Pre-configured Settings
The product supports partly automated in order to help reduce user interaction.
The automation can be split to two steps on a high level:
-
Pre-configuration
-
Automation
1. Pre-configuration
We setup the desired configurations following the INI file format:
-
file name: mdd_ignition.ini
-
file path: MetaDefender Drive/conf
INI files are simple text files with a basic structure composed of sections, keys, and properties
-
Sections, Keys and Properties are case sensitive
-
If there are duplicated Keys defined, the latest property is used
|
Section |
Key |
Property |
Description |
|
eula |
accepted |
true |
Skip EULA screen, shows:
|
|
any value except true |
Show EULA screen |
||
|
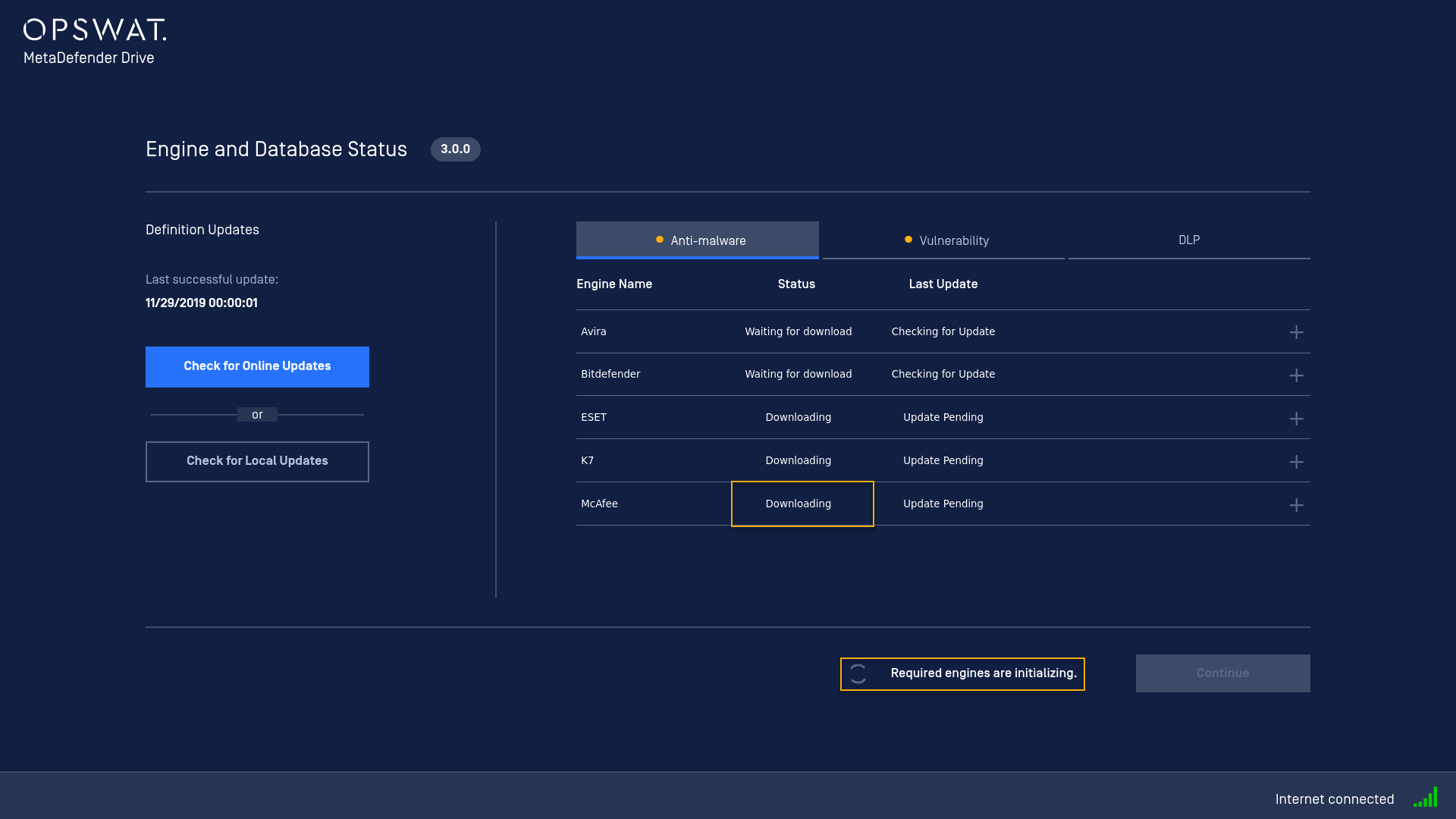
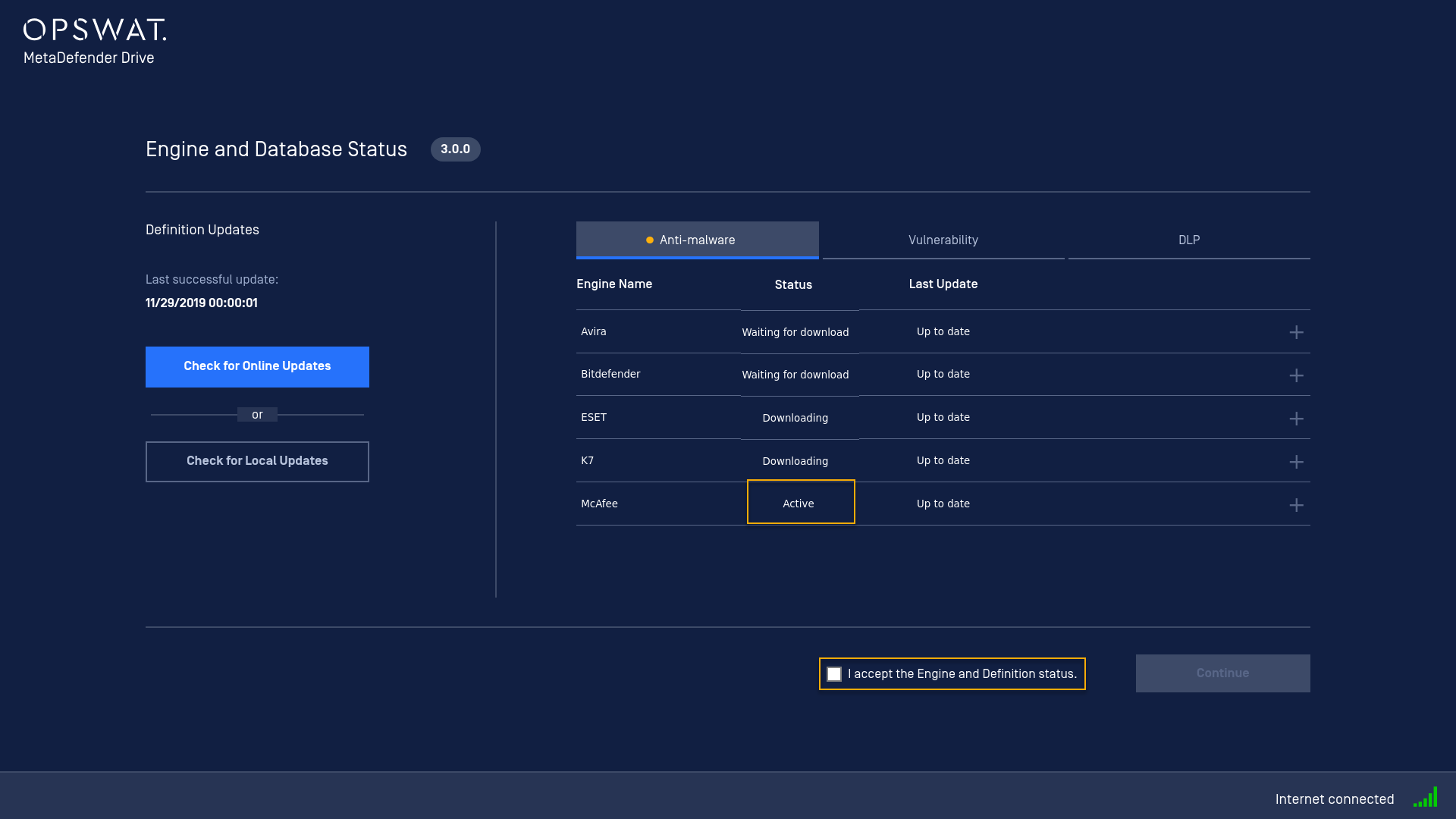
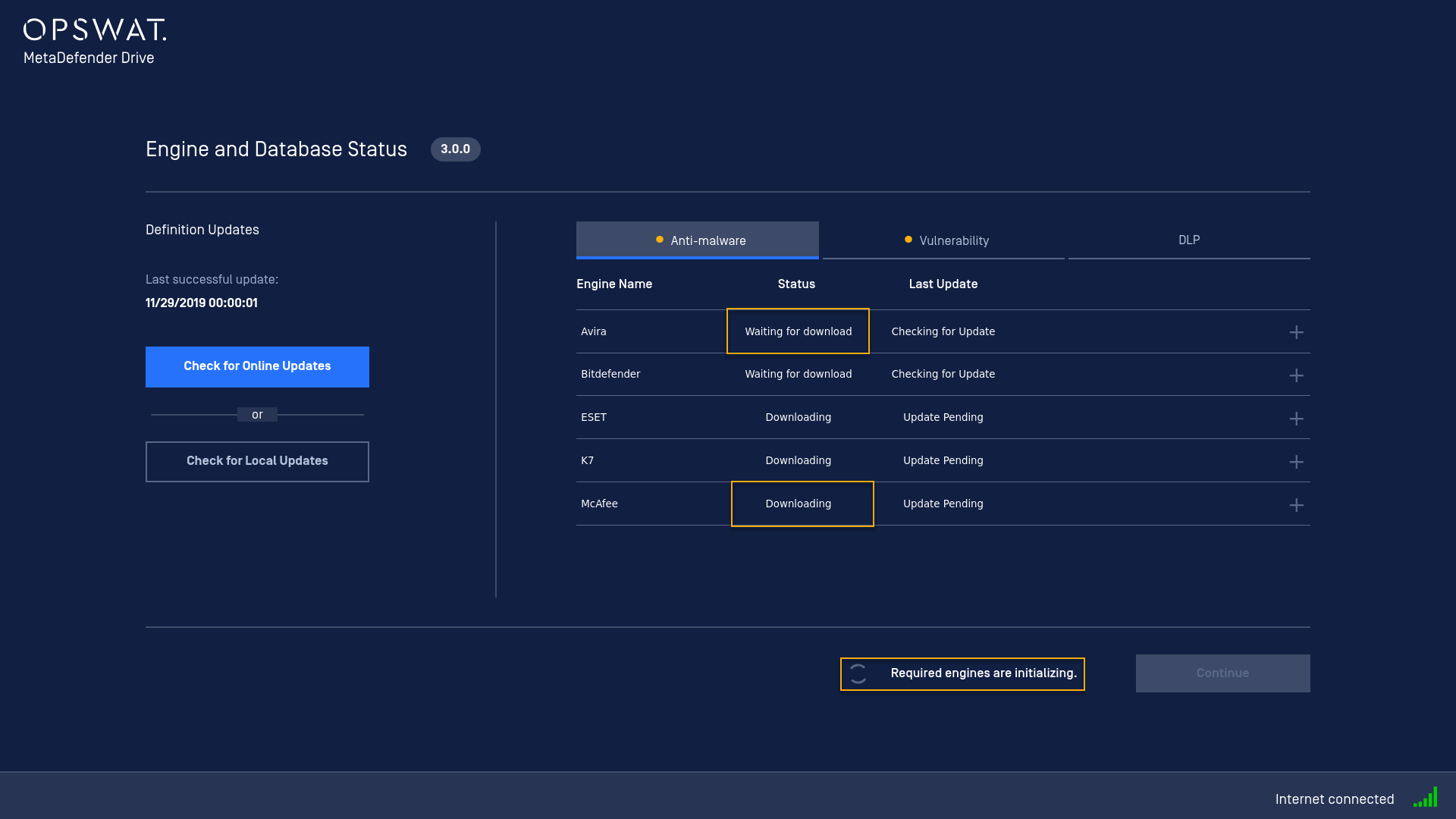
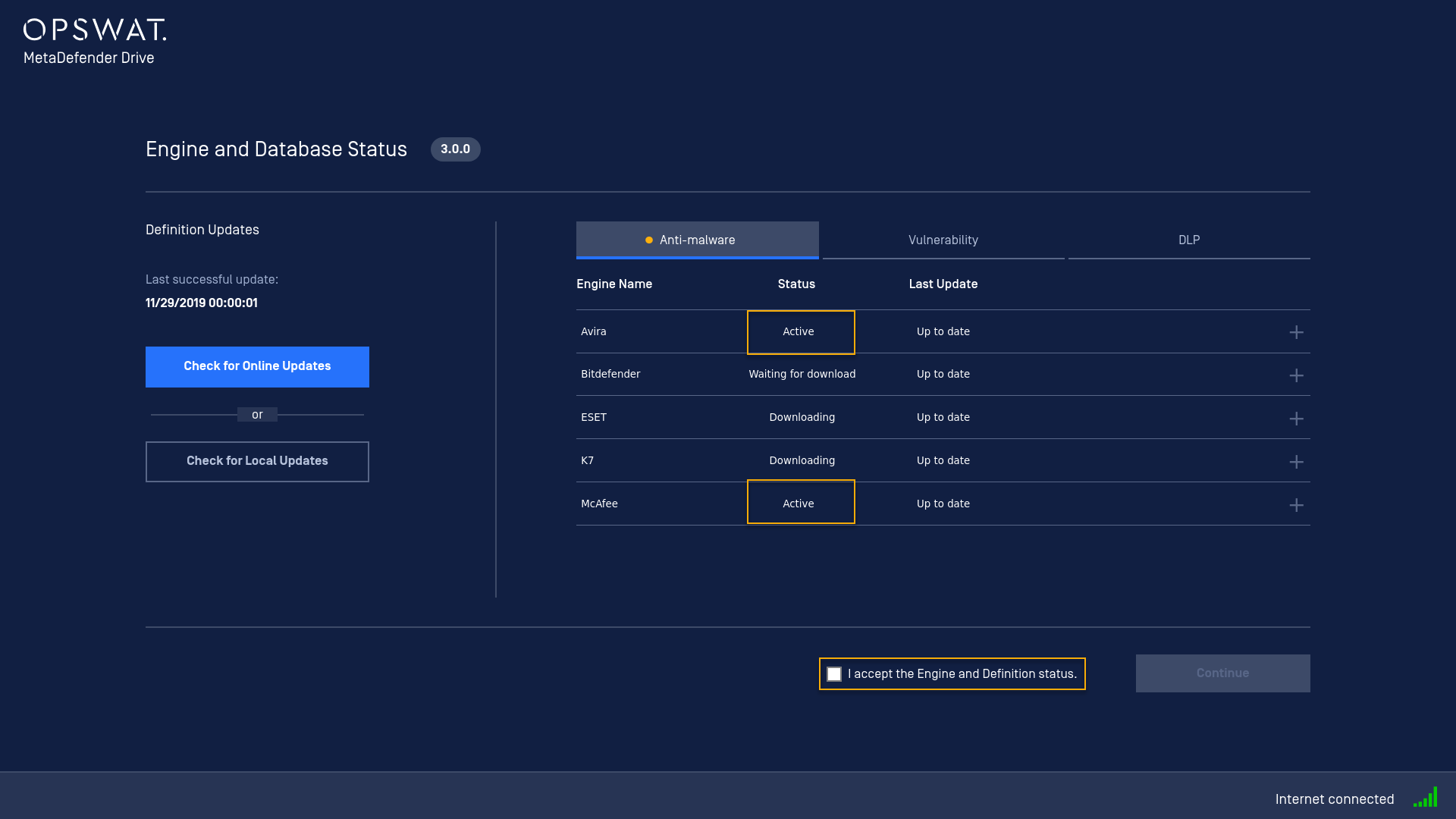
engine |
required |
all |
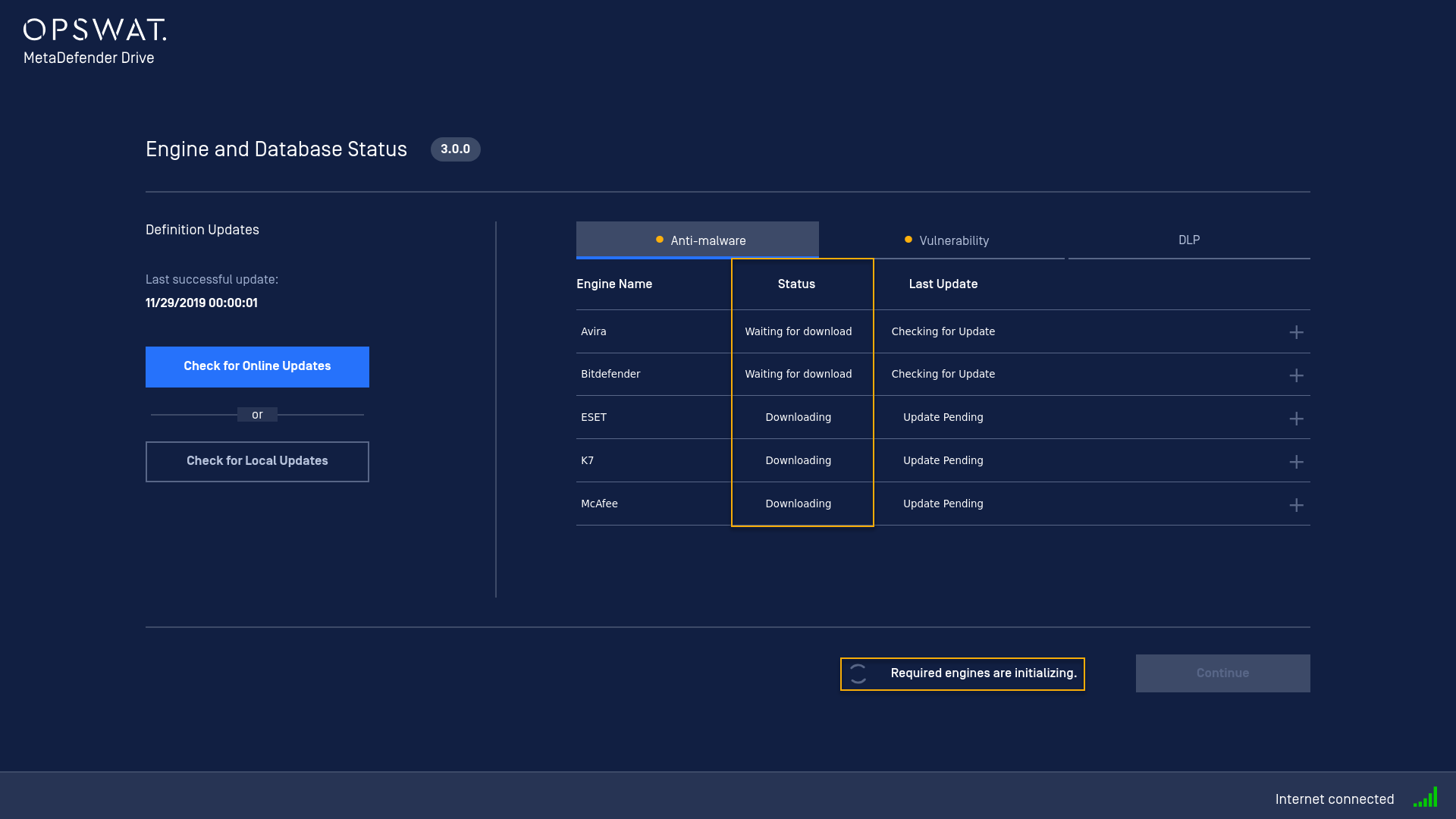
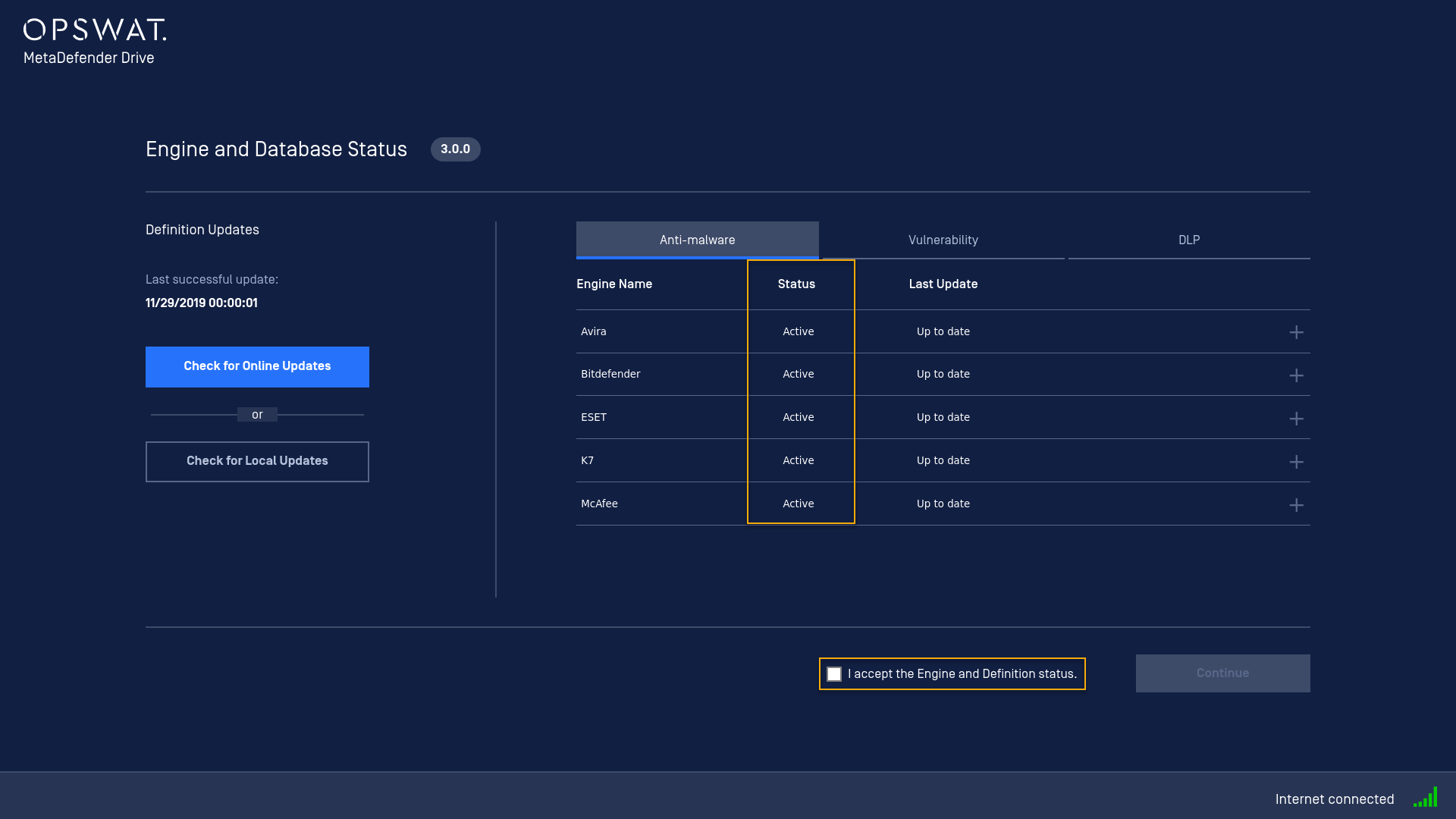
At Engine status screen:
|
|
