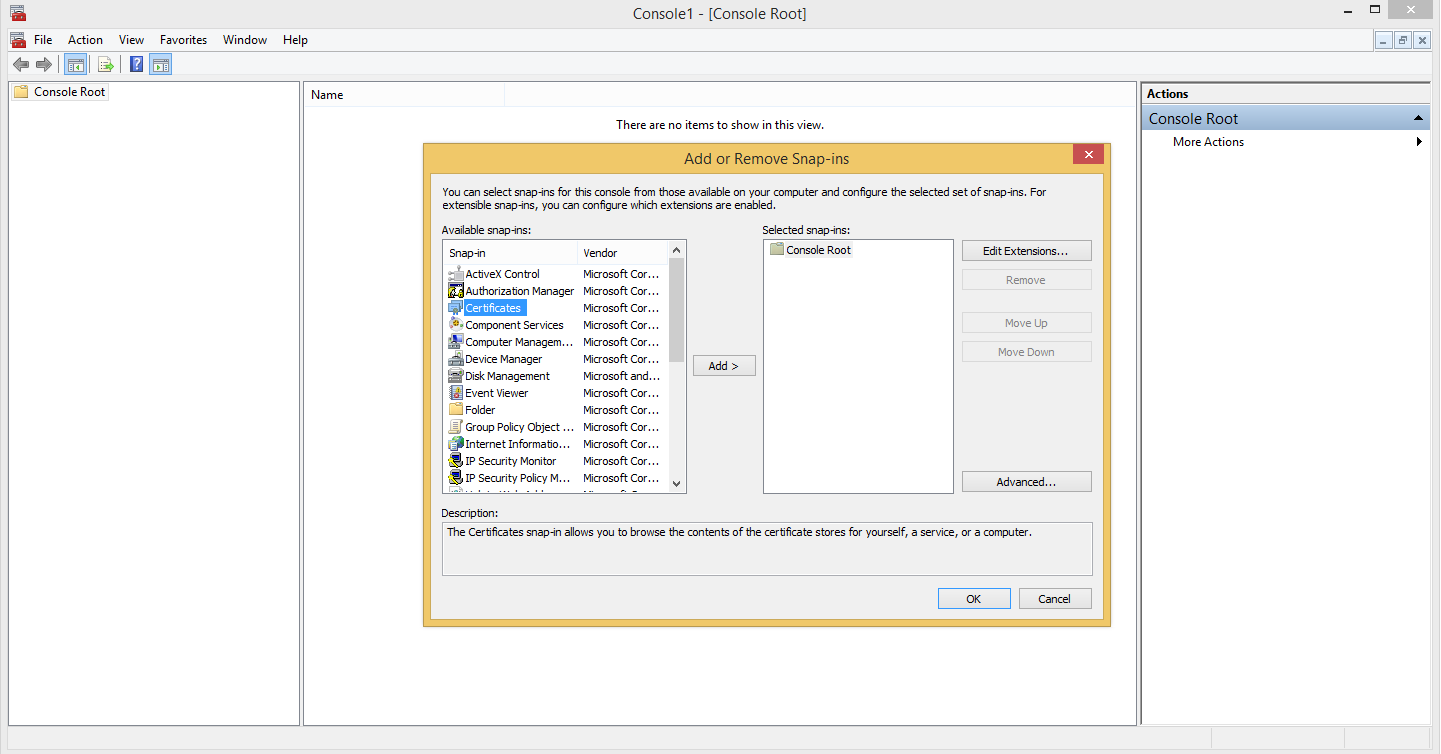
Select File → Add/Remove Snap-ins
-
Add Certificates → Choose Computer Account → Click next → Click Finish → Click OK
-
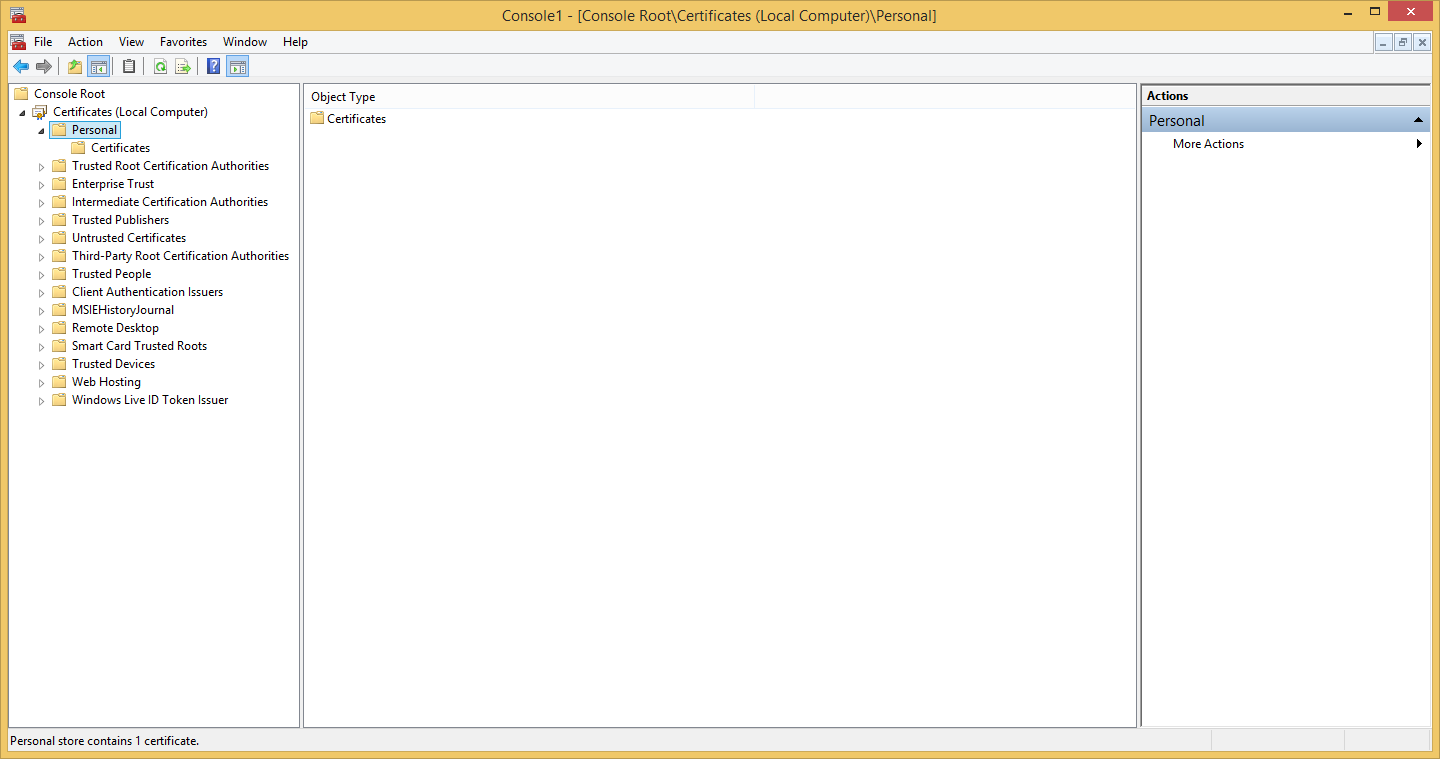
Navigate to whichever folder the certificate is installed in.
-
Right click the certificate and select All Tasks → Export in order to launch the Certificate Export Wizard.
-
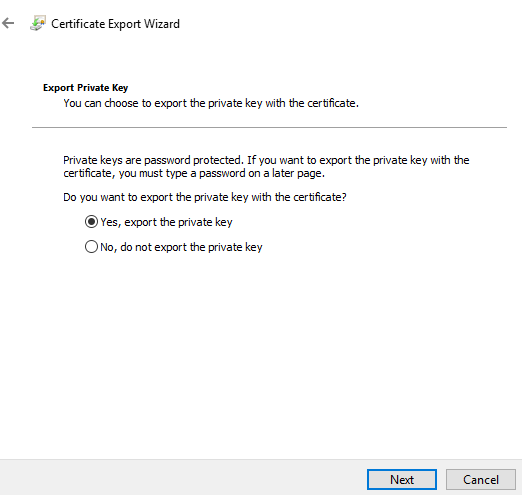
When asked, choose to export the private key with the certificate.
