1.5 Configuring through Central Management
Multiple MetaDefender Clients can be configured from a Central Management.
Some changes will take effect at the next restart of Client.
To point MetaDefender Client to Central Management either the Client is installed with the Central Management parameters or the settings are set on the Client settings page.
Refer to the Central Management documentation for further details on how to setup managing MetaDefender Clients.
When a Client is centrally managed, the settings will no longer be allowed to be changed on the Client itself, only through Central Management.
|
Settings |
Description |
|
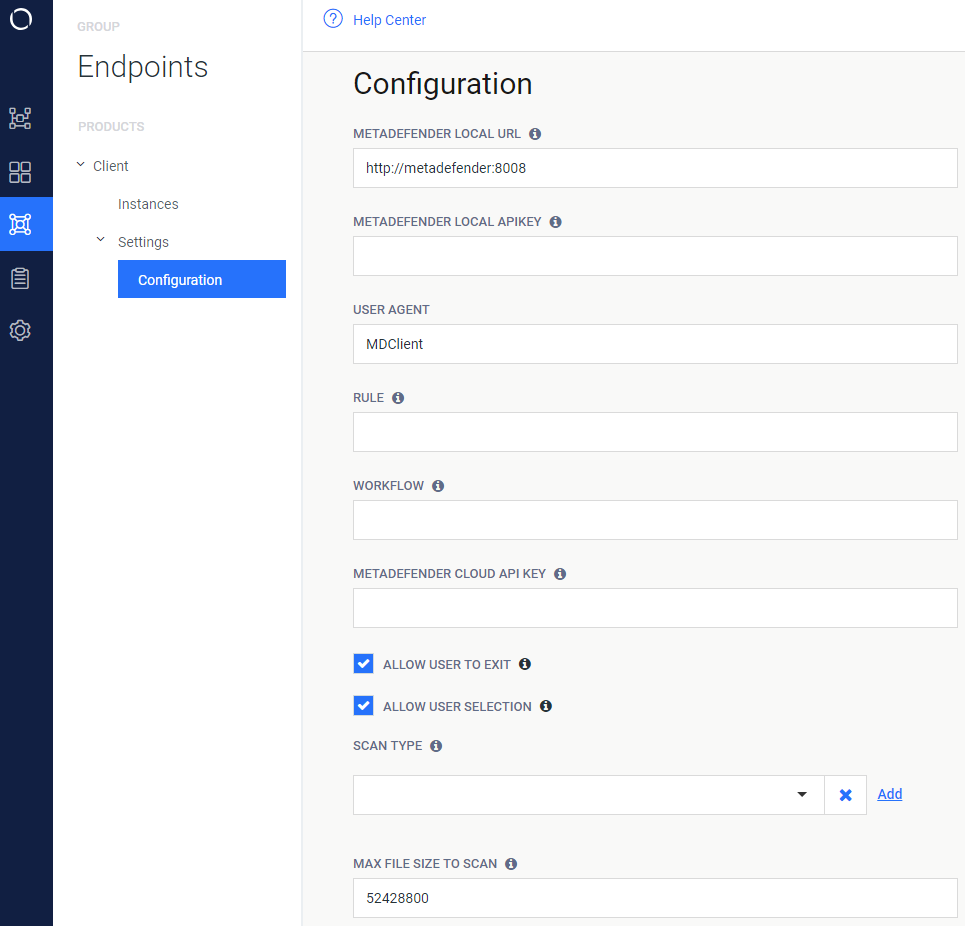
MetaDefender Local URL |
URL of the MetaDefender used to process files |
|
MetaDefender Local API Key |
API Key used for processing files with MetaDefender v3 (if one is set) |
|
User Agent |
The user agent Client provides to MetaDefender for rule/workflow security restrictions |
|
Rule |
Specifies the security rule Client should use for MetaDefender v4 |
|
Workflow |
Specifies the workflow profile Client should use for MetaDefender v3 |
|
MetaDefender Cloud API Key |
API Key used for processing files with MetaDefender Cloud |
|
|
|
|
Allow User to Exit |
Allow the user to exit through the UI |
|
Allow User Selection |
Allow the user to select scan type through the UI |
|
Scan type |
The type of scan that is performed if "Allow User Selection" is not checked |
|
Max File Size to Scan |
The maximum size of the file to process with MetaDefender (in Bytes) |
|
Disable Checking Hash |
Never perform hash lookups, always upload files to MetaDefender for processing |
|
Engines to Exclude from Results |
Engine(s) to not be included in the final MetaDefender result output |
|
Log File Location |
Path to store the location for an auto-generated log |
|
|
|
|
Enable Media Drive Protection |
All USB/CD/DVD media inserted into the endpoint will be blocked and require processing by MetaDefender before use |
|
Hide Locked Drive Warning |
Disable displaying the warning message of a blocked drive upon insertion |
|
Hide Drive Unlock Option |
Disallow a user from unlocking a blocked drive |
|
Hide Drive Browse Option |
Disallow a user from copying files from a blocked drive to the system |
|
Hide Drive Copy Option |
Disallow a user from copying files from the system to a blocked drive |
|
Drive Unblocking on Error |
Drive unblocking can proceed in the event of MetaDefender server errors |
|
Copy Files from Drive on Error |
Copying files from the drive can proceed in the event of MetaDefender server errors |
|
Copy Clean File Location |
The folder to copy clean files to, from the removable media in Browse File mode |
|
Maintain Directory Structure for Copy |
Maintain the directory structure of files on the media in the copy to destination |
|
|
|
|
Use File Sanitization |
Check for a sanitized copy of the file generated by MetaDefender |
|
Copy Only Sanitized File, Do Not Copy Original |
Dictates if the original file will be removed, or keep it alongside the sanitized copy |
|
|
|
|
UI Display Language |
Language the UI will be displayed in |
|
|
|
|
Upload Allowed/Blocked Files to MetaDefender Vault |
Allowed/Blocked files will be uploaded to MetaDefender Vault |
|
URL |
URL of the MetaDefender Vault server to upload files to |
|
Authentication Token |
Vault admin authentication token used for uploading files |
|
Always Upload to a Vault Guest Account |
Uploads will be sent to a newly created guest account |
|
|
|
|
Media Manifest |
Client will utilize a Media Manifest existing on the media inserted |
|
Block All Files Not Found on Manifest |
Any file not found in the Media Manifest will be immediately blocked and Client will not attempt to process the file with MetaDefender |
|
Days to Trust Manifest |
The maximum days to use a Media Manifest result |
|
Client Admin Password Hash |
Hashed administrative password. This will be used to uninstall the Client or disable USB blocking. The input to this field MUST be in the format <salt>:<iterations>:<password hash>. Use the "–hash_password" command line option for Metadefender.exe to generate a password hash. See section 2.1 Generating and using the Administrator Password for more information |
|
Allow Disabling of USB Blocking |
Allow the user to use the Admin Password to disable USB blocking until next restart |