<engine_name> e.g: required=McAfee Single choice <engine_name> is case sensitive |
At Engine status screen:
|
||
|
<engine_name1>,<engine_name2> e.g: required=McAfee,Avira Multi choice separates by , |
At Engine status screen:
|
||
|
report |
json |
true |
No effect since json is mandatory |
|
false |
No effect since json is mandatory |
||
|
|
true |
In Settings> Preferences, PDF checkbox is checked |
|
|
false |
In Settings> Preferences, PDF checkbox is un-checked |
||
|
txt |
true |
In Settings> Preferences, TXT checkbox is checked |
|
|
false |
In Settings> Preferences, TXT checkbox is un-checked |
||
|
disk |
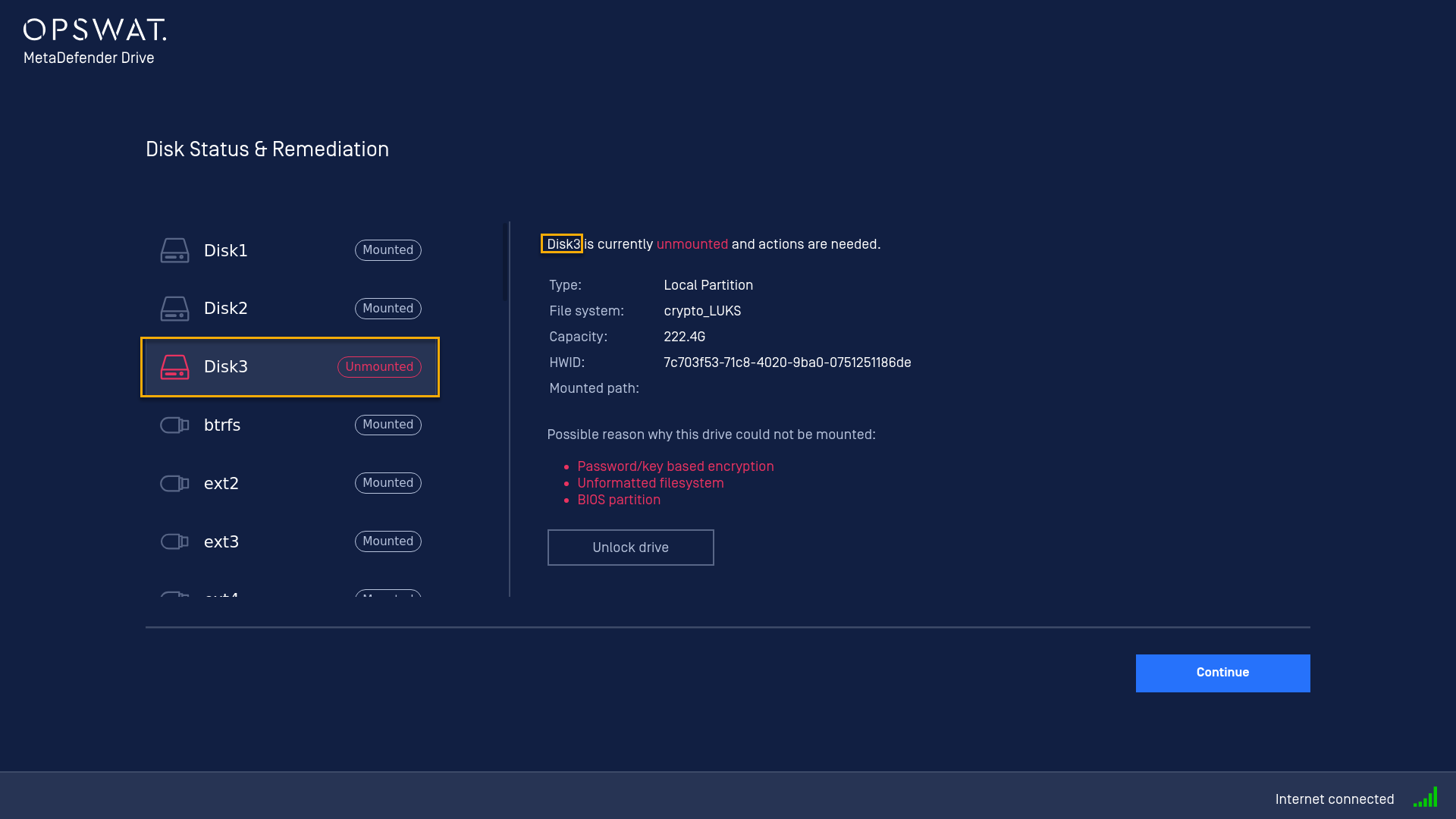
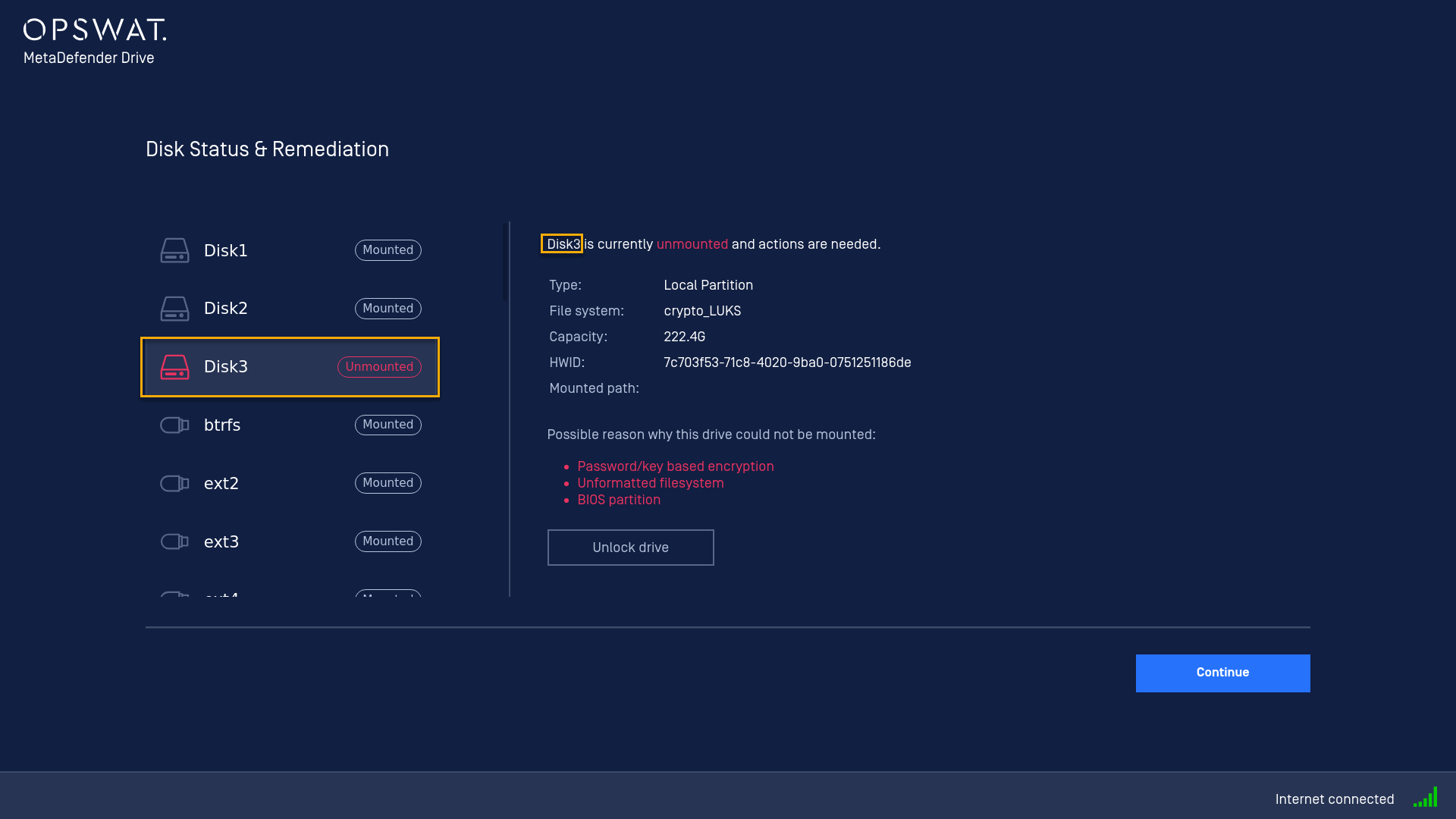
<driveID> EXAMPLE Disk3 Please access to Disk Status & Remediation to gain the information regarding to disks |
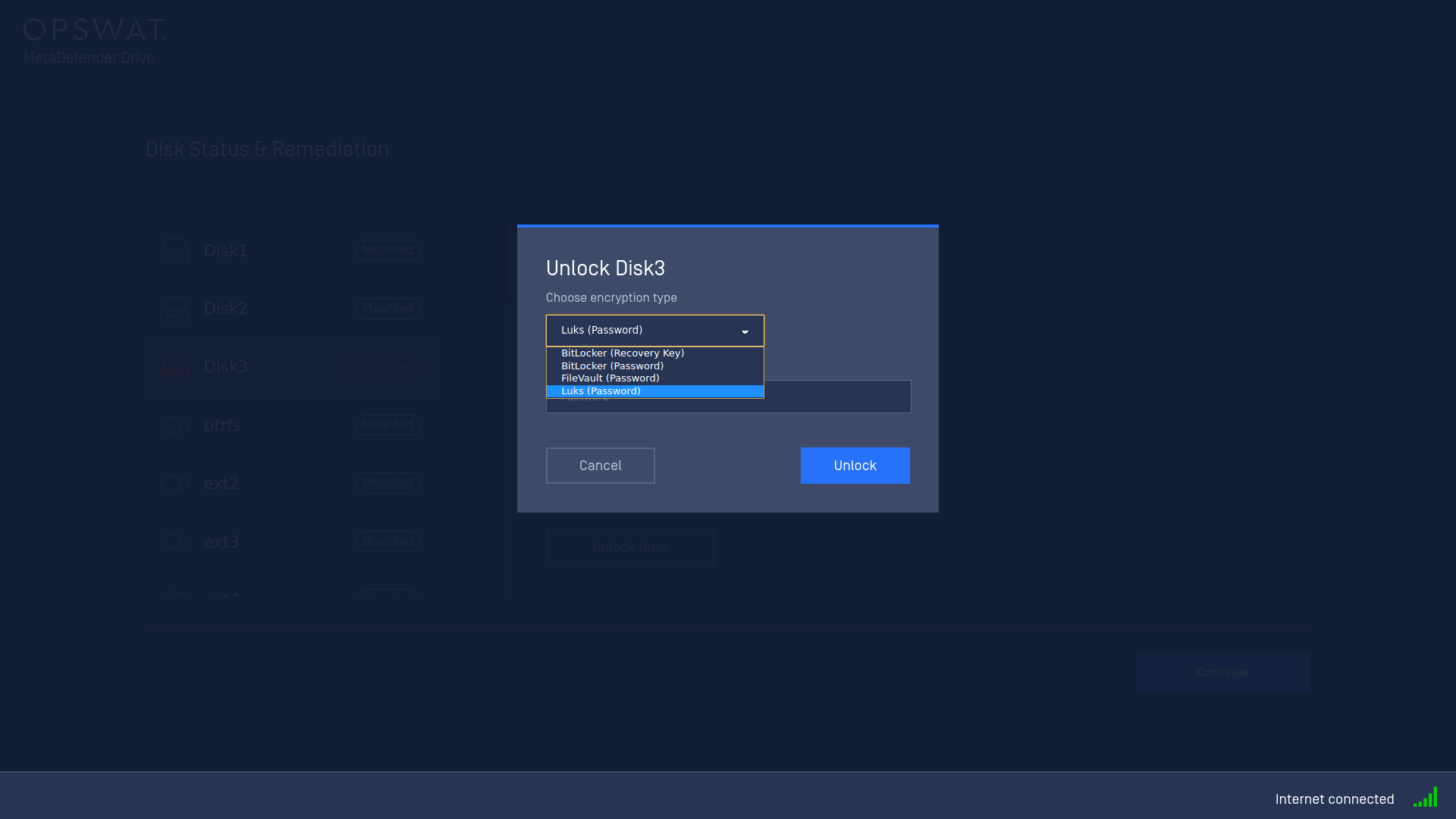
-e<encryption_type> -p<passowrd> -k<key> EXAMPLE Disk3=-eLuks (Password) -p12345678 Please access to Disk Status & Remediation> Disk3> Unlock > Encryption Type to gain the information regarding to encryption type |