-
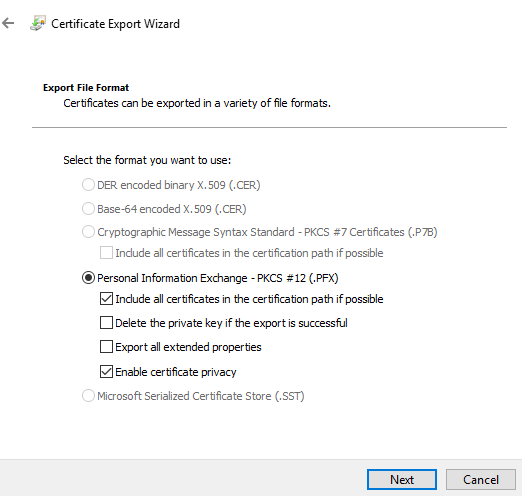
Choose to save the certificate and private key in the PKCS12 (.pfx) format.
-
You can opt to protect the private key via selecting security principal or by password.
We will opt for password in this guide.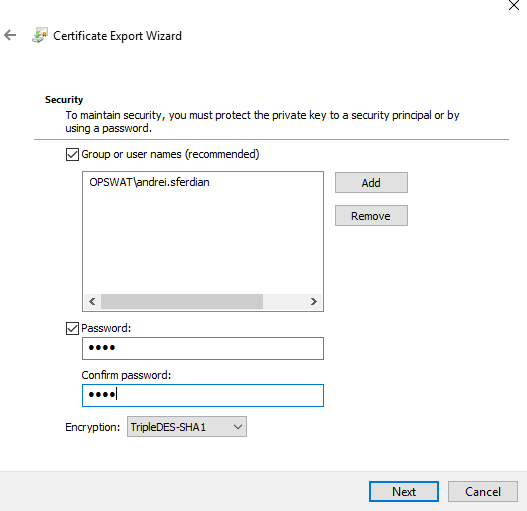
-
Enter a certificate name then click Next and Finish.
Converting a PKCS12 certificate to PEM
-
(Optional) Install openssl command line utility
-
Open a Command Prompt and type the following command (replacing the certificate names and password):
openssl pkcs12 -intestcert.pfx -out testcert.pemEnter Import Password:Enter PEM pass phrase:Verifying - Enter PEM pass phrase:Import Password is the password used to encrypt the PKCS12 private key.
PEM pass phrase is the password used to encrypt the key in the resulting PEM format.The entered passphrase must be saved in a file as plain text, to be used when configuring TLS/SSL.
If the user wishes no passphrase for the private key then the -nodes argument must also be passed.openssl pkcs12 -intestcert.pfx -out testcert.pem -nodesEnter Import Password:
Generating a self-signed certificate with openssl
-
Open a Command Prompt and type the following command (replacing the inputs with valid local paths):
openssl req -x509 -newkey rsa:4096 -keyout key.pem -out cert.pem -days 365Generating a RSA private key......................................................................................................++++.........................................................................................................................................++++writing new private key to'key.pem'Enter PEM pass phrase:Verifying - Enter PEM pass phrase:-----You are about to be asked to enter information that will be incorporatedinto your certificate request.What you are about to enter is what is called a Distinguished Name or a DN.There are quite a few fields but you can leave some blankFor some fields there will be a default value,If you enter'.', the field will be left blank.-----Country Name (2 letter code) [XX]:State or Province Name (full name) []:Locality Name (eg, city) [Default City]:Organization Name (eg, company) [Default Company Ltd]:Organizational Unit Name (eg, section) []:Common Name (eg, your name or your server'shostname) []:Email Address []:Note: The entries starting from "Country Name" can be left empty.