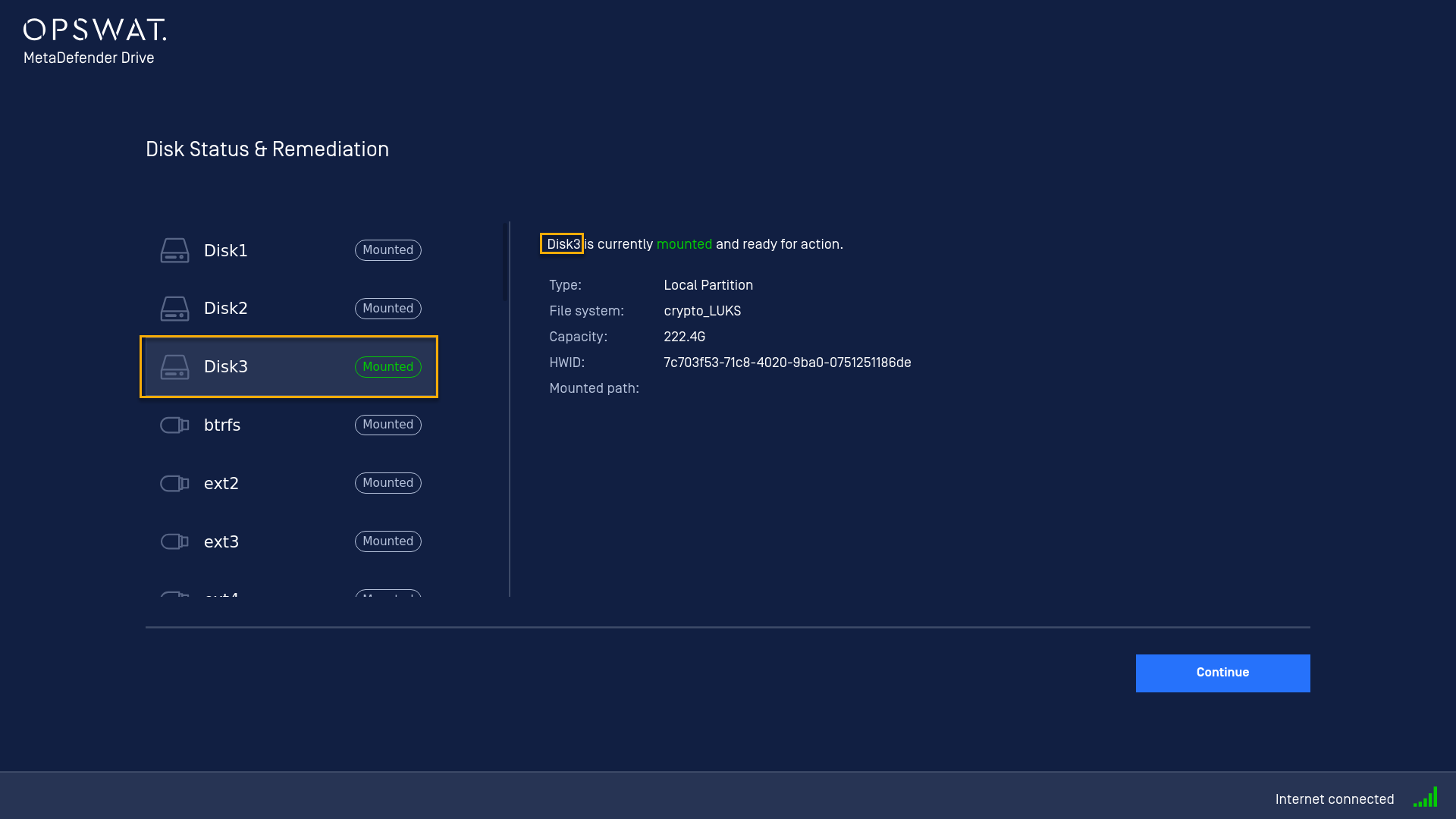
Auto unlock<driveID> based on provided <encryption_type>, <password> or <key> EXAMPLE Disk3 is locked by Luks (Password) Disk3 is auto unlocked with provided password This auto unlock result is recorded at MetaDefender Drive/conf/output |
|
scan |
full |
true |
Perform full scan from all unlocked disks Then paths key from custom scan will be skipped |
|
false |
Does not perform full scan |
||
|
paths |
/media/<driveID1>/ |
Perform custom scan with single target |
|
|
/media/<driveID1>,/media/<driveID2>,/media/<driveID3>/ |
Perform custom scan with multiple targets separates by , |
||
|
useDeviceIntegrity |
true |
Turn on scan option Device Integrity |
|
|
false |
Turn off scan option Device Integrity |
||
|
useMultiscan |
true |
Turn on scan option Malware Multiscan |
|
|
false |
Turn off scan option Malware Multiscan |
||
|
useVulnerability |
true |
Turn on scan option Vulnerability Analysis |
|
|
false |
Turn off scan option Vulnerability Analysis |
||
|
useDlp |
true |
Turn on scan option DLP |
|
|
false |
Turn off scan option DLP |
||
|
shutdownAfter |
true |
Turn on scan option Shutdown computer after processing. |
|
|
false |
Turn off scan option Shutdown computer after processing. |
||
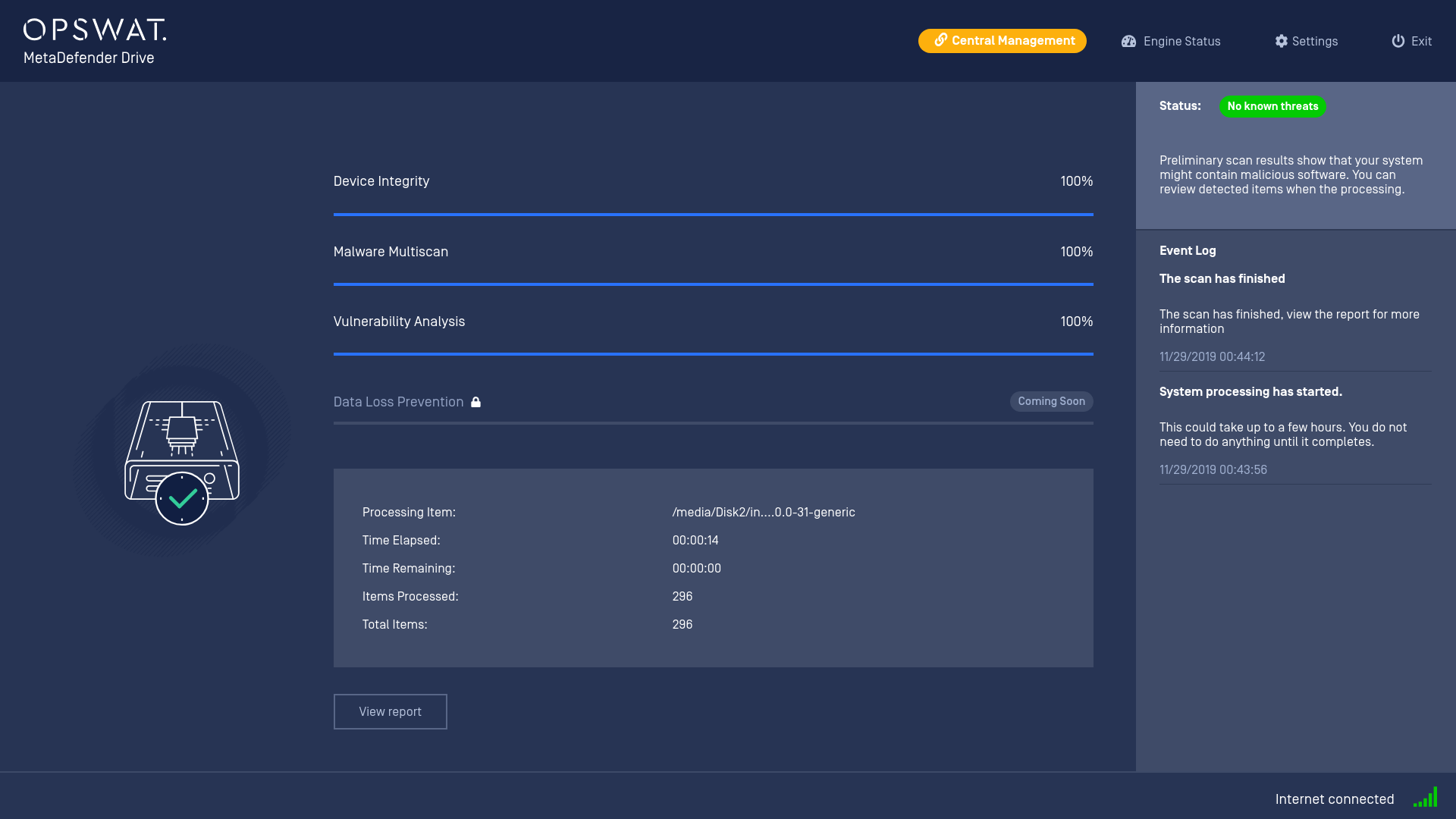
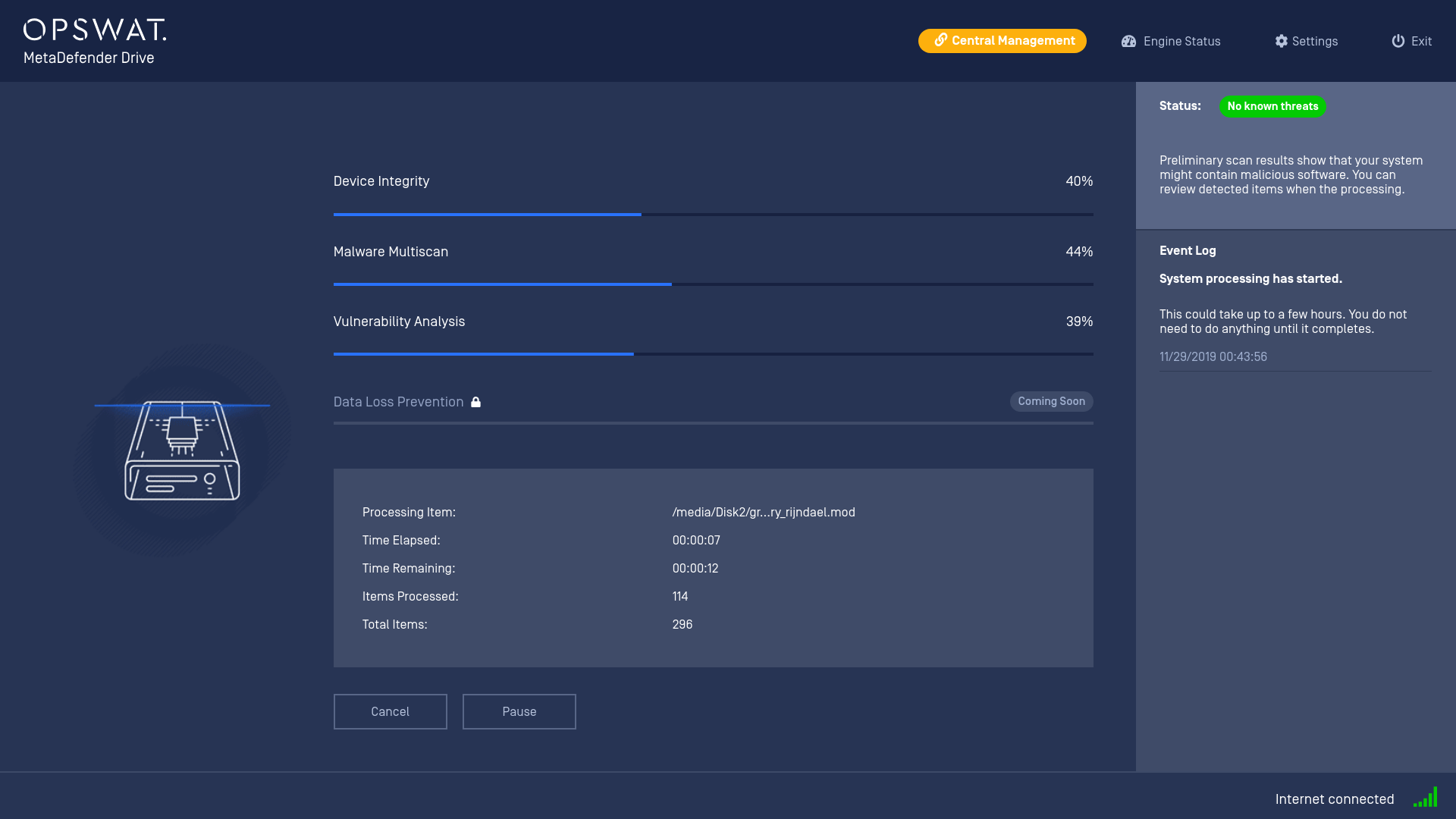
2. Automation
After setup the pre-configuration for example as below:
[eula]accepted=true[engine]required=all; -p[censored]: please input password to decrypt Luks there[disk]Disk3=-eLuks (Password) -p[censored][scan]paths=/media/Disk1,/media/Disk2useMultiscan=trueuseVulnerability=true[report]json=falsepdf=truetxt=falseWe could have an automation process from EULA accepted screen to waiting for all required engines be activated, then auto decrypt Disk3 with provided password and finally start the custom scan automatically. Lets see!
And the report formats is setting according to our pre-configuration except json still checked (of course, because it’s not allowed to change json)mdd_ignition.mp4